Secure, fast, clean antivirus for Mac
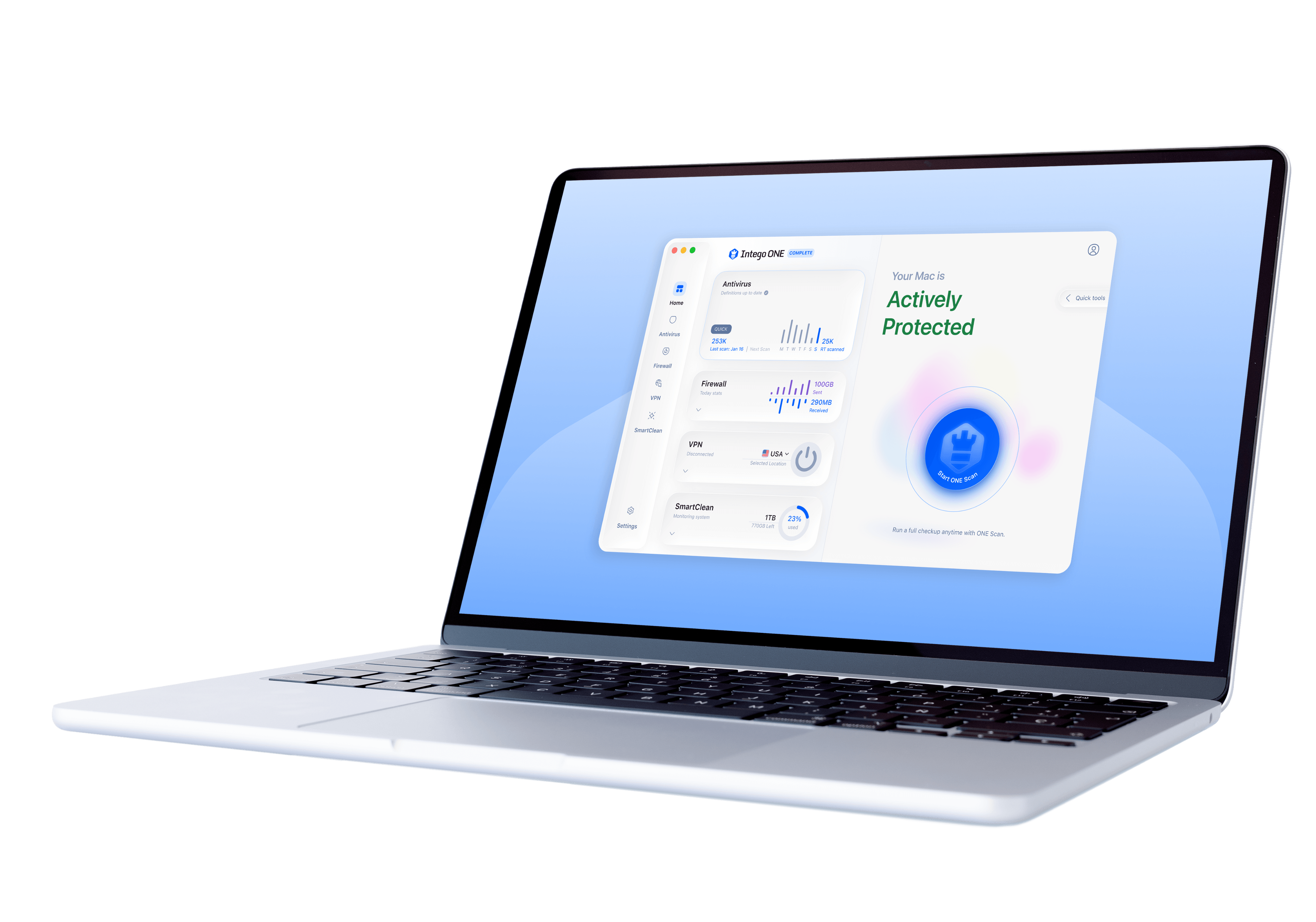
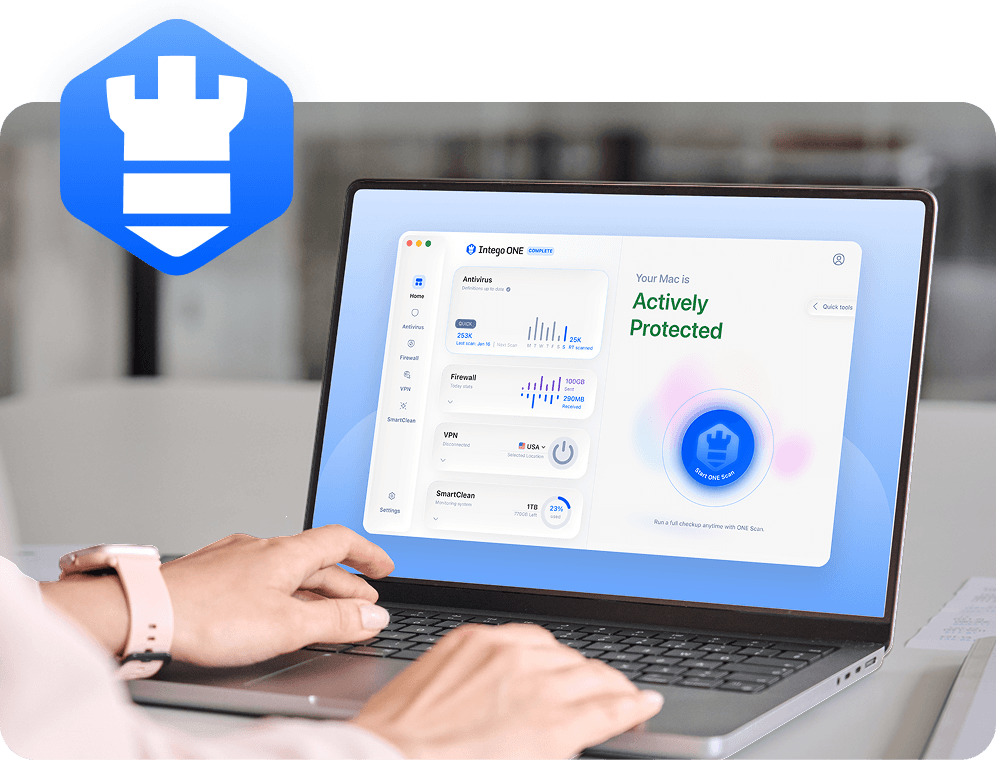
Intego ONE is built for macOS, giving your Mac real-time antivirus, firewall, VPN, and optimization tools in one sleek app.

