How to Use Your Web Browser’s Fraudulent Site Protection Feature
Posted on
by
Kirk McElhearn
Malware comes in many types, and it threatens you in many ways. In the early days of computers, the main worry was that you’d get infected by viruses that hid on floppy disks. That medium is no longer a threat, and most malware now is downloaded from the internet or attached to email messages. You can usually tell from the email you get whether an attachment is suspicious; lately, a lot of phishing email contain subjects such as “Invoice” or “Photo,” in the hopes that you might absent-mindedly double-click on a file. But some well-crafted emails may fool you.
Even if you are careful to not open files you receive with emails, and don’t download files from unreliable websites, there are still risks. Drive-by downloads can infect you unwittingly when you visit a website; the code on a page causes a file to be downloaded, and, in some cases, depending on your settings, that file may be launched automatically.
Other malicious websites may attempt to take advantage of vulnerabilities in software such as your web browser, or in the plug-ins it uses. One of the most attacked pieces of software is Adobe’s Flash Player. This plug-in is regularly updated as vulnerabilities seem to spring up like mushrooms after a thunderstorm. (See these articles on the Intego Mac Security Blog to see how often Adobe updates Flash.)
Because of this, web browsers have adopted “fraudulent site protection,” which relies on a constantly-updated database of URLs that lead to malware. Google’s Safe Browsing service is the most widely used such database; Safari, Firefox, and Chrome all use this on the desktop, and Safari uses it on iOS devices. Google says, about the Safe Browsing service, that it can:
- Warn users before they click on links in your site that may lead to malware-infected pages.
- Check a list of pages against Google’s lists of suspected phishing, malware, and unwanted software pages.
According to Google, some one-billion people use Google Safe Browsing, and tens of millions of people receive alerts every week about unsafe websites. They detect thousands of new malicious websites every day, and add them to the database. When you load a web page in your browser, the browser checks the URL against the database. If a fraudulent site is detected, the browser alerts you.
Google detects two types of sites: those that serve malware, and those that serve as phishing hooks. These latter sites may resemble, say, an Apple or Amazon website, or even a bank’s website, in an attempt to trick you into entering your user name and password. If you do so, this data will be harvested and potentially used to empty your account, access your personal data, and more.
There are two ways that sites can be fraudulent. The first is websites that are set up intentionally to serve malware, or to trick people into entering personal information. The second is compromised websites. These are legitimate sites where hackers have installed a few pages, deep in the directory structure, where the people who manage the sites may never notice them. For the latter, Google attempts to contact webmasters to warn them that their sites have been compromised; because, in most cases, someone who runs a small blog may never know they’ve been hacked.
Activating Fraudulent Site Protection
As I said above, the three major web browsers — Safari, Firefox, and Chrome — all offer fraudulent site protection. Let’s look at how you turn this on for desktop versions of these browsers.
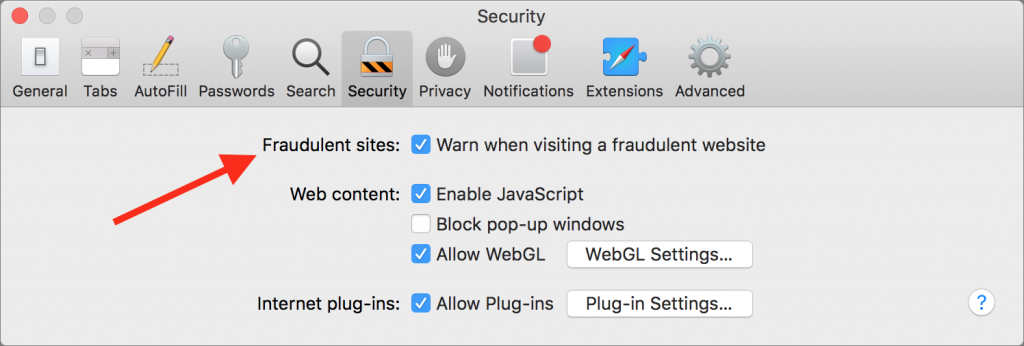
Safari
To activate fraudulent site protection in Safari: Choose Safari > Preferences, and then click Security. Check the box, “Fraudulent Sites: Warn when visiting a fraudulent website.”
