4 Best Password Managers in 2025: How to choose the right one for you
Posted on
by
Jay Vrijenhoek, Kirk McElhearn and Joshua Long

Companies and websites are hacked all the time, and data they hold about users can be leaked. These leaks often contain usernames and passwords, and can also include other sensitive data, such as credit card numbers or personal information. You don’t always hear about these hacks; only breaches of the biggest companies makes headlines. Wikipedia has a partial list of notable data breaches, listing the largest hacks. Just in the past year, major organizations such as T-Mobile, the Red Cross, and IKEA were compromised. Was your data stored on their servers?
A password manager is software that allows you to create and store strong and very complex passwords so you won’t have to memorize them. All you need to do is memorize one really strong password to get access to all the others. There are quite a few password managers on the market today, so which one is right for you?
We discuss four trusted password managers in this article; each is cross-platform, available for Mac, Windows, and iPhone (and the first three are available for Android). While not a complete comparison of all major password managers out there, this article will teach you what to look for in a good password manager, and will provide a few options.
In this article:
- Why password managers are necessary
- What to look for in a password manager
- 4 password managers that meet the above criteria
- Other password manager options
- Password managers to avoid (a partial list)
- How can I learn more?
Why Password Managers are necessary
You might wonder why it isn’t good enough to simply memorize one seemingly strong (but memorable) password and use it for every site.
One reason is credential stuffing attacks. If one company’s password database is breached, your password may get exposed. This may be the result of a site storing passwords in a less-secure (or completely insecure) manner, or a determined attacker cracking your password. Either way, once your password is out there, attackers will try “credential stuffing” attacks: checking to see if anyone with the same username or e-mail address has reused that same password on other sites.
Imagine a scenario where a forum gets hacked, your password is leaked, and then an attacker uses that database of leaked usernames and passwords to break into your bank account or your e-mail account. If they can access your e-mail, all the rest of your accounts are one reset-password request away from being compromised, too. So even using a couple of different seemingly strong but memorable passwords isn’t a great idea.
How sites are supposed to store passwords
If proper procedures are followed, sites should store your account details (including your password and credit card info) both “hashed” and “salted” using a strong cryptographic cipher. Here’s what those terms mean:
- Salting adds random bits to your password
- Hashing creates a digital fingerprint that represents your password
Hashing is technically a one-way function, meaning that if the only thing a site’s administrator (or an attacker) knows is the hash, they cannot somehow reverse it and extract the original password. However, if the original password is weak — or if an attacker has enough processing power and time — the password may eventually be guessed, which would result in the same hash. If the hashes match, then the attacker has successfully guessed the password.
This is one reason why you often see stolen data from a hack surface weeks or months later. Cracking password hashes takes time, but a large percentage of passwords can be cracked very quickly as they are commonly used. If your password is Password1, it will be cracked in under a second, but if your password is something similar to ZK}8xR%YtrvVAk4nuad#Y9g}X (don’t use this exact password), it can take so much time it’s not worth the effort for those attempting to crack it (unless they’re specifically targeting you).
What could happen if a site’s password database gets breached
It’s safe to assume that once a company has been hacked and your account details are stolen, your password will be exposed at some point. Before that happens, you want to make sure there is enough time to react and change your password. In the event of a data breach, the company must first discover the hack, investigate it, and report it. This can take weeks or months, during which time you have no idea that hackers have been trying to crack your password. In some cases, sites may never discover — or never disclose — the fact that they were compromised.
Ideally, your password is strong enough that by the time you learn of a hack, the chances of it being cracked are slim. This brings me back to the previously mentioned, much more secure password example: ZK}8xR%YtrvVAk4nuad#Y9g}X. A password similar to that one will likely be among the last that is cracked, but as a user, it would be very difficult to remember it. (Again, don’t use that exact password, just in case attackers add it to a password dictionary.) If you have a hard time remembering one password like that, imagine trying to use unique, strong passwords on dozens of websites. There’s no way you can remember them all, and this is exactly where a password manager comes in.
What to look for in a Password Manager
- Reputation: You probably shouldn’t use a password manager that isn’t well known; remember that you’re trusting the app to handle very sensitive information. Also, you can try doing some searches using the name of the password manager and words like “hacked,” “security flaw,” “vulnerability,” etc. See what pops up and you’ll have a pretty good idea of the product’s track record.
- Platform support: You want your passwords to be available to you on every device you use. Having to run to your Mac every time you need a password on your Android phone isn’t useful. You may also want a password manager that supports your smart watch; this is a great way of having important passwords with you at all time.
