Microsoft Issues Office 2011 14.6.2 Security Update
Posted on
by
Derek Erwin
This week, Microsoft released Office 2011 14.6.2 with critical patches for security flaws in Microsoft Office for Mac. This update addresses a remote code execution vulnerability in which remote attackers could execute arbitrary code via a crafted Office document, also known as “Microsoft Office Memory Corruption Vulnerability” (CVE-2016-0134).
An update for Microsoft Office 2016 for Mac was not released on March 16. “This update will be released as soon as it is available and users will be notified via a bulletin revision,” said Microsoft. However, the tech giant did provide updates to versions of Word, Excel, PowerPoint, OneNote, and Outlook that are designed for Microsoft Office 2016 for Mac. These updates resolve vulnerabilities that could allow remote code execution if a user opens a specially crafted Office file.
For a complete list of affected versions of Microsoft software, visit this MS support page.
The most critical vulnerability patched in these updates is described as follows:
CVE-2016-0134 : Microsoft Word 2007 SP3, Office 2010 SP2, Word 2010 SP2, Word 2013 SP1, Word 2013 RT SP1, Word 2016, Word for Mac 2011, Word 2016 for Mac, Office Compatibility Pack SP3, Word Viewer, Word Automation Services on SharePoint Server 2010 SP2 and 2013 SP1, Office Web Apps 2010 SP2, and Web Apps Server 2013 SP1 allow remote attackers to execute arbitrary code via a crafted Office document, aka “Microsoft Office Memory Corruption Vulnerability.”
While not currently being exploited, according Microsoft, the company outlined how an attack could impact users, saying:
If the current user is logged on with administrative user rights, an attacker could take control of the affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
Successful exploitation of the vulnerabilities requires that a user open a specially crafted file with an affected version of Microsoft Office software. That said, Microsoft clarified what is and is not an attack vector:
[The] Preview Pane is not an attack vector for these vulnerabilities. In an email attack scenario an attacker could exploit the vulnerabilities by sending the specially crafted file to the user and convincing the user to open the file. In a web-based attack scenario an attacker could host a website (or leverage a compromised website that accepts or hosts user-provided content) that contains a specially crafted file that is designed to exploit the vulnerabilities. An attacker would have no way to force users to visit the website. Instead, an attacker would have to convince users to click a link, typically by way of an enticement in an email or Instant Messenger message, and then convince them to open the specially crafted file.
Microsoft’s Office for Mac updates address the vulnerabilities by correcting how Office handles objects in memory.
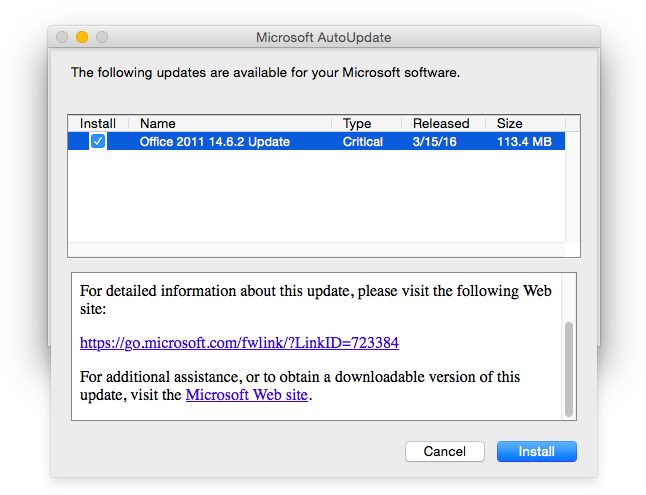
Office for Mac 2011 users should install the update immediately. Mac users can update your software by using Microsoft’s AutoUpdate application, or by visiting the Microsoft Download Center to get and install Office 2011 14.6.2 (113.4 MB).
Office 2016 for Mac users can get the updates by using Microsoft AutoUpdate. To do this, open a Microsoft Office program, and then click Check for Updates on the Help menu. Otherwise, the updates are also available for download and installation from the Microsoft Download Center:

