Atomic Stealer: Thieving Mac malware sold via Telegram
Posted on
by
Joshua Long

A threat actor is offering “malware as a service” that can steal sensitive data from Macs. Dubbed AtomicStealer—or Atomic macOS Stealer, AMOS—the framework enables cybercriminals to create custom Trojan horse malware. These Trojans attempt to exfiltrate passwords, stay-logged-in session cookies, cryptocurrency wallets, and more.
Below, we’ll explain what you need to know about this new Mac threat and how to stay protected.
In this article:
- What does OSX/AtomicStealer Mac malware do?
- How can one remove or prevent AtomicStealer and other Mac malware?
- Who created the AtomicStealer malware framework?
- AtomicStealer indicators of compromise (IoCs)
- Is AtomicStealer known by any other names?
- How can I learn more?
What does OSX/AtomicStealer Mac malware do?
A threat actor has recently begun selling access to a new, customizable Mac data-stealing malware framework. Access to the framework is advertised via the Telegram secure messaging app.
Reportedly, other cybercriminals can “lease” the malware framework at $1,000 per month. This implicitly means that the original developer may continue to update the framework to try to evade antivirus detection as part of this “malware as a service” operation.
So what can AtomicStealer-based malware do? We can easily observe that the malware attempts to trick users into divulging their administrator password via a fake system prompt, generated with AppleScript code.
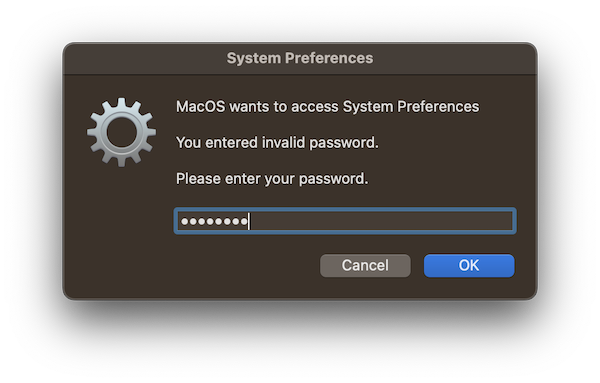
AtomicStealer’s first variant attempts to trick users into giving up their admin password via a fake system dialog box.
If users type their password into this dialog box, it is then logged insecurely on the system—in plain text.
According to the seller, the malware can do a number of other things, but the primary goal appears to be exfiltration of valuable digital assets.
The malware will supposedly try to export all passwords from the Keychain, steal saved passwords and stay-logged-in session cookies from all popular browsers, and steal cryptocurrency from more than 50 varieties of wallets.
After obtaining a victim’s passwords and session cookies, an attacker may be able to pivot to breaking into other accounts belonging to the victim. As we mentioned recently in our coverage of MacStealer malware, stealing stay-logged-in cookies often allows attackers to bypass two-factor authentication.
How can one remove or prevent AtomicStealer and other Mac malware?

Intego VirusBarrier X9, included with Intego’s Mac Premium Bundle X9, can protect against, detect, and eliminate this Mac malware. Intego products detect components of this threat as OSX/Downloader.go, or variations of virus/OSX/Agent.
If you believe your Mac may be infected—or to prevent future infections—use trusted antivirus software. VirusBarrier is award-winning antivirus software, designed by Mac security experts, that includes real-time protection. It’s compatible with a variety of Mac hardware and OS versions, including the latest Apple silicon Macs running macOS Ventura.
Additionally, if you use a Windows PC, Intego Antivirus for Windows can keep your computer protected from PC malware.
VirusBarrier X6, X7, and X8 on older Mac OS X versions also provide protection. Note, however, that it is best to upgrade to the latest versions of macOS and VirusBarrier; this will help ensure your Mac gets all the latest security updates from Apple.
Who created the AtomicStealer malware framework?
The first researcher to write about AtomicStealer’s initial variant noted something interesting: evidently, the username on the developer’s computer was iluhaboltov. Although this does not provide definitive evidence of the malware author’s name, it’s noteworthy that the developer began using an account with the generic username administrator for subsequent variants of AtomicStealer.
Boltov is a surname that is most common in Russia and Ukraine; it means “bolts” in Russian.
Iluha isn’t a particularly common given name, but it can be a masculine East Slavic name, a variant of Elijah. Iluha can also mean to weep or to tear up in Filipino or Tagalog. Iluh can be a Balinese name for a first-born female. Luha can be an Islamic feminine name meaning measure or amount.
If the developer truly did reveal their own name, it wouldn’t be the first time that a cybercriminal has made such an opsec failure. In 2019, Intego published a white paper (PDF) about Mac malware attribution in which I wrote about several malware makers who had unintentionally exposed their real names by mistake.