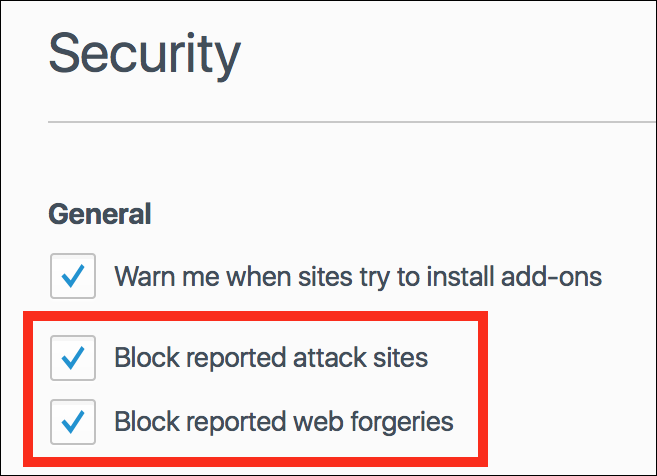
Firefox
To activate fraudulent site protection in Firefox: Choose Firefox > Preferences, and then click Security. Check the boxes for “Block reported attack sites” and “Block reported web forgeries.” (It’s a shame that Firefox uses such odd language; the terms “fraudulent websites” and “phishing” are common enough that they should be standard.)
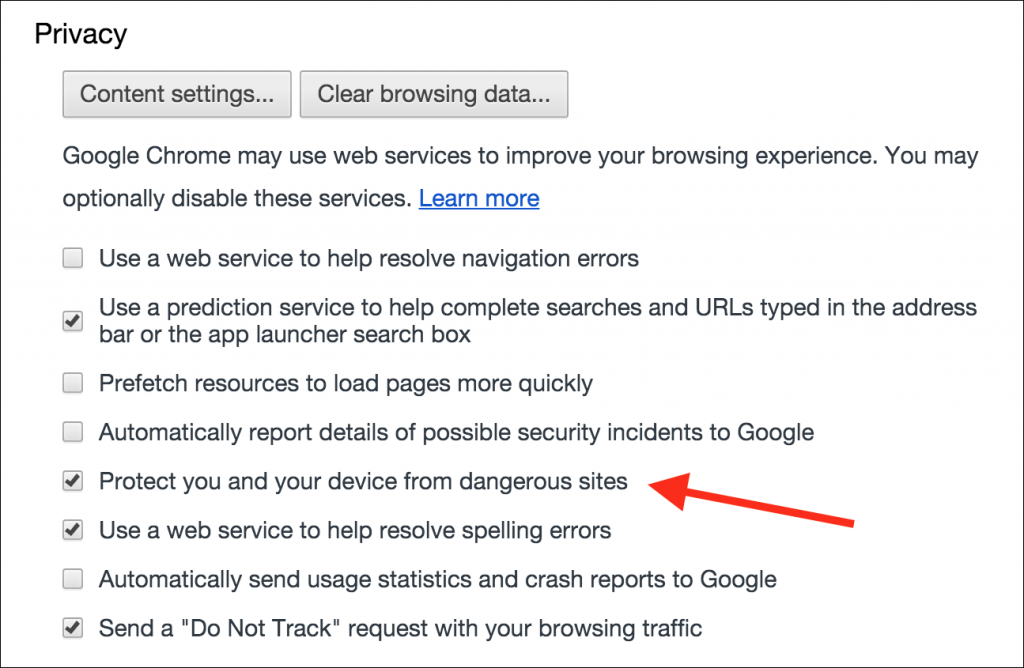
Google Chrome
To activate fraudulent site protection in Google Chrome: Choose Chrome > Preferences, and then click Show Advanced Settings at the bottom of the page. In the Privacy section, check the box, “Protect you and your device from dangerous sites.”
