Intego discovers new Atomic Stealer (AMOS) Mac malware variants
Posted on
by
Joshua Long

In May 2023 and September 2023, and again in February 2024, we wrote about earlier variants of the Atomic Stealer Mac malware family. This malware—also known as Atomic macOS Stealer or AMOS for short—is designed to exfiltrate sensitive data from infected Macs. Such data typically includes saved passwords, cookies, autofill text, and cryptocurrency wallets.
AMOS is distributed in the form of Trojan horses, often masquerading as supposedly pirated or “cracked” versions of apps. In recent months, AMOS Trojan horses often pretend to be the legitimate apps they mimic; they employ elaborate campaigns, leveraging malicious Google Ads that link to lookalike homepages with Trojan downloads.
Over the past two weeks, Intego has been tracking several new variants of Atomic Stealer. Here’s everything you need to know about them and how to stay protected.
In this article:
- Mimicry of File Juicer, Debit & Credit, Parallel NFT game, and Notion
- Source of these new AMOS infections
- Malware embedded within malware
- How can I keep my Mac safe from AMOS and other malware?
- Indicators of compromise (IOCs)
- How can I learn more?
Mimicry of File Juicer, Debit & Credit, Parallel NFT game, and Notion
The latest variants of AMOS masquerade as several different apps, all distributed through DMG disk images.
Fake “File Juicer” and “Debit & Credit” app installers
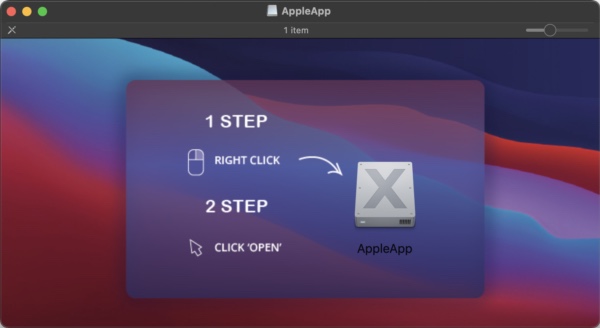
At least two disk images, when mounted, include a single app called “AppleApp” with an icon that implies that it’s an installer.
One fake-installer variant launches a Trojanized version of File Juicer, an app for extracting embedded files from various document formats. The real app costs $19.
A second fake-installer variant launches a Trojanized version of Debit & Credit, a personal finance app that’s normally only available through the Mac App Store. The real app is a free download, but a “premium version” is available via a $19.99 in-app purchase.
Fake “Parallel” NFT TCG game
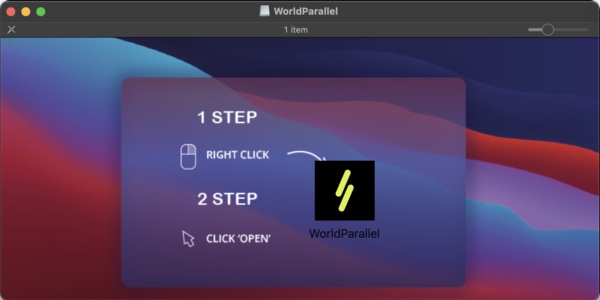
Another disk image, when mounted, includes a single app called “WorldParallel.” With a little investigation, we discovered that this Trojan mimics a Windows-only, NFT-based digital trading card game called Parallel, which its developer describes as “a Sci-Fi world and Card Game.”
It isn’t surprising to see malware disguise itself as something related to non-fungible tokens (NFTs), blockchains, or cryptocurrency; fake crypto wallet apps are another common Trojan horse. We’ve even observed stealer malware that was distributed through elaborate video-game marketing campaigns.
This is because a primary goal of stealer malware is typically to attempt to exfiltrate digital wallets, which may contain valuable assets such as cryptocurrencies or rare digital artwork.
Fake “Notion” app
And last but not least, we’d be remiss if we didn’t mention that, once again, some AMOS samples mimicked the Notion productivity software.
We mentioned in February that AMOS had been spreading via malicious Google Ads that mimicked real Notion software ads.
Source of these new AMOS infections
Although we have not definitively confirmed the original source of these infections, it’s likely that the team behind AMOS is up to its usual tricks, including Google Ads poisoning. Threat actors often pay Google for top placement, with sponsored ads disguised as real ads for legitimate software. These ads appear immediately above the actual search results; if you aren’t careful, you could inadvertently visit a malware distribution site instead of landing on the real software developer’s site.
We recommend that consumers get out of the habit of “just Google it” to find legitimate sites. Such habits often include clicking on the first link without giving it much thought, under the assumption that Google won’t lead them astray, and will give them the correct result right at the top. Malware makers know this, of course, and that’s why they’re paying Google for the number-one position.
Until or unless Google does a much better job of vetting its ads, a better practice than “Google it” would be to bookmark trusted sites whenever possible, and to go back to those bookmarks in the future.
Malware embedded within malware
One interesting observation from Intego’s malware analysis lab is that many of the initial stage (dropper) apps contain the secondary payload embedded within them.
In some cases, the embedded payload was unobfuscated (i.e. plainly visible). However, in other cases, the embedded payload was Base64 encoded, in a weak attempt to hide the payload from antivirus software.
