How to Use Your iPhone as a Webcam with Continuity Camera in macOS Ventura
Continuity Camera lets you use your iPhone as a webcam with your Mac.
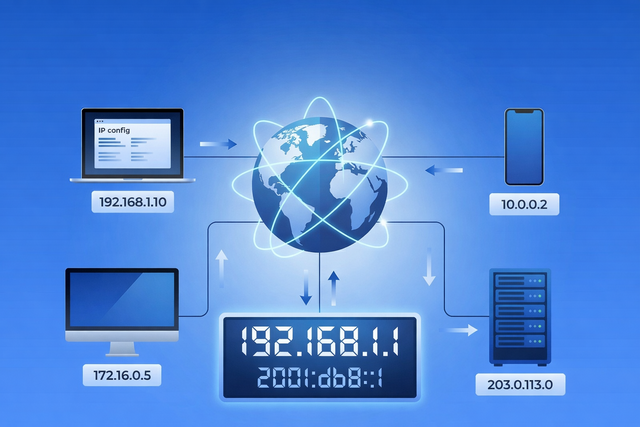
Every time you open a website, stream a video, send an email, or connect to Wi-Fi, your device relies on an IP address. You rarely see it, and most of the time you probably do not think about it. But it plays a quiet, important role in how the internet works. Your IP address helps...

Apple has just released critically urgent security updates—including macOS Sequoia 15.4.1 and iOS 18.4.1—to address two zero-day vulnerabilities that have been actively exploited in...

Macs have a strong security foundation. That’s true — and it’s worth appreciating. But “safer than” doesn’t mean “safe from.” Modern Mac threats don’t...
Is your Mac running slow? Here's how to diagnose and fix performance issues and get your Mac to run faster.
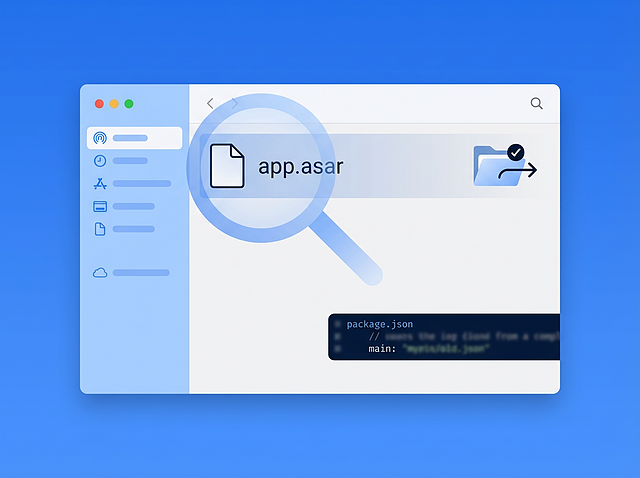
Executive Summary In March 2026, Intego Antivirus Labs investigated a macOS malware campaign delivering the OSX/Amos stealer. During analysis, the infection chain led from stripped Mach-O binaries and heavily obfuscated shell scripts to an unusual final payload that appeared...

Continuity Camera lets you use your iPhone as a webcam with your Mac.
Check out what's new in macOS Ventura: Stage Manager, new features in Mail and Messages, new security and privacy...
Learn about the many useful new features in Apple's Mail and Messages.
The System Settings app replaces System Preferences in macOS Ventura, and features a totally new look.
A new malware attack framework, Alchimist, can be used to infect and remotely control macOS, Linux, and Windows computers....
Apple announced new iPads this week, and now the iPad line is confusing. We look at what this means...
This month, Intego celebrates its twenty-fifth anniversary. Founded in 1997, Intego’s primary focus has always been protecting Mac users...
Stage Manager is an interesting new way of working with windows on macOS Ventura and iPadOS 16.
Apple's new crash detection feature in iPhones is creating false positives on roller coasters. Researchers have found a way...
Rumors started circulating last weekend that the German airline Lufthansa might be banning Apple AirTag tracking devices. But are...