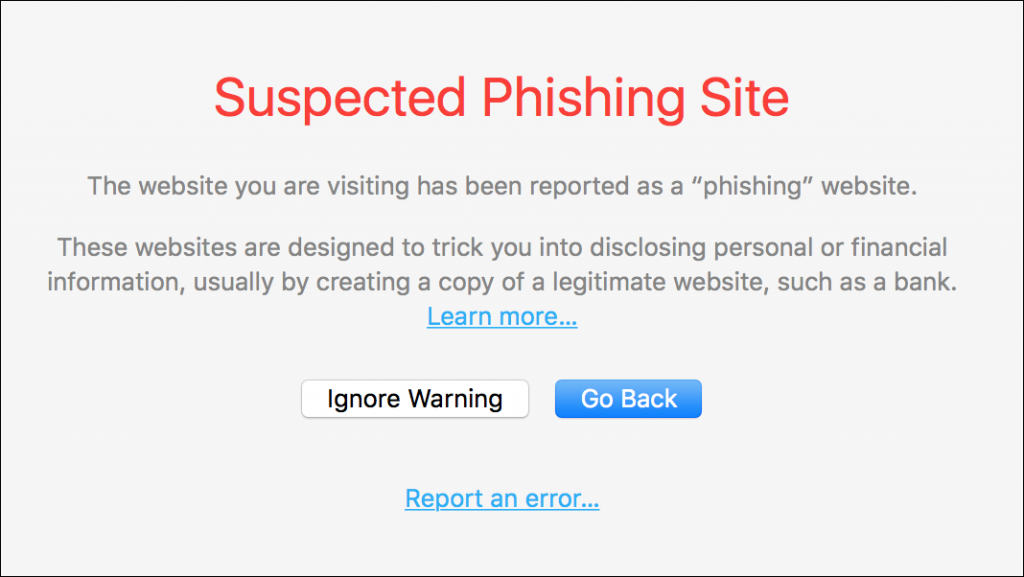
If you do encounter a dangerous website, you’ll see an alert, and you’ll be able to act accordingly. While there are rare cases of false positives — websites flagged as fraudulent which are, indeed, safe — you should assume that when you see such an alert it’s best not to venture any further. Just close the window or tab and move on.
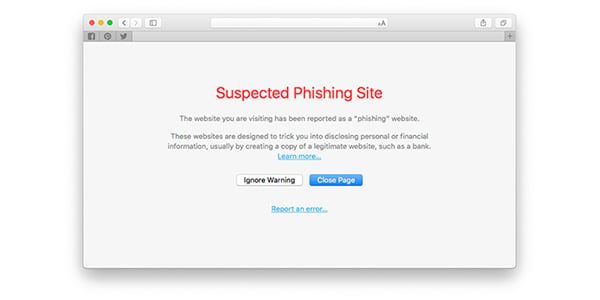
Here’s Safari’s alert for a suspected phishing site:
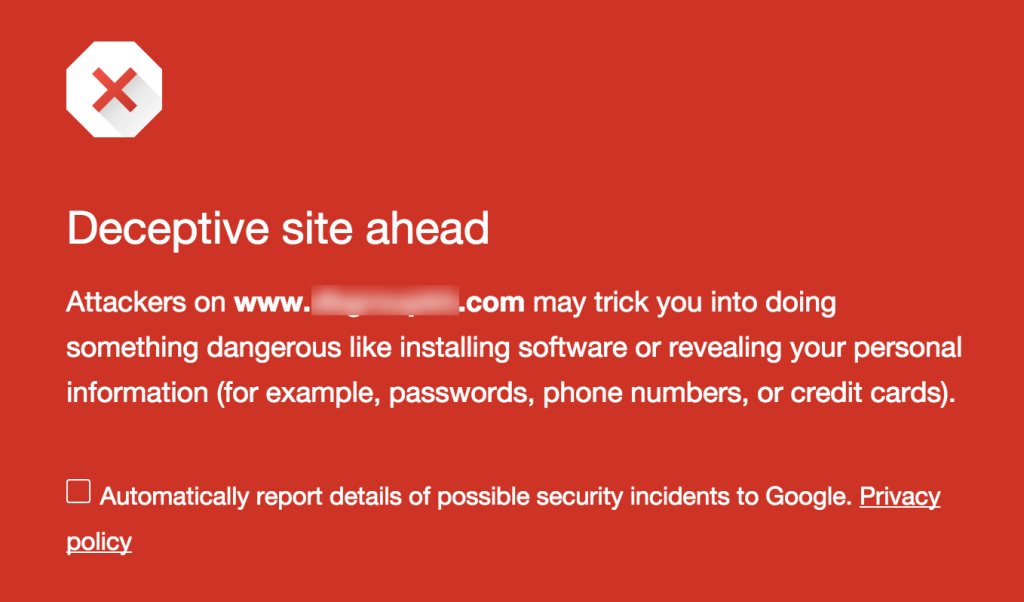
And here’s an alert in Google Chrome; it’s hard to miss:
Fraudulent Site Protection on iOS
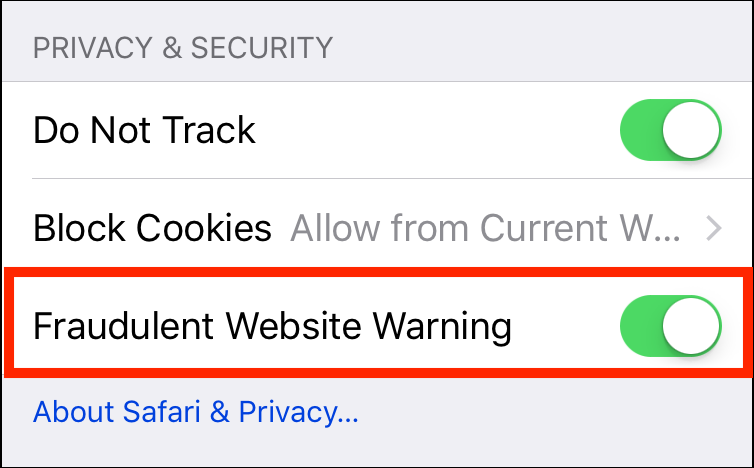
Safari on iOS can also use Google’s Safe Browsing service. You can activate it in Settings > Safari. Scroll down to the Privacy & Security section, and toggle Fraudulent Website Warning.
