Apple + Recommended + Security News
Clever Phishing Scam Targets Your Apple ID and Password
Posted on
by
Derek Erwin

Apple users need to be aware of an ongoing phishing campaign that appears to be ramping up efforts the past couple days. Scammers have found a clever way to generate phishing websites—and they’re after your Apple ID and password.
What’s happening is an active phishing campaign by way of fake Apple websites attempting to slurp up as many Apple IDs and passwords as possible. We’ve seen these types of phishing scams before, but the person or group behind this campaign appears to be very determined, creating tens and possibly hundreds of phishing websites all designed to steal your Apple ID and password.
Streams of these phishing pages have been uncovered the past two days, and subsequently posted to Twitter by vigilant users in the security community:
@malwrhunterteam @JAMESWT_MHT
Clever way to generate #phishing page:
http://account-secured-fraud[.]com pic.twitter.com/ec52jE0xPW— ExecuteMalware (@executemalware) August 1, 2016
#phishing verify-payment-account.]com @AppleSupport host https://t.co/UWZblkgnI4 cc @malwrhunterteam pic.twitter.com/g8HDVIwxRa
— JAMESWT (@JAMESWT_MHT) August 4, 2016
Upon discovery, many of these phishing websites have, of course, been shut down. But the scam isn’t over. New sites appear to be popping up, all registered under the same name, email address and country. One of the new scam sites is currently catching anti-phishing filters in some browsers, but not others.