“Droppers” are initial-stage malware samples designed to obtain and install additional malware. Typically, droppers connect to malicious or hacked sites to obtain their next-stage payloads. Embedding payloads within the dropper itself can sometimes allow malware campaigns to succeed for a bit longer. This is because sites that host malware may be taken offline quickly, or disinfected and patched as soon as the site owner becomes aware of the infection. In the case of a newly registered malicious domain, the registrar may retake control of the domain, take it offline, and revoke the purchaser’s access.
How can I keep my Mac safe from AMOS and other malware?
If you use Intego VirusBarrier, you’re already protected from this malware. Intego detects these samples as OSX/Amos.ext, virus/OSX/AVI.AMOS.jlei, virus/OSX/AVI.AMOS.lydw, virus/OSX/AVI.AMOS.mlhs, and similar names.
 Intego VirusBarrier X9, included with Intego’s Mac Premium Bundle X9, is a powerful solution designed to protect against, detect, and eliminate Mac malware.
Intego VirusBarrier X9, included with Intego’s Mac Premium Bundle X9, is a powerful solution designed to protect against, detect, and eliminate Mac malware.
If you believe your Mac may be infected, or to prevent future infections, it’s best to use antivirus software from a trusted Mac developer. VirusBarrier is award-winning antivirus software, designed by Mac security experts, that includes real-time protection. It runs natively on both Intel- and Apple silicon-based Macs, and it’s compatible with Apple’s current Mac operating system, macOS Sonoma.
One of VirusBarrier’s unique features is that it can scan for malicious files on an iPhone, iPad, or iPod touch in user-accessible areas of the device. To get started, just attach your iOS or iPadOS device to your Mac via a USB cable and open VirusBarrier.
If you use a Windows PC, Intego Antivirus for Windows can keep your computer protected from malware.
Indicators of compromise (IOCs)
As is typical, some of the Atomic Stealer samples we encountered have a very low detection rate on the multi-engine single file scanning site VirusTotal. For several samples, only 5–8 out of 60+ antivirus engines appear to detect them. At least three samples (two Mach-O binaries and one DMG disk image) were completely undetected when first uploaded to VirusTotal.
Following are SHA-256 hashes of malware samples related to these new AMOS malware campaigns:
8ef8fd7284843ab9e9309324a1eb9244850d9c2509ce9688dbf18f41c1370c4d 1dc2465654b7c5975d759649f023836c2af44c6a2936a71aad7e4e6c04fc0de9 8dd270c85f193617cd19ee268f852a8a19c90d470d1111b0ec50196087514277 78b7578fd77e6b3ea104f4c9f62c35fca5598caa430846c818b9e75540e10ef4 8e2d24aa70563688a80426d542883f45387cd093a2223fbd1320ecb95769fdf2 c405178e388752c5723e4dacde8b328abae15a7b953b438160d3e91a4386533f 6881e8b2c584e4b2fe05af6b501d5f4a6e43a7890d36b6da6b5342313cb5ce4e f747be2535bb146e1c7737dfc7c025419c92a877d7b51033eb3c48e6c08ce7cb 7944a8c9445c74975f14ebeee6ae5f1f7a50b39e5d4b478c645744b661754858 4d5e9d97e48a72639193b9dd4c0bcced376bde7943b87f0aea5333021c0cb073 9b0795e9b965b64a8931a8f9a7ac6ebd26f5dd7d70adaea7be13b04bfe56f6d5 34053a4fcddc5c3553eb9d988b32bc7bddae2ac63fdfc5b00a8270047706bd24 fb34bf9a66ff444c3a83b614af1ee2c5771cf21a676155207f1eefe52b89d2f1 ceb7c1a06a4c938a65d97aedbe2e18ca333f71827a015a0342ba1c13734c2032 d02aee0fc3c03558eaf99afd8d54424e59f7aa6c957bc49126484ad3071472dd 399614070ed2a44857d153979ee1ea0e2b05731d22409dede07b39d0869bcc90 1167f14f456e4bb54dc23fe858b571832fbb4e4801c883e134ba01270e6ef6b6 fdaaa25cc6be47bc893f773fcd7c0d8ad6c3618bf931f4b728eb5a1d920527f5 55e587ea12e590e70c500643cf2555a98edd00f90ee19aee0089998faf017b96 379fc1ec90b98ac4312184fda5a810ac7114e39385901103ca07dd22bb5382f1 88b5d4ec8b8ccc4d2b791317e1be6a24db98175af4c9f42d6a7cc277a0012b58 8c922dead9372c87c08f2e25f96538154be922a1511bb947e631b2d4a31bba2a d1b0fc3d03b4e6cd14b430daf0361989b8a65e87c30d5ea7436b1d51864114b6
The following domains have recently been used in connection with these AMOS samples:
dowlosutr[.]click farmfrnd[.]com tarafe[.]com
Network administrators can check logs to try to identify whether any computers may have attempted to contact one of these domains recently, which could indicate a possible infection.
How can I learn more?
Be sure to also check out our 2024 Apple malware forecast and our previous Mac malware articles from 2024 and earlier.
 Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, including security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, including security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
You can also subscribe to our e-mail newsletter and keep an eye here on The Mac Security Blog for the latest Apple security and privacy news. And don’t forget to follow Intego on your favorite social media channels: ![]()
![]()
![]()
![]()
![]()
![]()
![]()

