Malware + Recommended + Security News
Shellshock Vulnerability: What Mac OS X Users Need to Know
Posted on
by
Derek Erwin
 The vulnerability is called Shellshock, and it has rocked the security industry to its core. A flaw in the “Bash” shell—the command line interpreter for Unix-based systems including Linux and Mac OS X—has sent server administrators scrambling to patch their systems.
The vulnerability is called Shellshock, and it has rocked the security industry to its core. A flaw in the “Bash” shell—the command line interpreter for Unix-based systems including Linux and Mac OS X—has sent server administrators scrambling to patch their systems.
Security experts are saying this vulnerability is as dangerous, if not more so, than the Heartbleed flaw found in OpenSSL software—an encryption service used by around two-thirds of websites to protect information sent to and from web pages—back in April. The Shellshock flaw affects the Bash shell used across many Unix-based systems including Mac OS X and variants of Linux.
The Shellshock vulnerability (CVE-2014-6271, CVE-2014-7169) has been compared to Heartbleed, partly because the software at the heart of the “Shellshock” bug, known as Bash, is also widely used in web servers and other types of computer equipment.
With Heartbleed, somebody could grab credentials of a user and do what they wanted with it; however, the bug only allowed an attacker to steal data. But with Shellshock, if someone is vulnerable, an attacker could insert malicious pieces of code from a remote location and get full system control of a victim’s machine.
Fortunately, the Shellshock vulnerability is unlikely to affect as many systems as Heartbleed, because not all computers running Bash can be exploited.
How to tell if your Mac is vulnerable
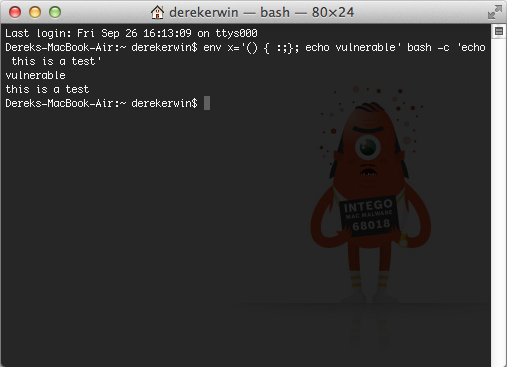
If you have a Mac OS X or Linux system, open the Terminal and run this line of code:
env x='() { :;}; echo vulnerable' bash -c 'echo this is a test'
If it returns the word “vulnerable” as an answer, then your machine is in theory vulnerable.
Here’s what that means, as mentioned over at Engadget:
Your Bash shell is simply running more code after a function (the “() { :;};”part), and that shouldn’t be happening. The function is the “allowed” code, while everything after it is where the potentially “malicious”code could be installed.
But—this is important—if your Mac is “vulnerable,” all this means is that your default shell is Bash. The only way for infections to occur is by exposing this vulnerability on a Mac.
If someone were to write an app that contained the exploit, a user downloaded the app, bypassed Gatekeeper (it would have to be an unsigned, unsandboxed app) and ran the app anyway, then yes—a Mac user could potentially get malware this way.
What exposes your Mac to Shellshock
There are two routes to exposing this vulnerability to a remote attack on a Mac:
Route 1
- Go into System Preferences > Sharing and turn on Remote Login
- In the same location, turn on All Users
- Go into System Preferences > Users & Groups and make sure Guest Access is enabled
Your system is now vulnerable. If you don’t enable guest access your system is still vulnerable if the attacker knows or is able to guess your username and password. But as this connection is secured, they can’t get that from packet sniffing. And enabling a guest shell on a box is probably not the most secure thing to do anyway.
Route 2
This route requires OS X Server, an old (Lion or earlier) version of OS X, or for the user to install Apache/PHP/some other scripting environment.
