iOS 9.3.4 Update Kills Flaw, Sabotages Pangu Jailbreak Exploit
Posted on
by
Derek Erwin
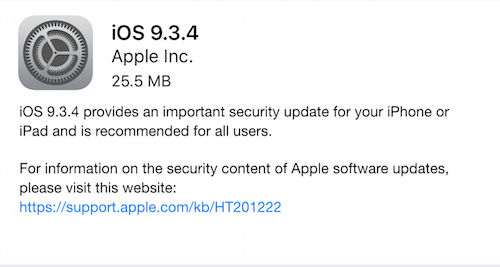
In a bit of a surprise, Apple has pushed an important security update to its mobile operating system to iOS 9.3.4, released on Thursday. iOS 9.3.4 is available for iPhone 4s and later, iPad 2 and later, and iPod touch (5th generation) and later.
The iOS 9.3.4 update patches a memory corruption security flaw and sabotages the Pangu jailbreak exploit. The flaw Apple patched may have been discovered and used by Pangu Team to facilitate their jailbreak, according to an iClarified report.
Apple’s security bulletin describes the vulnerability as follows:
CVE-2016-4654 : An application may be able to execute arbitrary code with kernel privileges. A memory corruption issues was addressed through improved memory handling.
Jeff Gamet over at The Mac Observer offered a brief overview describing how Pangu is a tethered jailbreak for iOS 9.3.3, “meaning users need to connect their iPhone or iPad to their computer to use the hack.” Jeff noted, “Like other jailbreaks, Pangu lets users install apps that aren’t available on Apple’s App Store.”
Not surprisingly, similar to what we’ve seen before with previous jailbreaks, some Pangu users reportedly had their credit cards, PayPal accounts, and Facebook logins compromised after using the tool.
This isn’t the first time a jailbreak exploit compromised iPhones. The malware family, identified by Intego VirusBarrier as iOS/KeyRaider, brought bad news for people jailbreaking their iPhones: Over 225,000 iOS devices were hit by the malware attack. KeyRaider malware was stealing Apple ID account usernames and passwords, certificate keys, private keys, App Store purchasing information and more.
Other instances included the Cloud Atlas malware, identified by Intego’s Mac antivirus as iOS/CloudAtlas, which could exploit Apple’s iOS iPhones and iPads if they have been jailbroken. After the iCloud Atlas malware was installed on a jailbroken iOS device, it would collect a wide variety of information and transmit it to an FTP account under the attackers’ control.
Another security researcher uncovered that some 75,000 jailbroken iPhones were infected by malware known as iOS/AdThief. And the list goes on. There are thousands of reasons not to jailbreak your iPhone; it’s just not worth the risk, and so it makes sense that Apple moved quickly to shut down the Pangu jailbreak exploit.
iPhone and iPad users can get the update directly from your iOS devices (Settings > General > Software Update), or it can be downloaded and installed in iTunes when a device is connected to a computer with an Internet connection.

