Tibet.C Malware Delivered by Poisoned Word Documents Installs Backdoors on Macs
Posted on
by
Peter James
Intego has been examining several samples of new Mac malware, Tibet.C, which uses Word documents to install a backdoor on Macs. The infected Word files look like real files when users double-click them – they display text just like regular Word files – but actually contain three parts, that are concatenated within the file, and hidden from users.
The Word file, when double-clicked, opens and displays its contents:
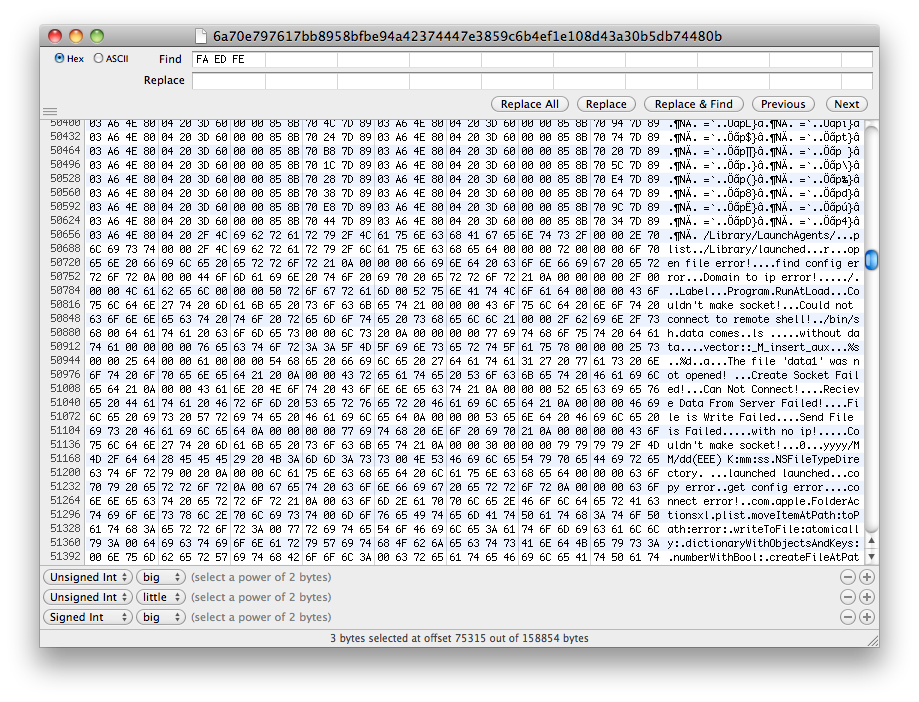
But within the document is code that executes when the file is opened:
This is the first time that Intego’s Malware Research Team has seen this technique used to target Macs. Simply launching a document leads to a buffer overflow, which then allows for the malicious code to execute. When this occurs, a backdoor is installed on the Mac, which then contacts a command and control server. Once this backdoor is active, those running the server can have full access to the infected Macs, as well as install other malware on them. They can either harvest documents from the infected Macs, install keyloggers to look for user names, passwords and credit card numbers, or use them as botnets to send spam or attack other computers.
These Word documents exploit a Word vulnerability that was corrected in June, 2009, but also take advantage of the fact that many users don’t update such software. Word 2004 and 2008 are vulnerable, but the latest version, Word 2011 is not. Also, this vulnerability only works with .doc files, and not the newer .docx format.
These files are not very large – the samples that Intego has analyzed range from 90 K to 230 K – and there is no indication that they may be dangerous. There is no request for a password, and the user does not need to be an administrator for this malware to install. It is worth noting that this is not only an attack on Mac users; Intego has found several samples of the same documents that contain code that will run on Windows.
This malware is fairly sophisticated, and it is worth pointing out that the code in these Word documents is not encrypted, so any malware writer who gets copies of them may be able to alter the code and distribute their own versions of these documents. While there is a possibility that this is a targeted attack on Tibetan NGOs, because the Word files contain text discussing the Tibetan situation, it seems more likely that this is a general attack on Mac users. The attack will be very effective on those who have not updated their copies of Microsoft Office, or aren’t running antivirus software, such as Intego VirusBarrier X6, and the Tibetan text may simply be a smokescreen.
This malware highlights the fact that Mac users should apply security updates to software they use regularly as soon as possible. Microsoft’s security alert clearly spelled out what this vulnerability could lead too:
This security update resolves two privately reported vulnerabilities that could allow remote code execution if a user opens a specially crafted Word file. An attacker who successfully exploited either vulnerability could take complete control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
While, in the past, we did not see this type of attack targeting Macs, it is clear that the game has changed, and that we are entering a new period of Mac malware. The Mac Security Blog has always published articles about security updates for common applications – web browsers, Microsoft Office, Adobe Acrobat and Flash, and many others – for this very reason. If these key programs are not up to date, they may be targeted by attacks, because of their ubiquity.
One way of spreading malware like this is by attaching files to spam messages, assuming that a number of people who receive them will open the files out of curiosity. It is therefore essential that, if you receive unsolicited Word documents, you do not open them.
Intego VirusBarrier X6, with malware definitions dated March 29, 2012, or later, will detect and eradicate the Tibet.C malware, and will also block the W97/CodeExec.gen code that exploits this specific vulnerability.