Apple’s AirTags: One Year On
It's been one year since Apple's AirTags were released; it’s time to take stock. How efficient have they been?...
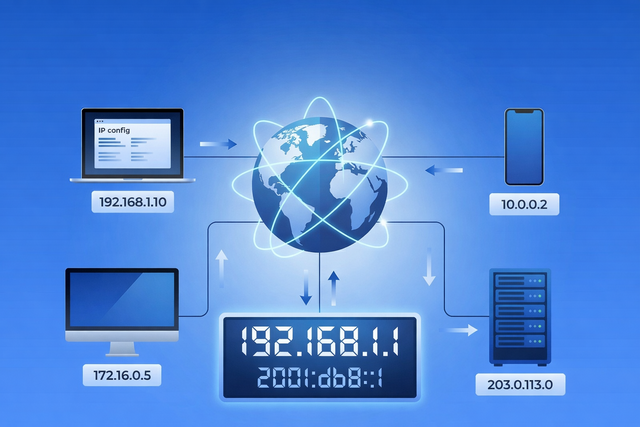
Every time you open a website, stream a video, send an email, or connect to Wi-Fi, your device relies on an IP address. You rarely see it, and most of the time you probably do not think about it. But it plays a quiet, important role in how the internet works. Your IP address helps...

Apple has just released critically urgent security updates—including macOS Sequoia 15.4.1 and iOS 18.4.1—to address two zero-day vulnerabilities that have been actively exploited in...

Macs have a strong security foundation. That’s true — and it’s worth appreciating. But “safer than” doesn’t mean “safe from.” Modern Mac threats don’t...
Is your Mac running slow? Here's how to diagnose and fix performance issues and get your Mac to run faster.
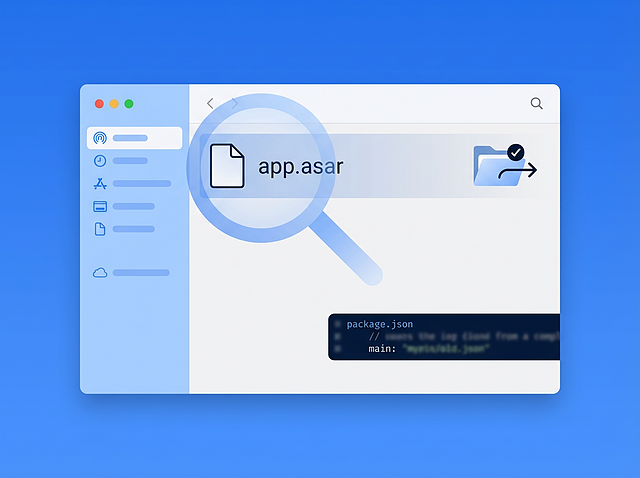
Executive Summary In March 2026, Intego Antivirus Labs investigated a macOS malware campaign delivering the OSX/Amos stealer. During analysis, the infection chain led from stripped Mach-O binaries and heavily obfuscated shell scripts to an unusual final payload that appeared...

It's been one year since Apple's AirTags were released; it’s time to take stock. How efficient have they been?...
Josh has a 15-year old iMac that he wanted to be up to date with security updates, but it...
DuckDuckGo is beta testing a privacy-focused browser; Google is deprecating old apps in its Play Store; activation-locked AirPods are...
Apple has issued new updates, but hasn't patched two serious vulnerability for Big Sur and Catalina. We also look...
Apple has chosen to leave Big Sur and Catalina (around 35 to 40 percent of all Macs) in danger...
Security & Privacy + Security News
Apple has just released fixes for two actively exploited vulnerabilities affecting macOS Monterey, iOS 15, and iPadOS 15. Here...
New malware, a new Chrome zero-day vulnerability, and why iOS auto-updates take so long to update. We discuss Apple's...
Universal Control lets you use Macs and iPads together, controlling them from one keyboard and pointing device.
We follow up on our recent episode explaining the jargon used in cybersecurity, explaining hacking and cracking, black hats...