ShadowVault is the latest Mac data-stealer malware, reportedly
Posted on
by
Joshua Long

ShadowVault, a new variety of data-stealing malware, recently arrived on the Mac and made headlines in the Apple press this week. Here’s what we know about it so far.
What is ShadowVault malware, and what does it do?
Originally released to the public on June 3, 2023, ShadowVault purports to be “macOS Stealer” malware. It is sold as a sort of ‘malware as a service,’ meaning malicious parties wanting access to it must pay the distributor $500 per month.
ShadowVault was first discovered on a Russian-language cybercrime and hacking forum called XSS (formerly known as DaMaGeLaB).
A YouTube video showcasing the malware in action was released on June 8 (credit to macOS security researcher Phil Stokes for this discovery). This video claims to show a ShadowVault app extracting a variety of data from a Mac, then reporting back to the command-and-control (C&C) server with a data dump in a little over a minute. That report, visible to the C&C operator, appears to show the victim’s password and a summary of what data was extracted, including cookies, passwords, credit card numbers, and cryptocurrency wallets.
The video makes mention of a Telegram channel with links to product pages for the malware in Russian and English.
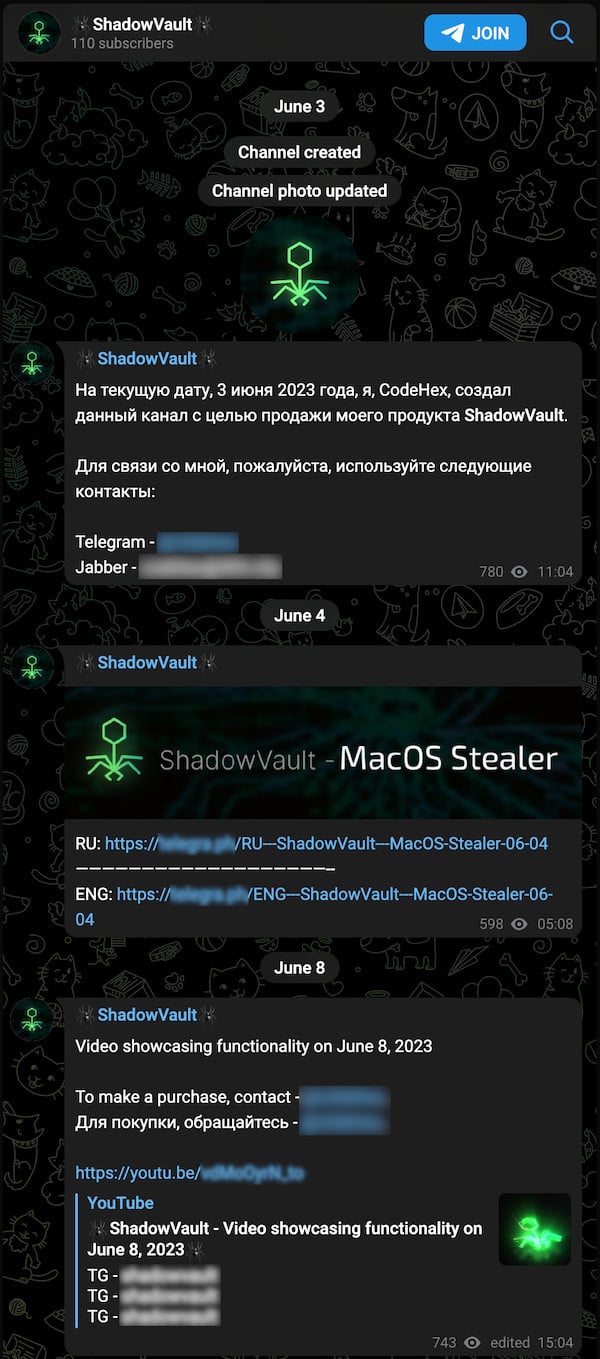
ShadowVault’s Telegram channel.
Those product pages claim that the malware can extract passwords from the macOS Keychain, Chromium-based browsers (such as Google Chrome, Microsoft Edge, Brave, Opera, Vivaldi, and others), and Firefox. They also claim that ShadowVault can do “Telegram grabbing,” which presumably means exfiltrating messages from the Mac version of Telegram, an encrypted messaging app.
How can one remove or prevent Mac malware like ShadowVault?
So far, no samples have been found that have been definitively identified as being associated with ShadowVault. We asked around within the Mac malware analysis community, and nobody had any confirmed samples. Additionally, no sales of the malware have yet been confirmed.
However, Intego has recently added detection for new generic stealer and keychain-dumping malware; these new threats could potentially be one and the same. It’s also possible that ShadowVault may simply be a repackaged version of existing malware that’s already in the wild, perhaps based on open-source Mac malware packages.
 Intego VirusBarrier X9, included with Intego’s Mac Premium Bundle X9, can protect against, detect, and eliminate Mac malware, including malware similar to ShadowVault.
Intego VirusBarrier X9, included with Intego’s Mac Premium Bundle X9, can protect against, detect, and eliminate Mac malware, including malware similar to ShadowVault.
If you believe your Mac may be infected—or to prevent future infections—use trusted antivirus software. VirusBarrier is award-winning antivirus software, designed by Mac security experts, that includes real-time protection. It’s compatible with a variety of Mac hardware and OS versions, including the latest Apple silicon Macs running macOS Ventura.
Additionally, if you use a Windows PC, Intego Antivirus for Windows can keep your computer protected from data stealers and other PC malware.
VirusBarrier X6, X7, and X8 on older Mac OS X versions also provide protection. Note, however, that it is best to upgrade to the latest versions of macOS and VirusBarrier; this will help ensure your Mac gets all the latest security updates from Apple.
How can I learn more?
For a few additional details about the ShadowVault malware, you can read the original write-up by Guardz from July 10. We would also like to thank Phil Stokes for helping to track down additional information about ShadowVault that was not included in the original report.
Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, including security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
You can also subscribe to our e-mail newsletter and keep an eye here on The Mac Security Blog for the latest Apple security and privacy news. And don’t forget to follow Intego on your favorite social media channels: ![]()
![]()
![]()
![]()
![]()
![]()
![]()