For example, as of this writing Firefox does not alert visitors of a phishing attempt to one of the malicious sites:
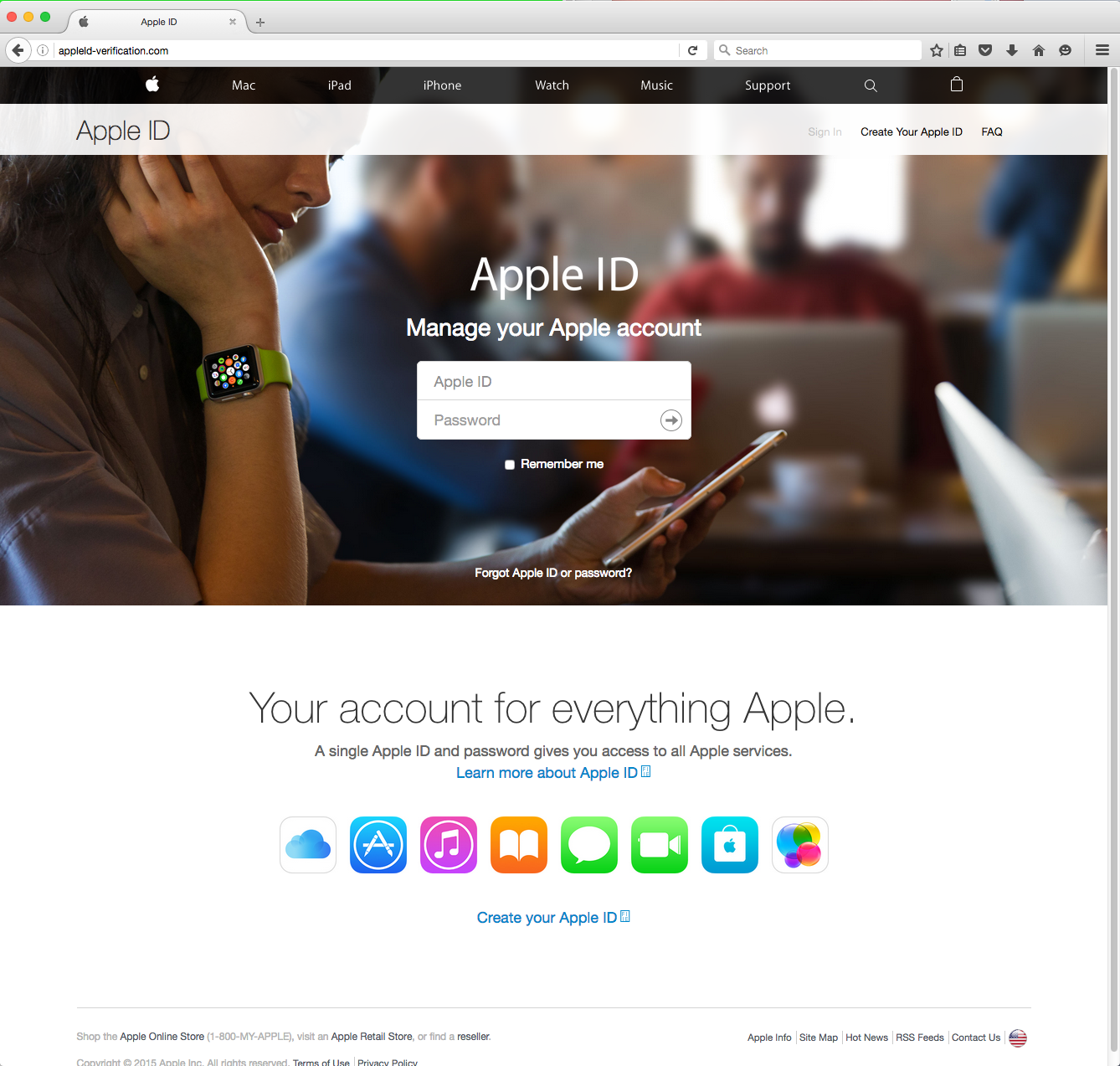
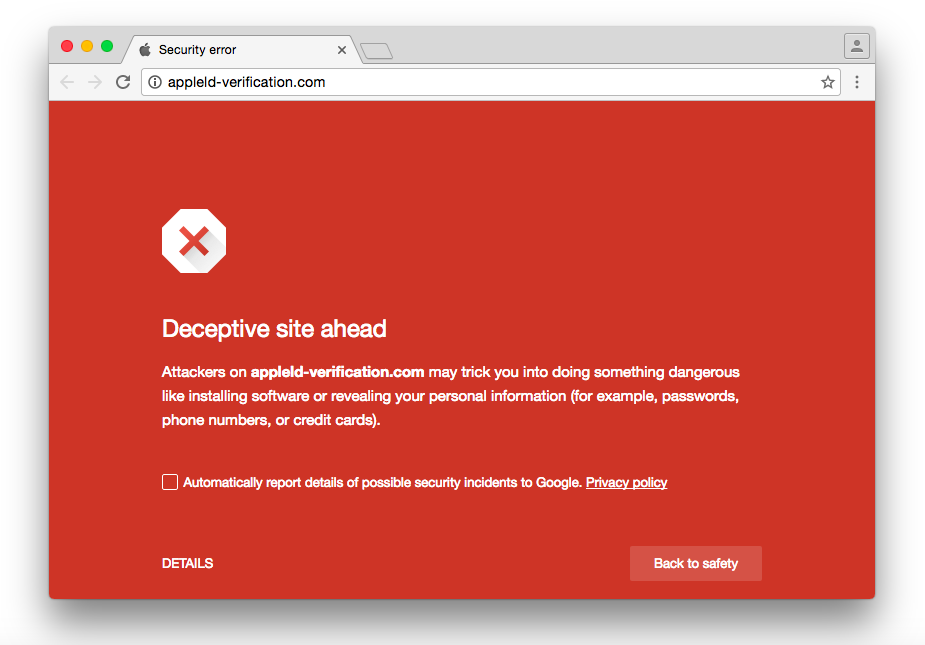
Google’s Chrome browser will alert visitors of the deceptive site:
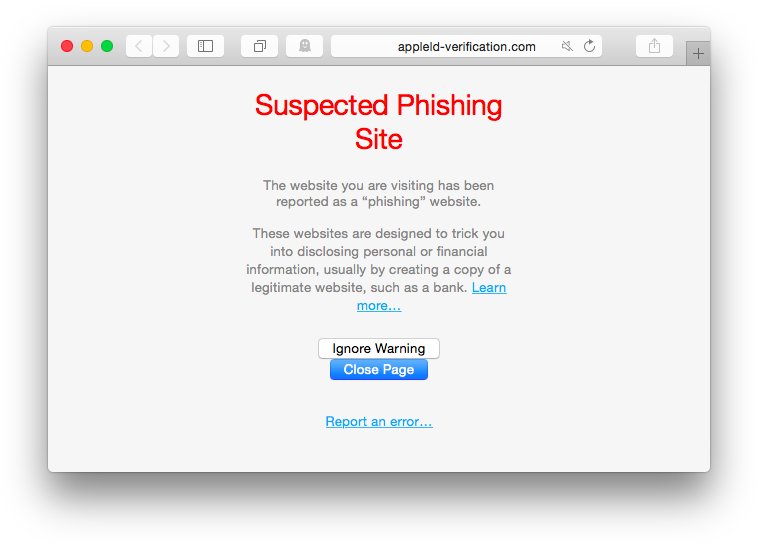
Apple’s Safari browser will also alert visitors of the suspected phishing site:
The duplicating phishing site, which is popping up under numerous URLs, is so deceptive it even offers legitimate links to Apple.com in order to trick unsuspecting visitors into thinking the page is legit.
Therefore, as we head into the weekend, we strongly encourage everyone to be vigilant about where you enter personal information online. We will keep you updated as this story evolves, but in the meantime, there are a few things to keep in mind to stay safe.
How scammers trick you into visiting phishing sites
Phishing scams have been causing serious problems for email users seemingly forever. Most of the time, phishing emails arrive in your inbox (or junk email, depending on your rules) pretending to from be your bank, utility company or other online payment system you use. Those messages request you to verify your accounts or to confirm your billing information, often leading victims to spoofed sites that ask you to update your credit card information or other identifying information.
Although such scams originated sometime around the year 1995, phishing emails and websites pretending to be from Apple are not as common, but they do happen.
