Recommended + Security & Privacy + Security News
Porn Blackmail Scam Rattles Mac Users: What You Need to Know
Posted on
by
Derek Erwin
Our experiences online today seem, at times, much like life was probably like in the Wild West about 145 years ago. Today, online thieves are out to get as much from you as possible. And when you connect to the Internet, you’re vulnerable to malware and hackers — it simply does not matter what computer or operating system you’re using.
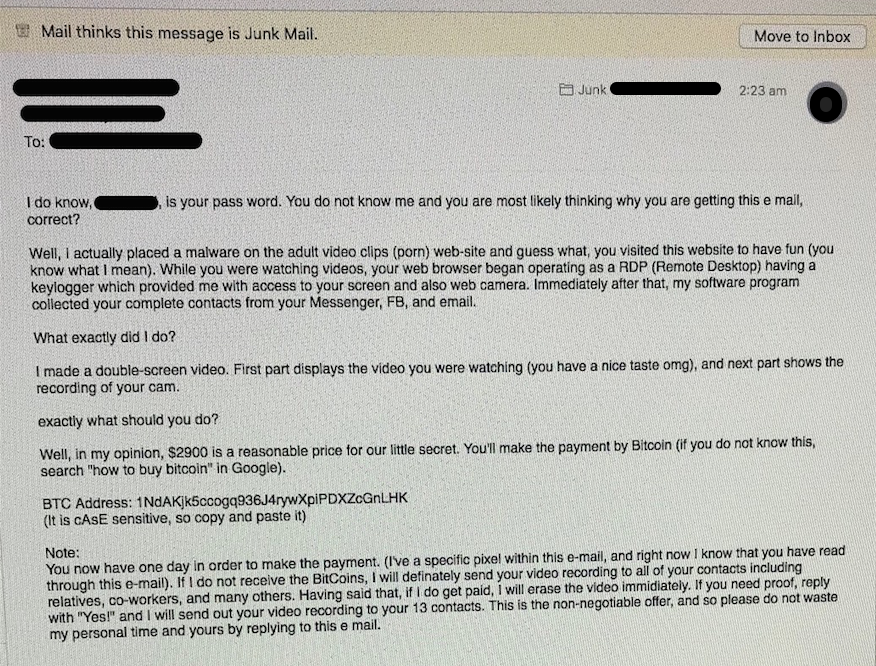
The latest trick up cybercriminal’s sleeves is a ploy utilizing a mix of social engineering and blackmail, a scam via email from someone claiming to have hacked your computer’s webcam and recorded your activities while you allegedly watched porn. The email claims you downloaded their virus while watching porn, siphoning your contacts, and they threaten to send the video of you to all of your friends, family and coworkers — unless you pay a ransom in Bitcoin (BTC) digital currency. (We’ve seen demands of anywhere between $300 to $3,000 USD or higher.)
Although “sextortion” schemes have been widespread in various parts of the world — Australia and the Middle East — we have recently seen these showing up in large numbers across the United States. For this reason, we feel it’s important to clarify a few things and provide assistance on the best way to protect yourself.
How the porn blackmail sextortion scam works
How would you react if you received an email from someone claiming to have hacked your webcam and recorded your most private moments? What if they threatened you with blackmail by sharing the video with your relatives unless you payed them money? Would you pay the ransom? Even if you never viewed porn, what if they made similar threats to reveal your private details of all your emails? And what does it mean if the email includes a real password that you’ve used in the past? Should you be concerned?
This is precisely the predicament a growing number of our customers discovered themselves in over the past few weeks, and it seems this scam is spreading at an alarming rate. The Intego Support Team has received an eyebrow raising uptick in calls related to porn blackmail scams, and many of you have contacted us for help on the best way to proceed. As part of our investigation, we gathered a few example emails to see what tricks the scammer’s use in attempt to con people out of their hard earned money.
Here is an example scam email that some of our customers have received:
What to do if you received a porn blackmail email
If you have received such an email, it’s important to know that you most likely have not been hacked. While, indeed, BBC News previously uncovered an entire industry centered on the buying and selling of access to compromised webcams, particularly those owned by women, these porn blackmail emails appear to be fake. Yes, your Mac’s camera can be hacked, but in the case of the porn blackmail scam, we have no indication that the threat is real. The video the scammer’s claim to have of you is not real. It doesn’t exist.
But what if the scam email includes a password that you’ve used in the past? Should you be concerned? The answer is yes and no.
No, you shouldn’t be concerned that your Mac was hacked and there is a video of you watching porn. We want to reiterate that this is a scam designed to scare you into sending the criminal money. The truth is there is nothing else in the email that indicates they know anything about you personally; for instance, it’s not addressed to you by name and there are no details about what site you supposedly visited and when. There is also no screenshot of you or any valid proof that they have a video of you. Think about it: If they wanted to really scare you into paying a ransom, wouldn’t they show you a compromising screenshot or other proof that their threat is in fact real?
Yes, you should be concerned that your password was leaked through a data breach. We’ve reported on a number of major data breaches in which emails and passwords have been hacked, affecting hundred of millions of people, and if you were a victim of such a crime, then your old password may be in the hands of bad guys. That password in the email was likely one of the accounts affected by a data breach.
By adding a password that you either currently still use or have used in the past, the scammer is using a tried and true social engineering tactic to give you the impression that they know more about you than they mention in the email. The attacker is reaching out to you under a pretext, leveraging information they previously acquired about you to give the impression that, since they have your password, they must also have that private video they claim to have recorded.
How to protect yourself from the porn blackmail scam
These blackmail scam emails are a great example why a layered defense strategy is so handy. We’ve already covered why using a password manager can help you safely manage your passwords, some of which will inform you if a password you use has been compromised. But what else can you do?
If one of these blackmail scam emails land in your junk box (or even inbox), there are a few things you can do. Take these steps to protect yourself:
- Ignore and delete the emails — do not pay the ransom. If you fail to pay, no video or images will be sent to your contacts; after all, the video doesn’t exist.
- Scan your Mac for malware and ransomware with Intego VirusBarrier. If you prefer free Mac antivirus, we recommend that you download and install VirusBarrier Scanner from the Mac App Store. (For details on the difference between our paid antivirus and our free antivirus, see: Why Your Antivirus Needs Real-Time Scanning.)
- Update your account passwords online, particularly if it was mentioned in the email message, since it was most likely stolen as part of a broader data breach in the past and the password is no longer secure. Take note that it’s imperative for you to be wary of which websites you create an account with since the password could be stolen. Only create accounts with trusted sources.
Further reading:
- CIA Porn Accusation Emails: Here’s What Mac Users Need to Know
- Your Mac’s Camera Can Be Hacked
- Creepy Spam Call Leaves Voicemail Phishing for iCloud Logins
- Social Engineering: Beware of ‘Tech Support’ Scams
How can I learn more?
 Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, including security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, including security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
You can also subscribe to our e-mail newsletter and keep an eye here on The Mac Security Blog for the latest Apple security and privacy news. And don’t forget to follow Intego on your favorite social media channels: ![]()
![]()
![]()
![]()
![]()
![]()
![]()