- Syncing: If software is available for all your devices, you want your up-to-date password database available on all of them, at all times. Syncing through iCloud, Dropbox, or other services is essential to make this happen. Many password managers use their own servers for this.
- Browser integration: Opening your password manager then copying and pasting your usernames and passwords when you need them works, but it’s not ideal. You want the password manager to interface with your browser of choice so it can auto-fill names, passwords, and credit card details for you.
- Strong encryption: You want to be sure the password manager encrypts your password database properly using a strong cipher.
- Auto saving new and changed passwords: Whenever you change a password or create a new one on a website, your password manager should offer to update its database. This way, you don’t have to open your password manager after the fact and update or create the database entry manually.
- Security Audit: Knowing which passwords are several years old, which services might be using the same password (duplicates), or which passwords are weak and need to be updated with something stronger are great features to have in a password manager. It’s also useful to know which user names or emails have been found in data breaches, so you can change those passwords.
- Backup / Restore: The ability to back up your password database and restore it if needed is very important.
- Import / Export: If you switch from one password manager to another you want to be able to take your password database with you.
- Password generator: Since the password manager will remember all your passwords, you might as well make them long, complex, and strong. A password generator will do this for you very quickly.
4 Password Managers that meet the above criteria
Below are four password managers that meet all of the above criteria.
1Password
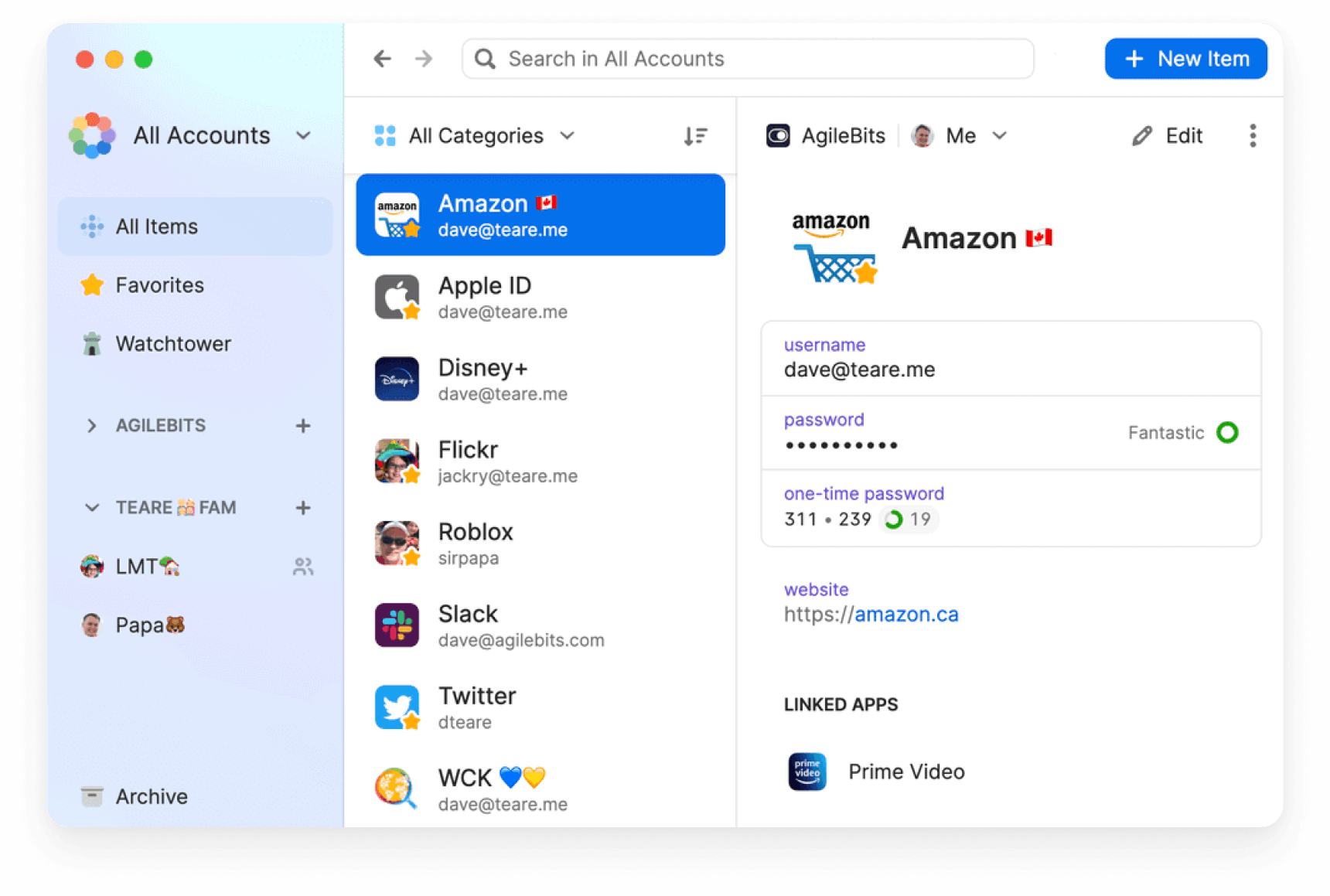
Cost: Pricing starts at $2.99/month billed annually ($36/year) for an individual, and $4.99/month ($60/year) for a family of 5 users. This includes access to 1Password for all available platforms, on as many devices as you use.
