Safe Surfing Tips for OS X and iOS
Posted on
by
Kirk McElhearn
We recently discussed how to shop safely online during the holiday season. All of the points in that article also apply to shopping all year round, and are good practices to develop to ensure that your online activity is safe. But there are also some other things you can do to make sure that you surf safely, even when you’re not shopping. Here are three tips to surf safely online, on both OS X and iOS.
Keep Your Browser Up to Date
No matter which web browser you use, you should make sure it is always up to date. This is essential because all browsers regularly apply security updates to protect against newly-discovered exploits, many of which can be injected into websites, even popular ones.
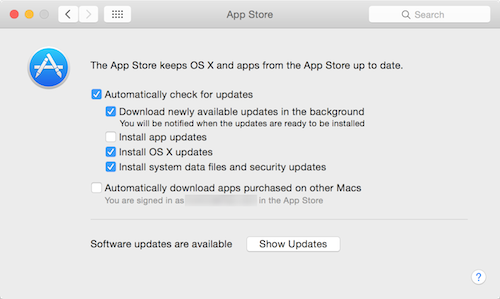
If you use Apple’s Safari, have the Mac App Store app check for updates automatically, and have it install OS X updates and system data files and security updates.
To do this, open System Preferences, then click App Store. Check the following options: Automatically check for updates, and, ideally, Download newly available updates in the background. Also check Install OS X updates and Install system data files and security updates.
If you use Google Chrome, it updates automatically in the background. However, if you run Chrome regularly and don’t restart it, it may not update. If so, the Chrome menu, at the right of the toolbar, will change to green, orange or red to alert you. See this Google technical note to learn more.
Firefox also updates automatically when you launch it, if updates are available (unless you turn this feature off in Firefox’s Advanced preferences). It tells you that an update is available, and prompts you to restart it.
On iOS, you’ll see updates to all your apps in the App Store app. Make sure to check it regularly and update apps you use to access the internet as soon as you can.
Don’t Get Caught by Phishing
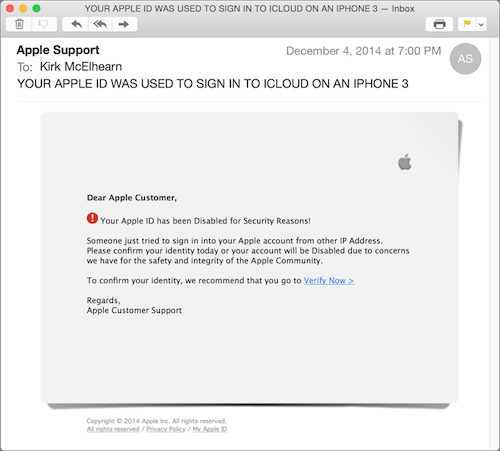
One of the more serious threats to your online life is phishing. This is when cyber-criminals send email messages purporting to be from banks, or companies like eBay, PayPal or Apple, in an attempt to trick you into giving up your login credentials. Here’s one phishing email I got recently:
This looks more or less like an email from Apple. But if you look closely, you can see a few grammatical errors (“from other IP address,” and “Disabled” with a capital D), but also a somewhat archaic subject line, which mentions an iPhone 3.
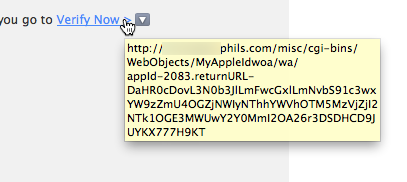
Many phishing emails look real, and can fool you. Before you click any links, check the URLs behind them. To do this, hover your cursor over the link and wait to see the URL that displays:
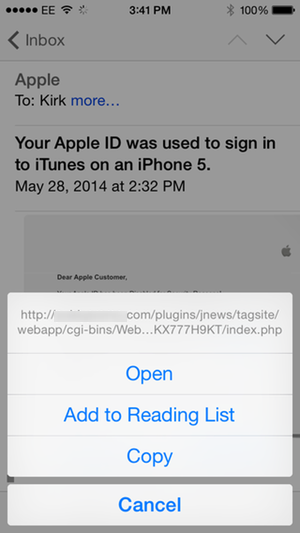
If you’re on an iPhone or iPad, tap and hold the link, and you’ll see the URL at the top of a sheet:
In both of these cases, you can see that these are not Apple URLs.
