Microsoft Releases Office 2011 14.4.9 Update, Patches Critical Vulnerabilities
Posted on
by
Derek Erwin
Microsoft has released Office 2011 14.4.9 Update for Mac OS X version 10.5.8 or later, patching critical vulnerabilities in its software. These security updates resolve a total of 5 vulnerabilities in Microsoft Office that could allow remote code execution.
The Office for Mac security update applies to the following Microsoft software: Office for Mac 2011, Microsoft Word for Mac 2011, Outlook for Mac for Office 365, Word Automation Services on Microsoft SharePoint Server 2013, and Microsoft Office Web Apps Server 2013.
Microsoft’s security bulletin noted the following on the now closed vulnerabilities:
The most severe of the vulnerabilities could allow remote code execution if a user opens a specially crafted Microsoft Office file. An attacker who successfully exploited the vulnerabilities could run arbitrary code in the context of the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
The following security bugs are resolved with the Office 2011 14.4.9 update:
- CVE-2015-1639 : An elevation of privilege vulnerability exists in the Microsoft Outlook for Mac app that is caused when the software improperly sanitizes HTML strings. An attacker who successfully exploited this vulnerability could read content that the attacker is not authorized to read or use the victim’s identity to take actions on the targeted site or application. The security update addresses the vulnerability by correcting how Microsoft Outlook for Mac sanitizes HTML strings.
- CVE-2015-1641 : A remote code execution vulnerability exists in Microsoft Office software when the Office software fails to properly handle rich text format files in memory. An attacker who successfully exploited the vulnerability could use a specially crafted file to perform actions in the security context of the current user. The file could then, for example, take actions on behalf of the logged-on user with the same permissions as the current user. The security update addresses the vulnerability by correcting how Office handles files in memory.
- CVE-2015-1649 : Use-after-free vulnerability in Microsoft Word 2007 SP3, Office 2010 SP2, Word 2010 SP2, Word Viewer, Office Compatibility Pack SP3, Word Automation Services on SharePoint Server 2010 SP2, and Office Web Apps Server 2010 SP2 allows remote attackers to execute arbitrary code via a crafted Office document, aka “Microsoft Office Component Use After Free Vulnerability.”
- CVE-2015-1650 : Use-after-free vulnerability in Microsoft Word 2007 SP3, Office 2010 SP2, Word 2010 SP2, Word 2013 SP1, Word 2013 RT SP1, Word Viewer, Office Compatibility Pack SP3, Word Automation Services on SharePoint Server 2010 SP2 and 2013 SP1, and Office Web Apps Server 2010 SP2 and 2013 SP1 allows remote attackers to execute arbitrary code via a crafted Office document, aka “Microsoft Office Component Use After Free Vulnerability.”
- CVE-2015-1651 : Use-after-free vulnerability in Microsoft Word 2007 SP3, Word Viewer, and Office Compatibility Pack SP3 allows remote attackers to execute arbitrary code via a crafted Office document, aka “Microsoft Office Component Use After Free Vulnerability.”
Microsoft’s security team addressed the critical flaws by correcting how Microsoft Office parses specially crafted files, by correcting how Office handles files in memory, and by helping to ensure that SharePoint Server properly sanitizes user input.
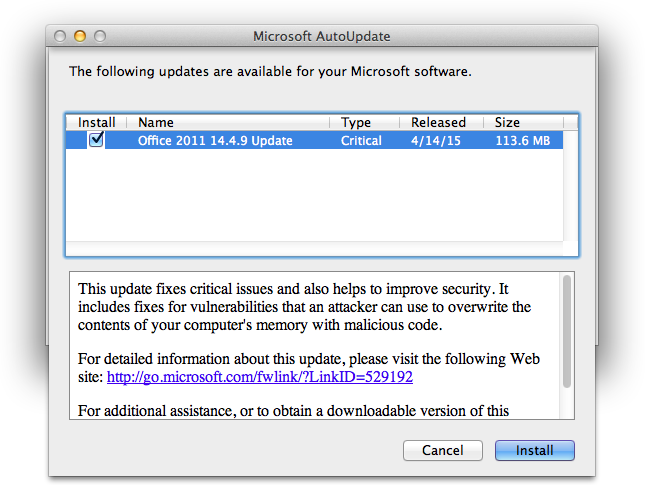
We strongly encourage all users running Microsoft Office 2011 for Mac install these updates as soon as possible. Mac users can update your software by using Microsoft’s AutoUpdate application, or you can visit Microsoft Download Center to get the Office 2011 14.4.9 Update (113.6 MB).