Platforms: Mac, Windows, Linux, iOS, iPadOS, watchOS, visionOS, Android, and browser plugins for Chrome, Safari, Firefox, and Brave. You can also access your 1Password database through a web browser.
1Password is one of the most popular password managers. It has a great reputation, offers strong encryption, and syncs through 1Password’s servers. Your passwords and password generator are quickly accessible from your Mac’s menu bar or browser plug-in. and 1Password’s Watchtower feature warns you if your credentials have shown up in data breaches. More pricing details and a full list of features are available on their website.
Bitwarden
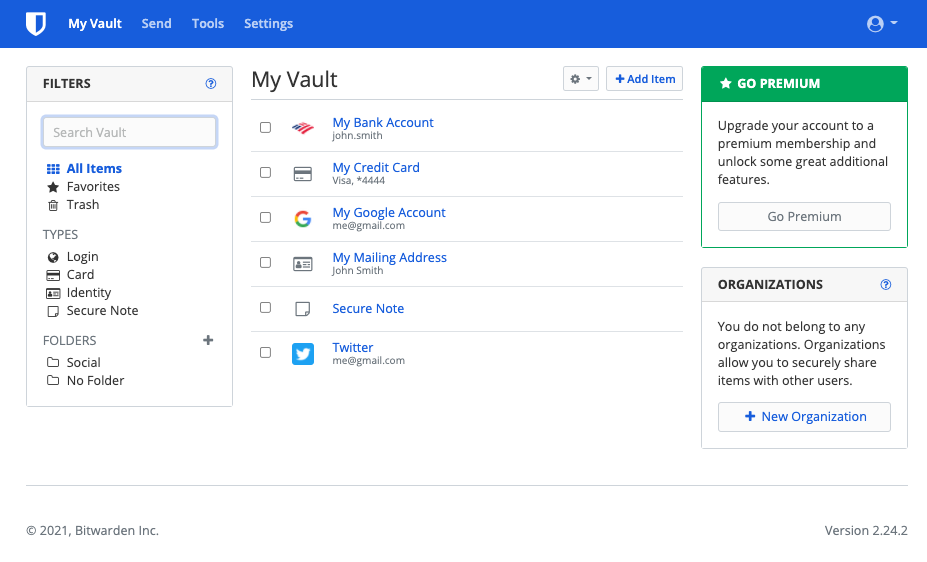
Cost: Free for personal use; a $10/year premium plan offers advanced features; a $40/year family plan offers premium features for up to 6 users
Platforms: macOS, Windows, Linux, iOS, iPadOS, watchOS, visionOS, Android, and browser plug-ins for Chrome, Firefox, Edge, Safari, Opera, Vivaldi, Brave, and Tor Browser. Bitwarden also offers a command-line interface for a variety of platforms, and you can access your Bitwarden database from the company’s website.
Bitwarden is an open source password manager that has a plan for individuals that claims to be “free forever.” Like other password managers, it handles passwords and other types of data, along with two-factor authentication codes, and offers a “username data breach report,” as part of its free plan. The $10/year plan offers a full range of features, and family and enterprise plans are also available. A full list of its security features are available on their website.
