Are iOS Shortcuts safe? Reports of risks surface
Posted on
by
Joshua Long

UPDATE 2: Apple has released a new version of Shortcuts to address these bugs; check the App Store for the update.
Reports have surfaced recently that warn of apparent vulnerabilities in Shortcuts, a new app and feature introduced in iOS 12 that lets users create a custom series of automated tasks.
The reports began surfacing on January 19, when a developer tweeted the following: (UPDATE 1: The Twitter account has since changed to a protected status, so the tweets’ screenshots are no longer visible to the public.)
Shortcuts can even read files protected by the sandbox, by using a path traversal vulnerability incombination with insufficient sandboxing on folders. pic.twitter.com/fOQuTfheGv
— UKERN Soft₩аre (@userlandkernel) January 20, 2019
The developer also claimed to be able to view the folder that contains the SMS text message database files:
Works! pic.twitter.com/VoSCHTZQNh
— UKERN Soft₩аre (@userlandkernel) January 20, 2019
The tweets went almost entirely unnoticed by the Apple-focused press, having only been mentioned in a brief article on the German-language site Heise a day later.
A week after the tweets were posted, other developers began posting to the Reddit community /r/Shortcuts about their own follow-up investigations, warning of the same significant risks in the way Shortcuts behaves.
One of the Reddit threads makes further claims about a sandbox escape (essentially meaning that shortcuts can do things they shouldn’t be permitted to do) that allows “certain parts of the filesystem [to be] writable” by way of a directory traversal attack, enabling the creation of numerous large files that can fill up the iOS device’s System storage to capacity. The same redditor claims that while testing this attack, his iPhone began to overheat.
Follow up, still going, phone is overheating as well pic.twitter.com/wWLZLnFinA
— Ashton (@Alphalaneous) January 27, 2019
This could be described as a type of denial-of-service attack (DoS), since over-full storage and overheating can each cause an iOS device to stop functioning properly. Being able to create a DoS-causing shortcut is bad enough, but the following day another redditor described a more worrisome attack.
A separate thread warned that “Shortcuts is way more powerful than it should be.” The redditor who started this thread claimed to have been “messing around with url schemes such as ‘file://’ and ‘../’, when I came across the delete file action.” Allegedly, this developer was able to execute another directory traversal attack to delete /System/Library/CoreServices/prdaily, a behind-the-scenes system utility that iOS uses to clean user caches when a device begins to run low on available storage.
Intego reached out to Apple’s product security and media teams on Monday to alert them of the issues and to request a comment, but Apple has not yet responded. (This is not terribly surprising given that Apple was just beginning to become aware of the FaceTime spying bug around the same time.) Other news sources had not yet picked up on this story at the time of the publication of this article, but given that these details are already openly available for potential attackers to find and exploit, we felt it was important to make this public service announcement to Shortcuts users. UPDATE 1: On February 6, an Apple Product Security representative finally responded to our request for comment, but only said, “We are already aware of these issues.” The representative did not offer any clarification about whether, or when, the issues would be fixed.
More research on the safety of Shortcuts
Coincidentally, two other stories broke this week about Shortcuts safety.
On Wednesday, AppleInsider wrote about a series of tweets that a developer had posted a week earlier (referring to someone else’s research that perhaps, although not necessarily, may have been inspired by the first research described above).
From highly personal contacts, names you've typed into iMessage, addresses, browsing history, app usage, file contents
I'd even loaded the entire text of Dickens' David Copperfield into Codea recently to test editing performance. Names and places from the story were indexed /2 pic.twitter.com/2bfIr9aqCS
— Simeon (@twolivesleft) January 23, 2019
You couldn't expect a reasonable user to know what they were agreeing to run when receiving an Apple-hosted link to this shortcut
With automatic scheduling of shortcuts (https://t.co/S5l1M3Rjyx) you could possibly trick someone into running a key logger /4
— Simeon (@twolivesleft) January 23, 2019
The developer was referring to a proof-of-concept (PoC) shortcut he had been shown that was capable of stealing data such as “contacts, names you’ve typed into iMessage, addresses, browsing history, app usage, [and] file contents.” A week later, on the same day that the AppleInsider piece was published, the PoC was posted publicly online by its creator, who claimed that Apple does not view the PoC’s behavior as a bug, but rather “as intended behavior.” (Before anyone asks in the comments: No, we will not share a link to the PoC here, nor will we approve comments asking for, or containing, a link to it.)
