Apple Updates XProtect to Detect Microsoft Silverlight Exploit
Posted on
by
Derek Erwin
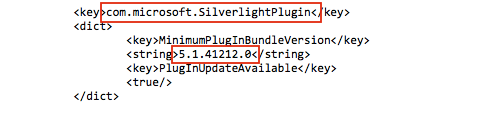
Following the discovery of a Microsoft Silverlight exploit, Apple has updated its XProtect.plist malware definitions file to version 2073. This update detects the minimum bundle version for Silverlight, protecting Mac users from Microsoft Silverlight 5 before version 5.1.41212.0.
The vulnerability that is being exploited is described as follows:
CVE-2016-0034 : Microsoft Silverlight 5 before 5.1.41212.0 mishandles negative offsets during decoding, which allows remote attackers to execute arbitrary code or cause a denial of service (object-header corruption) via a crafted web site, aka “Silverlight Runtime Remote Code Execution Vulnerability.”
The remote code execution vulnerability exists when Microsoft Silverlight 5 (before 5.1.41212.0) “decodes strings using a malicious decoder that can return negative offsets that cause Silverlight to replace unsafe object headers with contents provided by an attacker,” according to the Microsoft security team. And to exploit the vulnerability, “an attacker could host a website that contains a specially crafted Silverlight application, and then convince a user to visit the compromised website,” often by enticing them to click a link in an email or instant message.
Exploit kits are typically based on a “drive-by download attack” delivery technique, and installation can start silently in the background simply by visiting a website.
Microsoft confirmed the zero-day (CVE-2016-0034) and issued a patch on January 12, 2016. The update to Microsoft Silverlight 5.1.41212.0 addresses this vulnerability by correcting how Microsoft Silverlight validates decoder results.
Intego VirusBarrier with up-to-date malware definitions protects Mac users against the Microsoft Silverlight exploit, detected as W32/CVE-2016-0034. Most importantly, Intego VirusBarrier will detect known malware downloaded with any application, while Apple’s XProtect system only functions with files downloaded by certain programs—primarily Apple software, such as its Safari web browser, Mail and iChat applications.