Dashlane
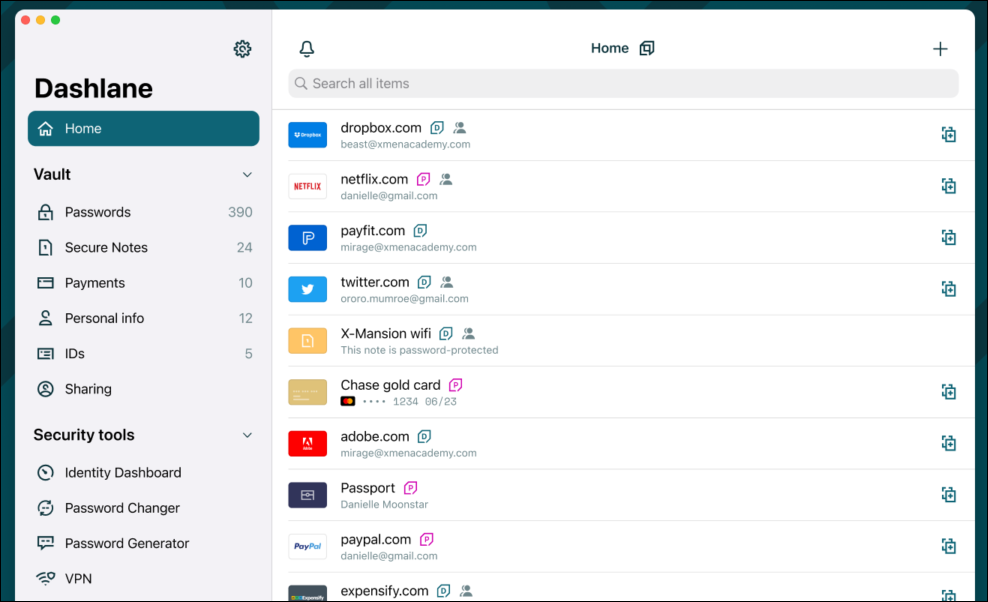
Cost: Dashlane has a free plan, which provides basic password manager features for a single device, a Premium plan at $4.99/month (i.e. $60/year) and a Family plan at $7.49/month (i.e. $90/year) billed annually. The Premium plan includes access to a VPN and Dark Web Monitoring, while the Family plan includes one Premium account and 9 other users that get all Premium features except for the VPN. There is also a range of business plans.
Platforms: Web app, Android app, and App Store apps for iPhone and Apple Watch, iPad, Mac (including a Safari extension), and Apple Vision Pro.
Dashlane is another popular password manager. It’s available as a web app for all major browsers on Mac, Windows, and Linux, and apps are available for Android and Apple operating systems; the iOS app also includes an app for the Apple Watch. The company got rid of its desktop app early in 2022 to focus on its web app, but later resurrected its macOS app. The web app version can be practical because it allows you to access your passwords on any device.
Passwords are encrypted and stored on the Dashlane server, and you can protect access with two-factor authentication. This is important with Dashlane because of the web access; other password managers with desktop apps store their passwords locally, so someone would need access both to your device and to your master password to access your passwords. Dashlane emergency access allows you to nominate someone who can unlock your account if you have lost or forgotten your master password. Dashlane’s Dark Web Monitoring (available with the Premium plan) checks to see if your personal information has been compromised. More pricing details and a full list of features are available on their website.
Apple Passwords (iCloud Keychain)
Cost: Free; included with all Apple ID accounts
Platforms: macOS, iOS, iPadOS, visionOS, Windows, Safari (note: doesn’t support non-Safari desktop browsers, Android, ChromeOS, or Linux)
If you mainly use Apple products, another option that might work for you is Apple Passwords (formerly known as iCloud Keychain). With syncing across all your Apple devices, the latest version of Apple Passwords includes support for credit cards and two-factor authentication codes, bringing its feature set up to par with (at least the free features of) many other password managers. You can use it natively on macOS, iOS, iPadOS, and visionOS. You can even get iCloud Passwords on Windows PCs using iCloud for Windows. However, there is no web access, so you won’t be able to directly access your passwords on other devices such as Chromebooks or Android phones or tablets.
Check out our comprehensive review of how iCloud Keychain works for macOS and iOS.
Other Password Manager options
There are many other password managers out there; a couple additional options that have been around for more than a decade include Keeper and RoboForm. (If you happen to use ExpressVPN, there’s also the relatively new ExpressVPN Keys; it’s a password manager that comes bundled with your VPN subscription.)
Whichever option you choose, make sure it works for you and meets all your needs. If you’ve never used a password manager before, there will be a small adjustment period. It may also take some time to consolidate all your passwords, but it’s worth it!