AtomicStealer indicators of compromise (IoCs)
The following SHA-256 hashes relate to AtomicStealer malware campaigns:
0498d08c1bc471fa4c4ebd1242bfaeabd79c4e1a8133205274a6e2c08c7cb581** 1062073ce5aad5bc8f05bd6b47898d5c11ace4a32cb1234e0c9c4f5aa27a6d17 15f39e53a2b4fa01f2c39ad29c7fe4c2fef6f24eff6fa46b8e77add58e7ac709 18d09f30c600855411488e670ef8413c3dc7f9f326b697c9815ba2a5baa55c0f 20a7971970dc0e0e02859f9c51a0626455a146919b8dc9c9c8172bd18988e8df* 2175cc3bc1e3bf4cc27a9524b34d47c14b9aa094061600c0c4bfee9447bd54b4 262f6dc6862c0377034d50c007386860d7a3ca3da95b6ecc2dfa53057b5924fa* 26b304352f45fd551195a66b7fbf493122cbc1442d6ef2aea73d75458c19bc56 2b4a06a50ff151f38586f1f3ae97990efb69dba80bfd4521a50ccdeeb4cf2b5b 2c63ba2b1a5131b80e567b7a1a93997a2de07ea20d0a8f5149701c67b832c097 2d0dda75bfc90e7ffda72640eb32c7ff9f51c90c30f4a6d1e05df93e58848f36 3a14c28ec0bd616b029efa6b1421a120869c80f088add868de93aeefd1b60cbc** 3dcb157b5a16f76e60f0407f7036692d04c2dfbbf334c2b843ec77a9b2f930fe* 4594513f34af968cf3fba5cd50331bbe7329ce436898eedecf53e574f6e05dcc 4cc591bf6dbfe851cc8fd891d8a5f3c2723dcad14e12f81eb58c008267ab8489 4d9a01b8f1efd30d39d7f6af61f2723f593436fdd667669b15d149db6eac04b0 51a0b39dc222749788e6559d5068b3633366b1a03690ac16e29f1ba9ed2f87ff 56cd21cb9f114e7e1709592449ab7cce2bb3a2a7c89dab72f9be88a99fc9e775 6152e233795fa52b5ee2c0283636c76d6389c9dfad5413408ea26fd7aa42fa23 71bcccde296cea2da9ad9ff294c672123e782abb3369d0576c3456391d4bb13e** 73ec6b3ec30b5437c910d04057e721a94525dcab00c283cac5a8cef8a28b2cae* 77589a321b3b876d4179cd4d287e6111b00edbfaeb50e5c2e729bf10a7ac005c 7e481f05173d895c2aa50fa5625a48877af2284da53285a71cc9845674004239 7fe19d8f93feafbbc23a1640534e9de2f5d6c88411bb23f622dabe5038026426* 821b05cef55eca9e07697c02b837567a75c9adc2e82afb798a41b4e6c0ae2ee9 82d2c1cdf97bbbb537879be0f3a50f28aa74ce353c6c4f4df736eae7751675b7 972c60772190eaf6a7d4fd15a342bcb947d49e39e996ddc899ff77eb31f113aa 990aaf49f24274dbecb68929683b1baa5ed1621722bed774ee8694b541b785e3 9d34698409f4a140822cd2e83c0f0c109436e8028a7e15f3e4428b41a86fa168** a00f4722b3922a61febd6db22c3cacfb75f3fcfe9f4e1a372e3c6d7d4ee94947 a2fec3172d70f7515d43959264a0ee55433ca8207b7022dc1f6430a1616d9a64 a4d590b7b0b5b1d7971b6f24a210afaa6024ac6b1ac13bbbb668739a230acc8f a856dccf60644f8e95461f5eb1f20fd688a72ce778625d775455e73cbe2648d3 ae24165de234f584dc53ab941e22e9f479d02baf6cdd6f120c84f7e8ebb5aca5** c294c28ef8f07bc30c9fe1980bd83236ae52fbdcb596117aa675ebe28a7ea548 c4078213cf64a68c5f0fc77d65e16d989d817c09814a01f73e37099c4ed6e0a7** c65a90e559db80612209717337a86bd072beb0125af126772873a4a6da50bf96 c76f71a617937866b5ccef9f10658cabc81c400f50971e04455c07a8d08da5b6** d9e46d316a975ec70827916976988fcff582e42f3927e0e158a9cd89c15a0b6e* e06a094d0bec6020536cdb92f0bd2171e48ca36b3f34b8ffd6da7f52f78436ec e2a756710241d90fd5d2c3fb33bf787014e1f5b4b6b516b6afd8fcb7cbd0ccbf e3d703fee5b08f5c869f34d79d08b8b9438b261a737c8b1275655f403b0b39e2 e6b6cf40d605fc7a5e8ba168a8a5d8699b0879e965d2b803e29b87926cba861f ea2235ea26951276cf724430774e1817295e53e64c55ababac38ec5443f066f6** f8cd5ff37ef71afe16b4499d9e0f7b92a7759e3cacb0fbbdc78bec39842c99a1 ff23a27fd326d428e931a42fa08d9e0c17f16c9cd7a1afbaba16ab4ae80a6656** ff4ce9dfe2ced97df1deeeda3e2450e958bd4bcad3778bad2bed080619014f46 * First reported by Intego **First reported by Intego; added 8 May 2023
Looks like a new variant of the “Atomic macOS Stealer” malware dropped just in time for Cinco de Mayo. Very low detection rates on @VirusTotal.