The risk here is that, if you log into your account after clicking one of these links, you’ll be taken to a page set up to harvest your credentials, which can then be used to empty your bank account, or buy lots of stuff on the iTunes Store.
It’s easy to assume that most such emails are bogus. But Apple does send you emails if you log into your iCloud or iTunes Store accounts from a new device, so you do sometimes get authentic emails like this. And your bank or credit card company may send you emails as well. To be safe, always check the URLs behind the links, or log into your account by manually typing the URL in your browser.
Protect Your Identity
Not long ago, a friend of mine posted on Twitter, saying something like “This Famous Person shares the same exact birthday with me!” That’s an interesting tidbit to discover, but I replied to his tweet, saying, “Congratulations, you’ve now told the entire Internet your birthday.” He promptly deleted his tweet. You’re bound to give out information about your life when you discuss things with people, when you post on Facebook or on forums, or if you have a blog. But make sure you know that some of that information has a risk.
There’s lots of personal information about you on the web. If you use Facebook, your friends can know when it’s your birthday; the month and day, but not the year. The same is the case on some other social networking services and forums. Yet your birthday—the full month/day/year—can be one of the elements you need to identify yourself. (Whenever I use my bank’s telephone support, it’s one of the pieces of information I have to give, for example.)
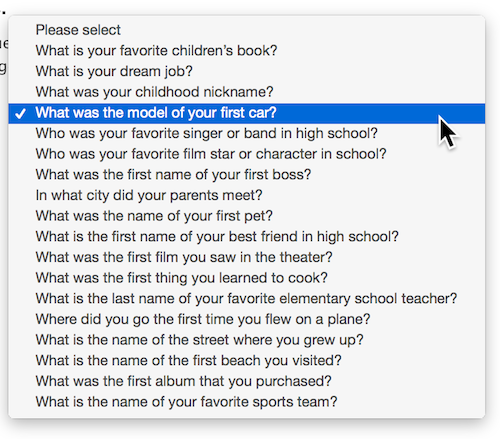
You are often asked to record certain bits of information for security purposes; these are often used to reset your password, if you’ve lost or forgotten it. If this information is publicly available, someone may be able the impersonate you, and get access to your accounts. One of the most common elements of information used to be your mother’s maiden name, but that’s been supplanted by more personal questions. Here’s what Apple offers on its Apple ID website:
Some of these questions may be easy to figure out. For example, if you had a nickname as a child, you, or a friend, may have mentioned it on Facebook. And you might have mentioned your best friend in high school; you might post about going to his or her wedding, for instance. You might have a discussion on Twitter about cats, you mention the name of the first one you had. And the name of your favorite sports team? Half my Facebook friends post about sports, and that would be easy to guess.
There are two approaches to dealing with these questions. The first is to choose the most obscure ones, things you’ll likely never mention online. This could be the first thing you learned to cook, the name of your first boss, the first beach you visited, or the first destination for a plane trip, for instance.
The second approach is to not answer the questions honestly, so long as you remember the answer. This is what I call the “Ed Norton” approach. In an episode of The Honeymooners, The $99,000 Answer, Ralph Kramden has to say who wrote the song Swanee River. His friend Ed Norton always played a bit of this when warming up, while he was helping Ralph study for the game show. But Ralph didn’t know who wrote it, so he answered, “Homina, homina, homa… Ed Norton?”
In other words, there’s no harm in having some fun and giving an answer that no-one else on the Internet will be able to guess, especially if it offers greater protection. You don’t need to supply the answer to the question that is asked. You could reply Ed Norton, or Mister Mxyzptlk, or use some random characters, if you wish. Or use a phrase, such as a favorite quote, or a line from a song. It’s a good idea, though, to use something memorable, because you may need this information to reset your password.
Use these three tips to keep your online activity safe and secure.
Further Reading:
- How to Keep Your Family Safe and Protected Online
- 6 Cyber Security Tips for Holiday Shopping Online
- How to Maintain Your Privacy on the Internet
- Top 5 Fast and Easy Ways to Improve Your Privacy Online