How to Recognize Cybercrime and Protect Yourself Online
Posted on
by
Kirk McElhearn

Cybercriminals have become very sophisticated in recent years. Gone are the days when viruses targeted computers just for the fun of messing things up. Those “script kiddies” have grown up, and many now work for organized crime groups who use cybercrime as a means of making money. Lots of it.
In this article, I’m going to look at some of the most dangerous cyber threats, and explain how you can protect yourself. Protection is often just about education, about understanding these threats and how cybercriminals target you. So read on and learn how to recognize cybercrime and protect yourself online.
Phishing for Your Money
Cybercriminals want your money. To get it, digital bad guys target you in many ways. Often, they don’t directly attack your bank account or credit card, but try to get in by the back door. Online banking systems are quite secure, but if someone has your credentials, then the strongest security won’t protect you.
There’s an old saying that goes like this: If it sounds too good to be true, it probably is. In other words, that email you get offering to send you millions of dollars; or the one promising a big commission if you take on a new sales job; or even the messages touting deep discounts for a brand you like. They’re all bogus.
The safest way to work with this sort of email is to start by assuming they are all trying to trick you. Even emails from companies you have done business with could be frauds, “phishing” emails, trying to get you to give up your credentials to that company’s server. You see a lot of these, purporting to come from Apple, Amazon, PayPal, eBay, and others.
Phishing emails can be quite sophisticated, and can look authentic. But there are simple ways to tell if they are real or not. Read these tips to learn how to tell the real emails from the dangerous ones.
Identity Fraud
Your most valuable asset is your identity. And that’s what cybercriminals most want to own. Through phishing emails and bogus websites, they try to get you to enter your user name and password, or even your bank or credit card information, so they can take control of your identity.
The most valuable credentials these bad guys can get are the ones who unlock your iCloud or Google account. Because when they get access to all your stuff, they can send and receive emails from your account, potentially resetting passwords on your accounts, and they can pretend to be you to your friends and family.
A popular scam is the “bad news” or “stranded traveller” trick. A modern version of the Spanish Prisoner scam, which dates back to the 16th century, this involves getting access to someone’s email account, and sending messages to their friends saying that they’ve stuck in some distant country, have no money, and no credit cards. They generally ask to have money wired via Western Union, or some other hard-to-trace system. Lots of people fall for this, because the emails really do come from the friends’ accounts.
