CIA porn accusation emails: Here’s what Mac users need to know
Posted on
by
Craig Grannell
Have you received an e-mail accusing you of pedophilia and demanding a ransom? Read on to find out what to do.
Email scams are commonplace; you’ve likely received countless over the years. Lately these scams have strayed into rather unpleasant territory: blackmail centered around porn. These scams are sometimes known as sextortion.
These emails take various forms. The most recent we’ve seen has you being sent a case number by a purported CIA agent, stating that your personal details are among those of 2,000 people about to be arrested as part of an international pedophilia sting; but, as ‘luck’ would have it, the sender is crooked, and so will remove your details if you send them ten grand in Bitcoins. If that sounds dodgy — spoiler! — it’s because it is dodgy.
So you can see for yourself (and possibly compare the content with emails you’ve already received), the full text of one such communication is as follows:
Subject: Central Intelligence Agency – Case #69723148
From: [email protected]
Case #69723148
Distribution and storage of pornographic electronic materials involving underage children.
My name is Pasty Faust and I am a technical collection officer working for Central Intelligence Agency.
It has come to my attention that your personal details including your email address ([your email address]) are listed in case #69723148.
The following details are listed in the document’s attachment:
- Your personal details,
- Home address,
- Work address,
- List of relatives and their contact information.
Case #69723148 is part of a large international operation set to arrest more than 2000 individuals suspected of paedophilia in 27 countries.
The data which could be used to acquire your personal information:
- Your ISP web browsing history,
- DNS queries history and connection logs,
- Deep web .onion browsing and/or connection sharing,
- Online chat-room logs,
- Social media activity log.
The first arrests are scheduled for April 8, 2019.
Why am I contacting you ?
I read the documentation and I know you are a wealthy person who may be concerned about reputation.
I am one of several people who have access to those documents and I have enough security clearance to amend and remove your details from this case. Here is my proposition.
Transfer exactly $10,000 USD (ten thousand dollars – about 2.5 BTC) through Bitcoin network to this special bitcoin address:
[Bitcoin address redacted]
You can transfer funds with online bitcoin exchanges such as Coinbase, Bitstamp or Coinmama. The deadline is March 27, 2019 (I need few days to access and edit the files).
Upon confirming your transfer I will take care of all the files linked to you and you can rest assured no one will bother you.
Please do not contact me. I will contact you and confirm only when I see the valid transfer.
Regards,
Pasty Faust
Technical Collection Officer
Directorate of Science and Technology
Central Intelligence Agency
Variations of the e-mail include different names of the alleged sender (e.g. Antionette Carbajal, Carla Jernigan, Carmelo Kenyon, Devon Babin, Hong Lees, Huey Ferguson, Page Fogle, Robyn Mckinney, Roxana Mackay, Pasty Faust, Sadye Crawley, Sandie Curtin), implying that the name is randomized for each e-mail that’s sent.
Similarly, the return address subdomains (e.g. the “gov3.” in the example above) change with each e-mail, although many of the e-mails seen so far have come from a subdomain of one of various fake CIA domains containing “cia” and “-gov” or “-govn” (examples include cia-gov-int.ga, cia-gov-int.gq, cia-gov.ga, cia-govn.cf, cia-govn.ga, cia-govn.ml, or cia-us-govn.ga).
Porn blackmail variants – and should you be afraid?
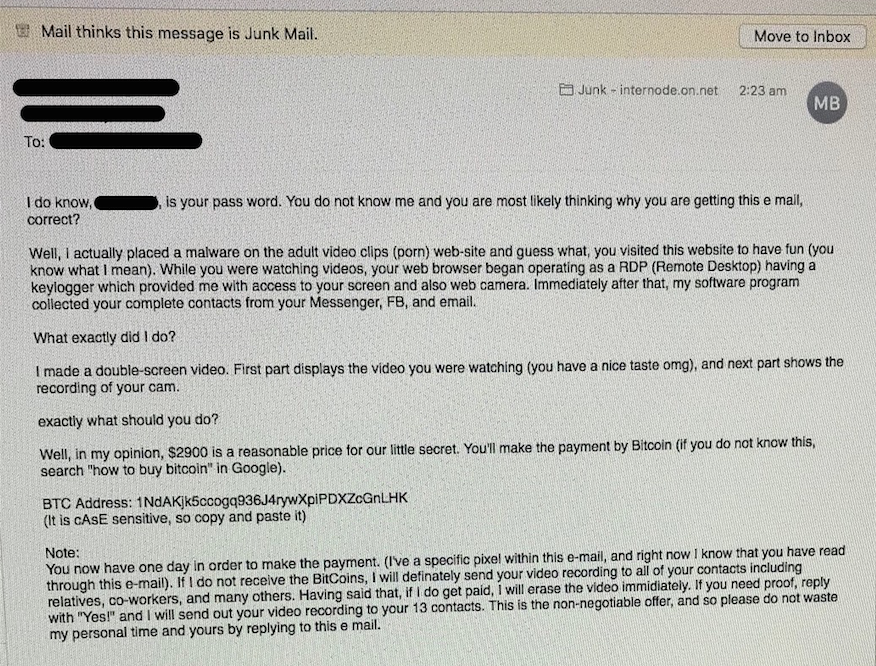
There are variations on this basic theme. In 2018, we covered a similar email that’s had something of a resurgence in recent weeks. This one features a lone hacker making demands, but instead they claim to have somehow acquired video surveillance of you from your webcam. Unlike the CIA porn scam, this earlier variant may appear to be sent from your own email address, to showcase the hacker’s amazing hacking prowess. (In fact, such email address ‘spoofing’ is comically easy, and it proves nothing.)