All of these new samples were uploaded in the US via VT API keys, IDs af632c50 or 97e2a062. #AtomicStealer #AMOS #OSX #malware pic.twitter.com/WFSU1FykHW
— Josh Long (the JoshMeister) (@theJoshMeister) May 6, 2023
These command-and-control (C&C) domains and IP address have been used in conjunction with this malware:
amos-malware[.]ru 37.220.87[.]16
Network administrators can check recent network traffic logs to try to identify whether any computers on their network may have attempted to contact this domain or IP address, which could indicate a possible infection.
Is AtomicStealer known by any other names?
Other vendors’ names for threat components related to this malware campaign may include variations of the following, among others:
A Variant Of OSX/PSW.Agent.J, Backdoor (0040f37c1), DMG/MAC/Agent.C, Gen:Variant.Trojan.MAC.Stealer.3, HEUR:Trojan-PSW.OSX.Amos.a, HEUR:Trojan-PSW.OSX.Amos.gen, IOS/Agent.T, Mac.Stealer.5, MacOS:Agent-YR [Trj], MacOS:AMOS-A [Trj], MacOS/Agent.T, Malware.OSX/Agent.aastz [or apvnq, bikjo, dplus, fqgok, hefho, hpdme, igrcu, jdnso, jinac, kgzuf, mewoo, miqkw, nqwim, nyoag, ownpu, pvour, snanh, tkpml, uzzyb, wojiq, xvddr, xveph, ylarv, ylask, zaxaz], Osx.Trojan-QQPass.QQRob.Azlw [or Eflw, Gajl, Itgl, Kflw, Qgil], OSX.Trojan.Agent.240XS0 [or Azlw, B01BNO, Bujl, Cgow, Ctgl, Dtgl, Gajl, Gjgl, Hkjl, Itgl, Jkjl, Ljgl, Lqil, Msmw, Ojgl, ORDPIH, Pqil, Psmw, Qcnw, Twhl, VZCCLC], OSX.Trojan.Gen, OSX.Trojan.Gen.2, OSX/Agent.2308!tr [or aastz, apvnq, bikjo, dplus, fqgok, hefho, hpdme, igrcu, J!tr.pws, jdnso, jinac, kgzuf, mewoo, miqkw, nqwim, nyoag, ownpu, pvour, snanh, tkpml, uzzyb, wojiq, xvddr, xveph, ylarv, ylask, zaxaz], OSX/InfoStl-CP, OSX/MacStealer.d, OSX/PSW.Agent.J, Other:Malware-gen [Trj], TROJ_FRS.0NA104DT23, Trojan-Spy.MAC.Atomic, Trojan:MacOS/Amos!MTB, Trojan:MacOS/Amos.A!MTB, Trojan:MacOS/AtomicSteal.A, Trojan:MacOS/Multiverze, Trojan:Win32/Vigorf.A, Trojan.MAC.Generic.112364 [or 112365, 112381, 112636, 112639, D1B6EC, D1B6FD, D1B7FC], Trojan.MacOS.S.Stealer.54058210, Trojan.MacOS.S.Stealer.54058274.A, Trojan.OSX.Agent, Trojan.OSX.Amos.4!c, Trojan.OSX.Generic.4!c, Trojan.Trojan.MAC.Stealer.3, Trojan/OSX.Agent.47995673 [or 54058210, 54058274], TrojanPSW:MacOS/MacStealer.da728306, UDS:DangerousObject.Multi.Generic, UDS:Trojan-PSW.OSX.Amos.gen
How can I learn more?
For additional technical details about this malware, see PhD. Phuc’s tweet thread that first brought it to light, Cyble’s technical write-up, and Phil Stokes’ technical write-up of another variant.
We also acknowledge MalwareHunterTeam and dustyfresh for their tweets with additional observations, which correlated with some of Intego’s research team’s findings.
 Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, including security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes. You can also subscribe to our e-mail newsletter and keep an eye here on The Mac Security Blog for the latest Apple security and privacy news. And don’t forget to follow Intego on your favorite social media channels:
Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, including security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes. You can also subscribe to our e-mail newsletter and keep an eye here on The Mac Security Blog for the latest Apple security and privacy news. And don’t forget to follow Intego on your favorite social media channels: ![]()
![]()
![]()
![]()
![]()
![]()
![]()

