Security & Privacy + Security News
Apple Patches Brute Force Password-Cracking Security Hole in iCloud
Posted on
by
Graham Cluley
On New Year’s Day, when most of us were recovering from festivities of the night before, Apple was dealing with a whole different headache.
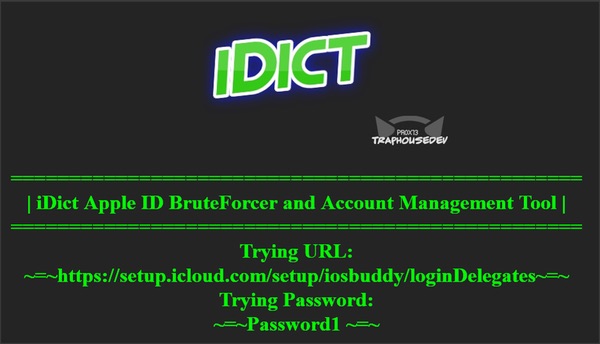
A hacker group calling themselves Pr0x13 released a tool designed to exploit a hole in Apple security, and gain access to iCloud accounts through sheer brute force.
iDict was described as a “100% working iCloud Apple ID Dictionary attack that bypasses account lockout restrictions and secondary authentication on any account.”
Posing as a legitimate iPhone device, the iDict software would make multiple attempts to break into iCloud accounts, working through a long list of commonly used passwords. That’s the kind of attack that you would hope Apple would normally prevent—noticing that the wrong password has been entered five times, and then blocking further attempts.
But iDict apparently leapt around that security hurdle—and it also, according to its author, could even bypass security questions (“What was the first car you owned?”) and two-factor authentication.
Releasing his or her code on GitHub, Pr0x13 claimed that the security hole exploited by iDict was “painfully obvious” and that it was “only a matter of time before it was privately used for malicious or nefarious purposes.” The hacker went on to explain that the iDict code was being publicly disclosed “so Apple will patch it.”
What a way to start 2015… as if 2014 hadn’t raised enough concerns about cloud security with numerous leaks of nude celebrity photos.
Fortunately, it appears that Apple responded quickly to the iDict threat and by 2 January, the security hole had apparently been fixed, as Pr0x13 acknowledged in a tweet.
iDict is patched, Discontinue it's use if you don't want to lock your account #TheMoreYouKnow
— ! ★ (@pr0x13) January 2, 2015
I’m far from convinced that Pr0x13 did the right thing by releasing the iDict tool and its code.
I fully understand that a hole like this in the security of iCloud accounts is very serious, and needs to be patched quickly. But I would have preferred if the code hadn’t been made available to the many who would, no doubt, be tempted to use it maliciously and illegally.
In these situations it’s always a good idea to inform the vendor who has the security hole and, if you feel they need a kick up the backside to fix it promptly, inform and demonstrate the vulnerability to the media.
After all, it could have been reported and made a pressing issue for Apple to fix without the code being released.
Of course, the best thing of all would be if these security holes weren’t present in the first place, or at the very least had been discovered by Apple’s own development and security team. As it is, all of us who use the iCloud were potentially at risk of having our accounts compromised.