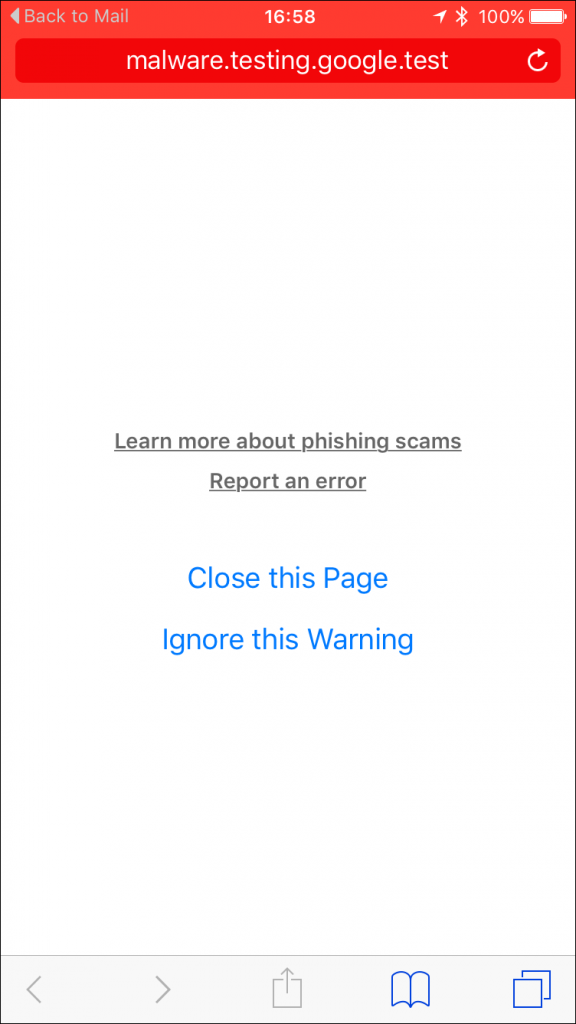
If you encounter a fraudulent page in Safari on iOS, you see a warning as seen in the image below; the red bar at the top of the screen is a good way to alert you that something is wrong.
Fraudulent site protection is a valuable feature, but it’s not foolproof. It depends on dangerous sites being reported to Google, and, while this happens quickly, new sites may spring up and threaten you before Google’s database is updated. So you should still always be careful where you surf. But using this feature can help warn you about many of the dangers you face when using the web.
Further Reading:
- Phishing Dangers in Business and How to Avoid Getting Hooked
- Seven iOS Web Browsers Compared
- The 6 Most Common Social Hacking Exploit Techniques