On Thursday, threat researchers at IBM warned about another potential attack involving Shortcuts, claiming that, (as reported by eWeek) “it is possible to use a Siri Shortcut [sic] for malicious purposes, including tricking a user into paying a fee to avoid having his or her information stolen in an attack known as scareware.” The IBM researchers said that they have not yet seen evidence of Shortcuts-based scareware attacks in the wild.
How to avoid Shortcuts-related attacks
Thankfully, iOS 12 doesn’t come with the new Shortcuts app preinstalled; users have to know about it and seek to download it from the App Store. You could choose to avoid downloading the Shortcuts app if you don’t have it installed, or you could delete it if you’ve already downloaded it and you don’t plan to use it.
If you decide to use Apple’s Shortcuts app, you will notice that the app includes a Gallery where you can find some suggested, Apple-curated shortcuts that should be safe to use. Where things get dicey, however, is with shortcuts sourced from a third party.
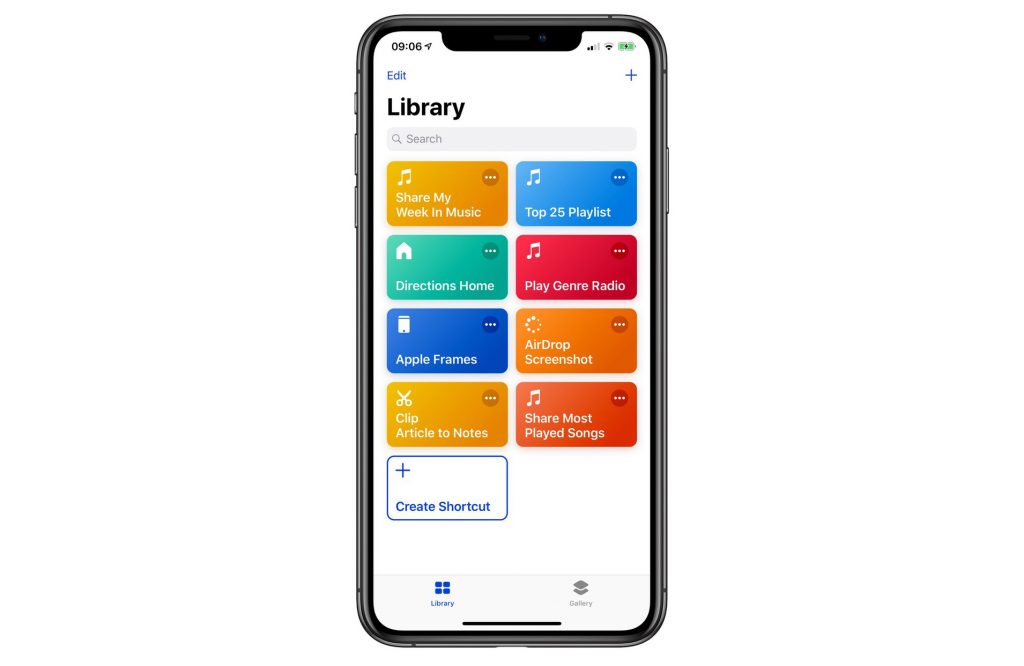 The Shortcuts app has a Gallery (bottom right) with a curated list.
The Shortcuts app has a Gallery (bottom right) with a curated list.
Apple has made Shortcuts uncharacteristically open to unauthorized developers and third-party distribution sites, making Shortcuts on iOS feel more akin to the Mac ecosystem. And while some third-party sites may curate and verify the safety of user-submitted shortcuts, other sites may not have the same standards, and still others could theoretically be designed to outright deceive you.
The takeaway is that if you decide to use Shortcuts, be sure to stick with developing your own shortcuts or using ones that Apple has curated in its Gallery—and if you really need to use a third-party shortcut for some reason, do your homework and try to make sure it’s safe first.
How can I learn more?
 Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
You can also subscribe to our e-mail newsletter and keep an eye here on Mac Security Blog for the latest Apple security and privacy news. And don’t forget to follow Intego on your favorite social media channels: Facebook, Instagram, Twitter, and YouTube.