- Enable Apache and have it running
- Enable Apache to run scripts or execute extensions
- Have one of those scripts or extensions vulnerable to malicious attacking (being able to inject something into the script that gets executed)
The attacker can then insert the variables into the script or extension that gets run under the Bash shell, then the injection gets into the Shellshock vulnerability, and voila—machine compromised. This one, however, requires exploiting two holes. First, in the script running on Apache, and then in turn using that compromised script to send something to the Bash shell.
What this means
As you can see, these are both edge cases. And both routes probably require a level of technical expertise that the person configuring their account as such can patch the exploit fairly simply.
Also note that for route 1, enabling a Bash shell with Guest access for remote login most likely opens up your system to many other possible attacks. The difference Shellshock provides is access to root privileges, in other words full machine access to said Guest user.
The bigger issue is all the devices with embedded Unix, where telnet (unsecured) access is enabled, and no login is required. These typically are “The Internet of Things” (IoT) devices. Even if they require an administrator password other then “Admin” to get change settings, Shellshock may now give the attacker root to do whatever they want on the device.
What can an attacker do to your Mac?
Basically, an attacker can run code by simply asking for basic information from your computer, a server or an IoT device. “The remote execution (over the Internet or a network) of extra code could let an attacker load malware on a system and steal private information, delete files, activate your camera, open a lock and, well, do pretty much anything with a little know-how,” mentioned Jose Andrade at Engadget.
However, the Engadget article also mentions “your computer is most likely unaffected” if you are running a firewall that blocks external requests not initiated locally by the software already authorized to run. This suggests that if a Mac is running firewall software, such as Intego NetBarrier, it has not been proven possible to take advantage of the bug under that scenario.
Unfortunately, the Bash Shellshock bug is wormable, and can easily worm past firewalls and infect lots of systems, according to Robert Graham at Errata Security. Robert explained:
“One key question is whether Mac OS X and iPhone DHCP service is vulnerable –once the worm gets behind a firewall and runs a hostile DHCP server, that would be ‘game over’ for large networks.”
And, worse, protecting a server is another issue but different, because a server must listen to requests in order to do its job. Engadget’s Jose Andrade provided a good overview of this problem:
This means that by requesting almost any data and running malicious code, an attacker can infect any affected server, which is about 60 percent of web servers out on the internet, most routers (even your home router) and many consumer devices (including security cameras and “smart” appliances — which don’t seem so smart right about now). This is because smart appliances are a form of servers.
Have hackers figured out how to exploit the Shellshock vulnerability?
With the media spotlight on the Shellshock vulnerability, in just one day after discovery, hackers have most likely figured out how to exploit it. Intego has seen proof-of-concept exploits so far on Mac OS X, and we are continuing to research this threat and will continue to provide updates as new information becomes available.
How can the Shellshock vulnerability be resolved?
In a statement to iMore, an Apple representative disclosed the following:
The vast majority of OS X users are not at risk to recently reported Bash vulnerabilities. Bash, a UNIX command shell and language included in OS X, has a weakness that could allow unauthorized users to remotely gain control of vulnerable systems. With OS X, systems are safe by default and not exposed to remote exploits of bash unless users configure advanced UNIX services. We are working to quickly provide a software update for our advanced UNIX users.
According to Apple, there is a patch coming soon for Mac users who could be exposed.
What can you do to stay protected?
Until Apple patches this hole, which they no doubt will, you can take a few simple steps to make sure you’re not exposed:
- Don’t enable Guest Access AND at the same time enable All Users for Remote Login.
- Don’t run a Web server on your personal machine.
- Have a strong password on your Account.
- Keep Gatekeeper turned “On.”
- Only install or run signed Apps from trusted sources.
- For extra protection install a Firewall, such as Intego NetBarrier.
UPDATE: Apple’s OS X Bash Update 1.0 Patches Shellshock Vulnerability
Also remember, these are probably good security rules to adhere to even after Apple patches this hole, just to insure you don’t fall victim to the next one yet be discovered.
Where to get more information
US-CERT recommends Mac OS X users (and pretty much anyone concerned about the flaw) seek help from the Redhat Security Blog, or consult their respective Linux or Unix operating system vendor for advice.