| Apple | Notarized |
|---|---|
| 4.8 | Excellent on Trustpilot |
| Mac-First | Since 1997 |
| 30+ Million | Devices Protected |
As seen in





Do Macs really need an antivirus?
For years, people believed Macs were immune to viruses. While Apple builds strong defenses into macOS, new malware, phishing scams, and online threats are evolving constantly. Today, cybercriminals target Macs just as aggressively as Windows PCs. That’s why dedicated Mac antivirus software is essential to keep your files, data, identity, and privacy safe.
Modern threats don’t discriminate. Protect your Mac with confidence. With Intego ONE, you don’t just react to threats - you stay ahead of them.
Smarter Mac security,
faster performance
Everything you need to keep your Mac safe, private, and running at its best.
Real-Time
Malware Detection
Stops threats before they can harm your Mac, with constant monitoring in the background. That way, you always stay protected.
Full &
Quick Scans
Run a fast scan for instant peace of mind or choose a deep system check. Flexible options put you in control of your security.
Suspicious
File Quarantine
Risky files are automatically isolated so they can’t spread. You decide whether to remove or restore them safely.
Firewall Rules
& Traffic Stats
Block unwanted connections and track how apps use your network. Get clear visibility and control over your Mac’s traffic.
Fast Global
VPN Servers
Connect to secure servers worldwide for privacy and speed. Stream, browse, and work online with confidence from anywhere.
Optimization Scans
& Quick Cleanup
Clear clutter and junk files in minutes. Keep your Mac running fast, smooth, and free of unnecessary baggage.
What your Mac has and
what it’s missing
With Intego ONE, you get stronger protection, true privacy, and smoother performance.

With Intego ONE
Without Intego ONE
Strong Protection
Intego ONE’s antivirus and firewall work together to block threats and unwanted connections before they can reach your Mac.
Exposed to Risks
Viruses, spyware, and hackers can slip past limited built-in defenses, putting your personal data at risk.
Private Browsing
Intego VPN encrypts your internet traffic, masks your IP address, and keeps your online activity truly private.
Online Vulnerability
Without a VPN, your browsing data and location may be visible to your ISP, advertisers, or cybercriminals.
Smooth Optimization
SmartClean clears clutter, frees storage space, and monitors performance so your Mac can run fast and smoothly for long.
Performance Slowdowns
Junk files, unneeded files, and background drains build up, leaving your Mac sluggish over time.
30-Day Money-Back Guarantee
Scan your Mac in just a few clicks