Another variant of this is the tech support scam. Your phone rings, and someone on the line says they’re calling from “Windows technical support,” or from “Facebook,” and claims that they’ve detected a problem with your computer. They try to get the user to install an app that provides remote access to the computer, at which point the scammer either gets access to files or personal data, or claims to fix problems with the computer, and requests a credit card number to pay for the service. If these people do get access to your files, though, they may use your identity to get further access to your bank accounts and other financial services. And if not, and you’ve given up a credit card number, that will quickly be used for malicious purposes.
Security Flaws in Outdated Software
We’ve said it here many times: One of the most important things you should do to protect yourself is keep your Macs and your iOS devices up to date. Update your apps as soon as you see there are new versions available. On iOS, this is easy, since all your apps come through the App Store. A glance at the App Store icon will tell you when there are updates.
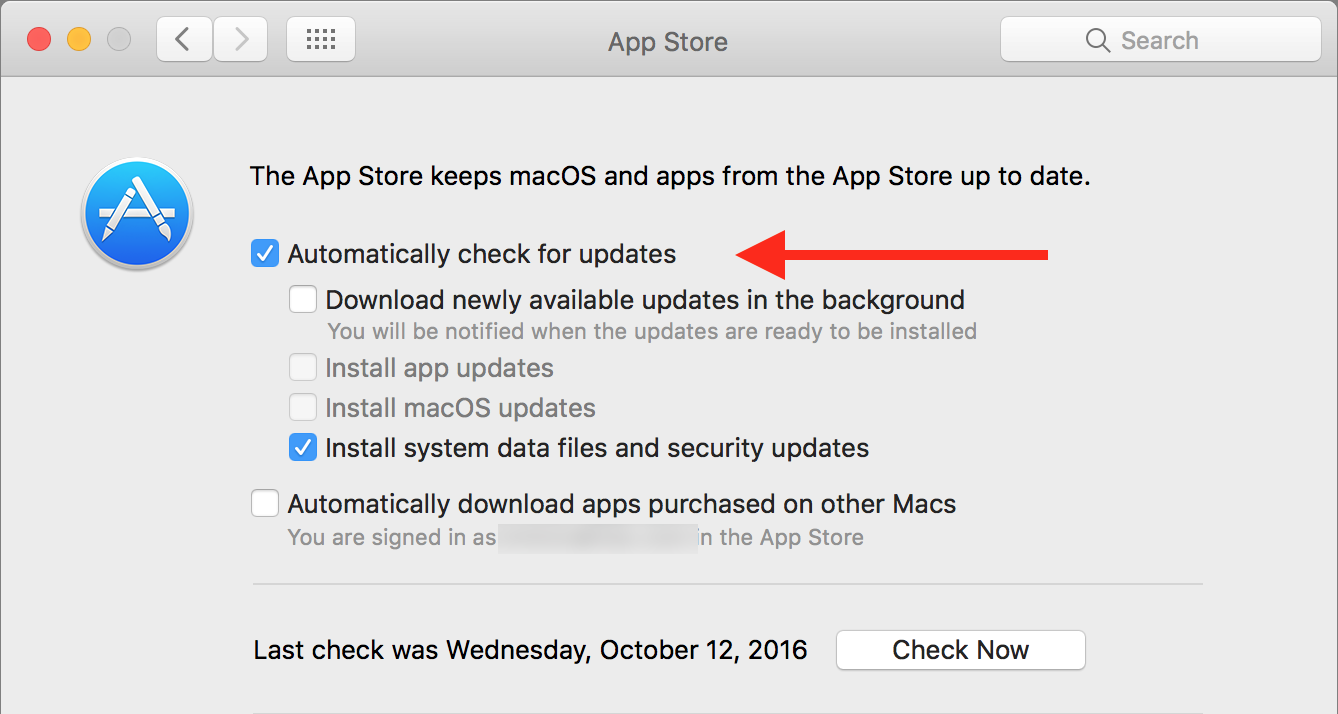
On your Mac, it’s a bit more complicated. There are Mac App Store apps, and you can have your Mac check for updates automatically. Go to System Preferences > App Store, then check Automatically check for updates.
But for third-party apps, you need to take the initiative. In most cases, apps you use will have a setting for automatic update checks. If not, you generally check for updates from the menu with the app’s name; choose Check for Updates.
The most important apps to keep up to date are your web browsers. Security flaws in these apps can have serious consequences, and can lead to malicious websites downloading malware. If you ever see a file or app in your Downloads folder that you don’t remember downloading, don’t open it. It could have come from a malicious website, and simply opening the file or launching the app could lead to an infection.
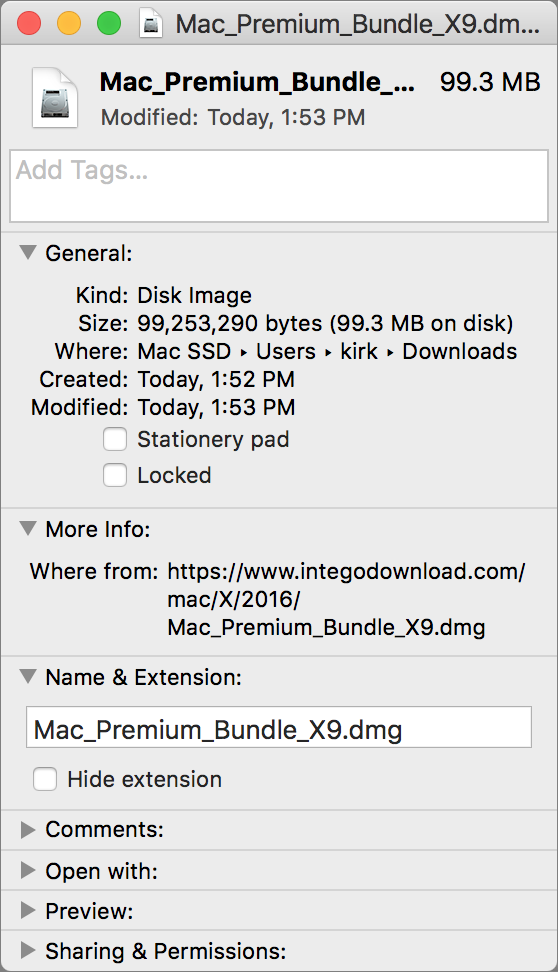
You can look at any item in the Finder to see where it downloaded from. Select a file, press Command-I, then look at in the More Info section. For example, in the screenshot below, you can see that this disk image, containing an installer for Intego Mac Premium Bundle X9, was downloaded from www.integodownload.com. If you don’t recognize the source of a downloaded file, and you don’t remember downloading it, delete it.
To update your web browsers:
Apple’s Safari gets its updates through the App Store app, so the settings I mentioned above will ensure that you’re up to date.
Google Chrome updates automatically, but you need to quit and relaunch your browser to apply updates. If you don’t restart your Mac often, and don’t quit Chrome, you may not have the latest version. Read this Google support document to find out how to ensure that you’re up to date.
Firefox has a setting, in Firefox > Preferences > Advanced > Update, that you can set to either automatically apply updates, or check for updates and ask you if you want to install them. As with Google Chrome, you will need to restart Firefox to ensure that it applies its updates.
Be Vigilant
The above examples highlight just how much is at risk when you use your computers and iOS devices. You need to be constantly vigilant: one email, one link, could open you up to potential harm. Learn how to spot phishing emails, make sure your identity is protected, don’t open unexpected downloads, and keep your web browsers up to date. These four tips will help make your online activities much safer.