Lavabit and Silent Circle Stop Email Encryption Services
As of yesterday, it got a little less convenient to encrypt email end-to-end, as both Lavabit and Silent Circle...
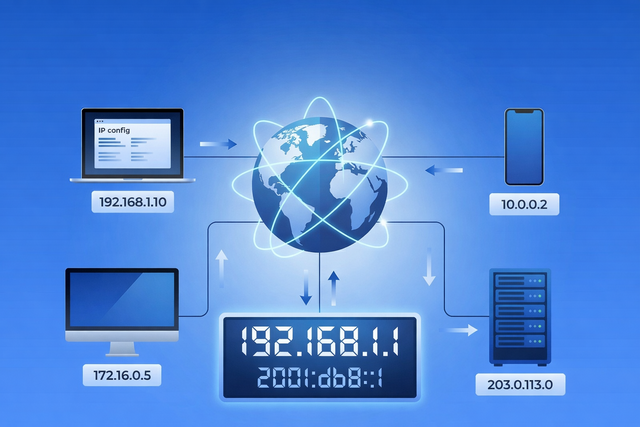
Every time you open a website, stream a video, send an email, or connect to Wi-Fi, your device relies on an IP address. You rarely see it, and most of the time you probably do not think about it. But it plays a quiet, important role in how the internet works. Your IP address helps...

Apple has just released critically urgent security updates—including macOS Sequoia 15.4.1 and iOS 18.4.1—to address two zero-day vulnerabilities that have been actively exploited in...

Mac gaming is in a better place than it used to be — but it’s not “anything a PC can do, a Mac can...
Is your Mac running slow? Here's how to diagnose and fix performance issues and get your Mac to run faster.
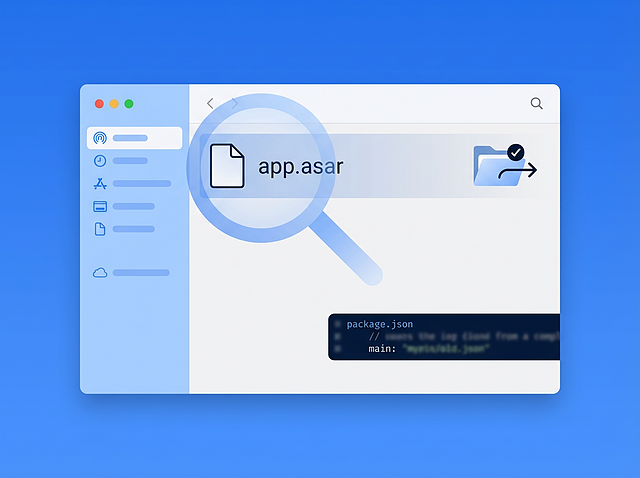
Executive Summary In March 2026, Intego Antivirus Labs investigated a macOS malware campaign delivering the OSX/Amos stealer. During analysis, the infection chain led from stripped Mach-O binaries and heavily obfuscated shell scripts to an unusual final payload that appeared...

As of yesterday, it got a little less convenient to encrypt email end-to-end, as both Lavabit and Silent Circle...
Spammers have a tendency to attempt to exploit any medium in order to drive traffic to their sites. Everyone...
So apparently this is the week I get to harp on the necessity of reading news with a soupçon...
Some of the most noteworthy malware were likely considered a failure by their authors. Flashback, for instance, turned out...
In one of my previous incarnations within the security industry, I was on the receiving end of a lot...
Every year the Black Hat security conference promises spectacular headlines of the ways hackers can use to make our...
File this under “Life is stranger than fiction”: You know you’re getting under the skin of cyber criminals when...
Last week, we discussed a couple of breaches that hit Apple’s developer site and Viber’s support site. As it...
The NSA saga continues! In this chapter, we find that the Feds are requesting SSL master-keys from Internet companies, in order to...