There is a common theme to these messages: to override your internal reasoning and replace it with fear. The threats talk of the recipient being arrested for a horrendous crime, or compromising videos being circulated among their contacts. Even if the accusations are false, this fear might be enough to spook people into paying the blackmailer.
The question that will doubtless play on your mind is whether you should be concerned. The answer is no.
What to do on receiving a porn blackmail email
Explore the ‘CIA’ text above and you’ll spot red flags that showcase it to be as much spam as scam. The content is quite well written, but doesn’t add up, and has giveaway spellings that are not in U.S. English. Moreover, the email address our example was sent from was [email protected]. (In Mail on macOS, you can check a sender’s email address by clicking the down arrow next to their name.) We find it rather unlikely—to say the least—that the CIA has suddenly switched to using the top-level domain (.cf) of the Central African Republic!
So here’s our advice on what to do if you receive a similar email:
- Don’t worry. Seriously.
- (Optional) Forward the email to [email protected] if it impersonates a U.S. agency (see our instructional video for details on how to include the full headers to help in the investigation)
- (If applicable) If you paid the ransom and you’re a U.S. resident, file a report at ic3.gov
- Delete the email. If you don’t pay, nothing will happen, because this CIA case file on you does not exist—just like the fake surveillance threats from the other scams.
Protect yourself against genuine email scams
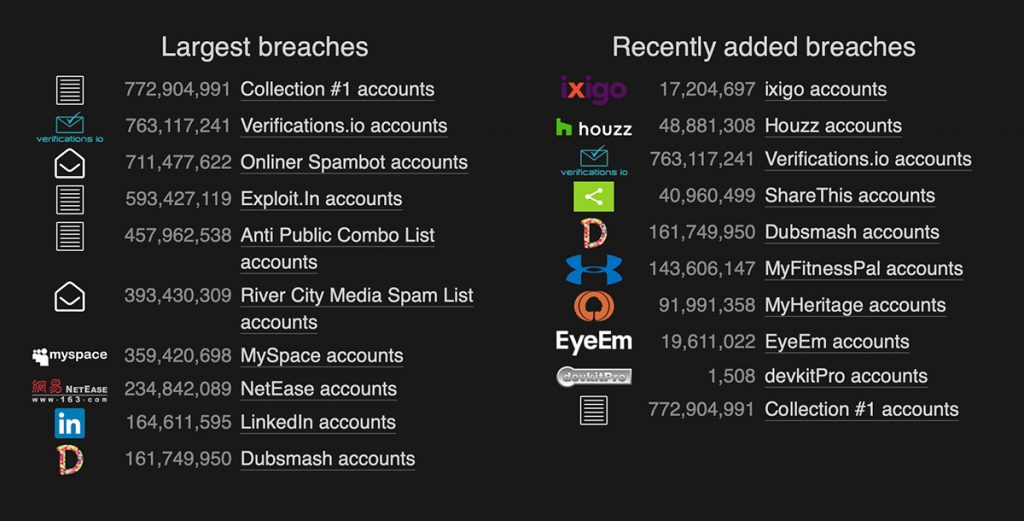
There are, however, much more dangerous scammers out there who can make your digital life miserable by using social engineering and other techniques to gain control of your online accounts. So although you shouldn’t be worried about porn scams such as those outlined in this article, do not become complacent. Chances are your email has ended up on a scammer’s list through a password breach; check haveibeenpwned.com to see if yours has been compromised.
If you’ve had any accounts become compromised, be sure to read How to Avoid Getting Hacked After Data Breaches. Also, we can’t stress enough that you should use a password manager to manage your passwords. Every service and account you have online should have its own unique, complex password (and wherever possible, two-factor authentication).
You may also wish to keep your Mac protected from malware and ransomware using Intego VirusBarrier X9 (or at least scan manually with the free VirusBarrier Scanner, available on the Mac App Store; read Why Your Antivirus Needs Real-Time Scanning to learn about the differences).
In short, then: don’t worry about porn blackmail scams from the CIA or elsewhere, because, well, they’re scams. But do remain vigilant, ensuring your Mac and your online accounts are well defended, rather than a row of open doors.
How can I learn more?
 Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, including security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, including security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
You can also subscribe to our e-mail newsletter and keep an eye here on The Mac Security Blog for the latest Apple security and privacy news. And don’t forget to follow Intego on your favorite social media channels: ![]()
![]()
![]()
![]()
![]()
![]()
![]()