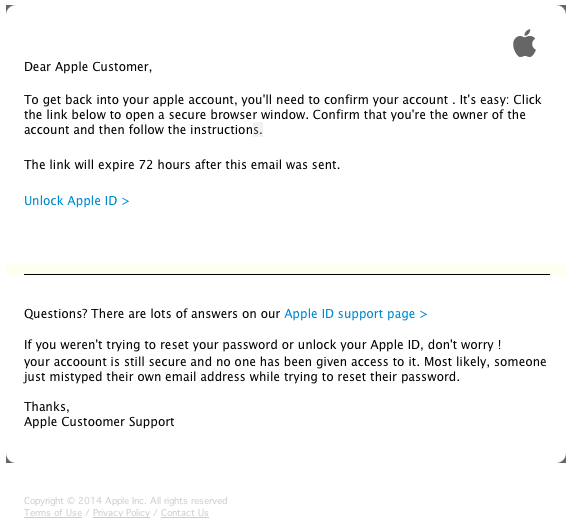
You have probably seen Apple phishing emails in your email junk box—unfortunately, some of these bogus phishing emails can look very real. Just the other day I got one from a scammer phishing for my Apple ID. An email claiming to be from “Apple Inc” erratically tells me: “Notice of Expiry of Your apple ID ref U-54614.”
The bogus email looked this:
The first thing I noticed about this email was that it was sent to about 100 different email addresses, all of which I could see in the “To:” line—a warning sign of fraudulent intentions, especially for an email wanting me to verify my Apple ID intended for someone “trying to reset your password.” You can also see in the email itself there are multiple grammatical errors, copyright dates are expired, and it presents a lame resemblance or what a valid email from Apple actually looks like.
Although the sender claims to be Apple Inc, a quick check to find out who the email is really from reveals it’s not coming from Apple:
It failed the grammar test and the “received from” test. And that’s all I needed to know before hitting the delete button. But not all phishing attempts are so easily identified.
Other phishing attempts come to you in the form of text messages in attempt to steal for your Apple ID and password. And some scams may use both SMS messages and emails, attacking you from multiple channels hoping to con you into believing this must be a valid attempt to save you in some way or another.
Phishing scams typically use social hacking exploit techniques to trick you into giving up your personal information. Sometimes they begin with pretexting: The attacker will contact you under a pretext, perhaps based on a very real situation, such as the theft of your iPhone or iPad, designed to give you the impression that since they know what they already know, they must be authorized to know more. And sometimes it works. “Hook, line and sinker,” as they say.
Take, for instance, Joonas Kiminki’s unfortunate tale of his stolen iPhone. This happened merely weeks ago, and the result was an active attempt to steal his identity—specifically his Apple ID and password. After Joonas’s iPhone was stolen, he got a new phone and life went back to normal. However, a couple of weeks later he received an SMS and an email notifying him that his phone was found, and to simply visit a website and login to find the phone’s location. You can read his experience on his blog at Hackernoon.com.
Fortunately, he didn’t fall for the scam, but this is a perfect example of the kinds of phishing attempts we’re seeing this week. Joonas cautioned why such scams would target your Apple ID, saying:
[Y]ou can’t activate an iPhone (or any iOS device for that matter) as long as it’s connected to someone’s iCloud account. However, when you steal a phone, you can perfect the crime by stealing the poor bastard’s identity as well. Then just log on to Find my iPhone, decouple the account from the device, and poof, you have an unlocked phone!
The moral of this story is that, if your phone is stolen, be aware that at some point in the near future you could receive an email and even an SMS message indicating that, surprise-surprise, your phone was “found,” and that you need to visit such-and-such website and enter your Apple ID credentials to view your iPhone’s location.
An example of this type of phishing page popped up just hours ago, and it may even be targeting Apple users whose iPhones were stolen:
@AppleSupport @malwrhunterteam @JAMESWT_MHT
findmyiphone-location-map[.]com
Those "tpyos" will kill you
🙂 pic.twitter.com/DNMotqoLf9— ExecuteMalware (@executemalware) August 5, 2016
How to protect yourself from phishing scams
There are many ways to protect yourself from phishing scams. Here are five of the best methods to protect your data and avoid getting duped:
- Stay aware of the types of websites you’re visiting and who you receive emails from, and double check the validity of a site before you enter any personal information.
- Ensure that your iPhone and iPad has its passcode enabled, preferably a six digit passcode, available on Apple devices running iOS 9, which makes it even harder to crack.
- You may even wish to enable the “Erase Data” passcode setting on your iPhone or iPad, which ensures that your device erases all data on it after 10 failed passcode attempts. (Just be sure to also backup your data to a cloud service provider, such as iCloud Drive, so if you lose your phone you can easily retrieve the data on it.)
- Add another layer of protection by enabling two-factor authentication for your Apple ID.
- Last but not least, some very sound advice from Joonas Kiminki: “If you ever lose your iPhone, iPad or iPod, be extra alert for upcoming identity theft attempts.”