01
Open Intego ONE
Intego ONE’s Home screen gives you easy access to all protection & optimization tools in one place.

02
Click “ONE Scan”
Choose ONE Scan for complete coverage of your Mac, or choose any other scan that fits your needs.

03
Detect threats
Any suspicious files are instantly identified and quarantined, preventing them from causing harm.

04
Take action
Review the scan results, remove unsafe items with one click, and enjoy peace of mind knowing your Mac is secure.
Why choose Intego ONE Antivirus for Mac
Go beyond basic defenses. See how Intego ONE boosts your Mac’s protection, privacy, and performance.
Features

Intego ONE

macOS Built-In
Real-Time Threat Detection
Limited
Quarantine for Suspicious Files
Malware Remediation
Limited
External Drive & USB Scans
Firewall with Custom Rules
Limited
VPN for Private Browsing
Junk File Cleaning
Four essential tools,
ONE solution
Intego ONE for Mac is designed to keep your computer safe, private, and running smoothly.

Antivirus
Intego’s real-time protection, engineered for macOS, blocks threats instantly- from viruses and ransomware to spyware - so your Mac stays secure without interruptions, 24/7.

Firewall
Take control of your computer’s connections. Our firewall shields you from hackers, blocks unwanted traffic, and keeps your personal data out of the wrong hands.

SmartClean
Give your computer a fresh start in minutes. SmartClean clears junk files, reclaims wasted space, and boosts performance - so your computer feels faster, lighter, and more responsive.

Intego VPN
Browse with true privacy, wherever you are. Intego VPN encrypts your Internet traffic and masks your IP address so you can stream, shop, and connect with total confidence.
Minimum System Requirements
Intego ONE is lightweight and built to run seamlessly on supported Macs. To install, you’ll need:
OS
macOS 12.4 or later
CPU
Intel or Apple Silicon processor
RAM
At least 8 GB of memory (16 GB recommended for best performance)
Storage
2 GB of available disk space
- OS: macOS 12.4 or later (including macOS Sequoia 15.x)
- CPU: Intel or Apple Silicon processor
- RAM: At least 8 GB of memory (16 GB recommended for best performance)
- Storage: 2 GB of available disk space
What our most satisfied customers say
{"trustpilotBtnText":"Testimonials","techReviewsBtnText":"Reviews","hideCarousel":false,"selectedType":"testimonials","legalText":"We sometimes pay review sites to refer customers to us."}Award-winning security for Mac and PC

AV Test

AV Comparatives

VB100

Gold Award Winner
TopTenReviews

Editors Choice
Our 30-day
money-back guarantee
Install Intego in minutes and run your first scan right away. If you are not completely satisfied, contact our support team within 30 days for a refund. No hassle, no long forms, and no hard feelings.
Frequently asked questions
A well-designed Mac antivirus should not slow down your device. Modern solutions run background scans efficiently and use cloud-based threat databases to minimize system impact. In fact, regular scans can contribute to better Mac optimization by removing unwanted files and malware, helping your system stay fast, secure, and running smoothly.
Apple’s XProtect works silently in the background, blocking certain known malware, but it doesn’t allow manual scans. With Intego antivirus, you can run Quick or Full Scans anytime, isolate suspicious files, and get a clear report so you always know your Mac is secure.
macOS doesn’t include a traditional antivirus app, so there’s nothing to turn off. With Intego ONE, you can pause protection temporarily from the Home screen, then easily turn it back on to stay safe.
No. While macOS is generally more secure than some other operating systems, it’s not immune to malware or online threats. Hackers continue to develop viruses, spyware, and ransomware that specifically target Mac users. That’s why Intego ONE delivers essential, Mac-first protection designed to detect and block malware before it can cause harm.
Yes, macOS includes XProtect, which blocks certain known malware, and Gatekeeper, which checks apps before they open. These are useful but basic. Intego ONE gives you complete, real-time defense against both known and emerging threats.
Free tools exist, but they often provide only limited detection, no real-time scanning, and don’t specialize in Mac protection. Intego ONE offers full cybersecurity protection, privacy features, and optimization tools in one reliable solution designed especially for macOS by Mac protection experts.
Mac antivirus is designed specifically for macOS architecture and its built-in protections. Unlike many cross-platform tools, Mac-specific antivirus software integrates smoothly with macOS, offering optimized scanning and detection for Mac-targeted threats while using minimal system resources.
Intego
Trusted. Proven. Powerful.
Driven by innovation for over 25 years, Intego has provided advanced cybersecurity solutions built to protect what matters most — your data, your privacy, and your devices.
With award-winning antivirus, firewall, VPN, and system optimization tools, Intego combines powerful defense with the simplicity and reliability Mac and PC users expect.