Password managers to avoid (a partial list)
In a previous version of this article (originally published more than a decade ago, way back in 2012), we mentioned several other password managers that were available at the time. A lot of time has passed since then, and the industry has learned a lot from recent events like the LassPass hack of 2022. In addition to LastPass, any password managers that are no longer being updated, or no longer available to download, should be presumed less safe (or unsafe) to use. They may use less-secure encryption methods, and at the very least, older apps may have compatibility problems with the latest operating systems.
If you use any of the password managers listed below, we recommend that you:
- Switch to another password manager that you trust, like the ones we’ve covered above: 1Password, Bitwarden, Dashlane, Apple Passwords, Keeper, RoboForm, or ExpressVPN Keys.
- Change all your passwords. Your old password manager may not have been storing your passwords securely, so changing all of your passwords is important. Just make sure you do this step after switching to a trusted password manager first; you shouldn’t put any new passwords into an old app.
Here is a partial list of some now-defunct (or no longer safe to use) password managers:
- Access Manager by Black Cat Systems was a standalone Windows password manager once recommended by security expert Steve Gibson in 2005; it was last updated in 2013, and its homepage went offline in 2022, so we do not recommend using it.
- Avast Passwords was effectively discontinued in 2020 and should no longer be used.
- CyberGhost Password Manager was discontinued in 2022 and should no longer be used.
- DataVault by Ascendo Inc. has macOS and iOS/iPadOS/watchOS apps that were last updated in 2020, and a Windows app that was last updated in 2017, so we do not recommend using them.
- Encryptr by SpiderOak was discontinued in 2021, so we do not recommend using it.
- eWallet by Gator Corporation (aka Claria Corporation) is a discontinued product developed by a former spyware vendor, so we do not recommend using it.
- Firefox Lockwise (previously known as Firefox Lockbox) by Mozilla was discontinued in 2021, so we do not recommend using the associated iOS or Android apps. (Mozilla still allows password synchronization between desktop and mobile versions of Firefox via Firefox Sync.)
- got password? by Edash was a standalone Windows password manager; it was last updated in 1997 and used weak encryption, so we do not recommend using it.
- KeePassX (not to be confused with KeePassXC, which is still being updated as of 2024) was a Linux port of KeePass, an open-source password manager; KeePassX was discontinued in 2021, so we do not recommend using it.
- KYPS (“Keep Your Password Secret”) was a Web-based password management service that was discontinued in 2012; while it is no longer possible to use it, we’re including it in this list to note that any passwords that may have been stored in KYPS should be changed.
- LastPass suffered a catastrophic breach in August 2022 that put users’ password vaults and personal information at risk. Although the company hasn’t gone out of business (yet), we can no longer recommend LastPass, and we recommend that all LastPass users switch to another password manager and then change all their passwords.
- Mitro was a Twitter-owned, browser extension-based password manager that was discontinued in 2015 and should no longer be used.
- MobilePad by Vision Technology Consulting was a standalone app for (pre-iPhone) Java-enabled phones; it was last updated in 2005 (the year Gibson recommended it), and its homepage went offline in 2009, so we do not recommend using it.
- Myki was a cross-platform password manager that was discontinued in 2022, so we do not recommend using it.
- Offer Assistant by Billeo was a browser-based password manager that was discontinued in 2012, so we do not recommend using it.
- Oubliette was a standalone Windows password manager once recommended by Gibson in 2005; it was last updated in 2003, and its homepage went offline in 2017, so we do not recommend using it.
- Passwords Plus by DataViz was discontinued in 2022 and should no longer be used.
- Personal Passworder by DVAsoft was a standalone Windows password manager once recommended by Gibson in 2005; it was last updated in 2008 and its homepage went offline in 2016, so we do not recommend using it.
- PINs by Mirek Wojtowicz was a standalone Windows password manager once recommended by Gibson in 2005; it was last updated in 2003, so we do not recommend using it.
- SafeWallet by SBSH Mobile Software was last updated in 2013, and its homepage went offline in 2014, so we no longer recommend using it.
- STRIP and STRIP Lite by Zetetic LLC (aka “Secure Tool for Recalling Important Passwords”) have been replaced by the company’s newer password manager, Codebook. We do not recommend using the older STRIP apps.
- Wallet by Acrylic Software has apps that were last updated in 2018 (iOS) and 2017 (macOS), so we do not recommend using it.
How can I learn more?
 Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, including security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, including security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
You can also subscribe to our e-mail newsletter and keep an eye here on The Mac Security Blog for the latest Apple security and privacy news. And don’t forget to follow Intego on your favorite social media channels: ![]()
![]()
![]()
![]()
![]()
![]()
![]()