iOS 9 Can Now Finally Be Remotely Jailbroken — but YOU Can’t Do It
Bad news iOS 9 users. Someone has developed a way of jailbreaking your iPhone or iPad and spying...
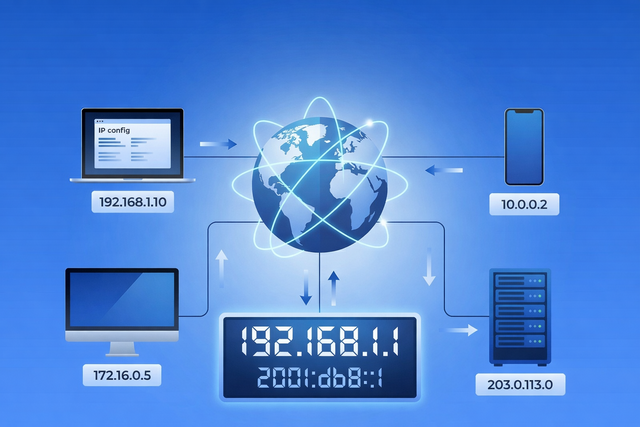
Every time you open a website, stream a video, send an email, or connect to Wi-Fi, your device relies on an IP address. You rarely see it, and most of the time you probably do not think about it. But it plays a quiet, important role in how the internet works. Your IP address helps...

Apple has just released critically urgent security updates—including macOS Sequoia 15.4.1 and iOS 18.4.1—to address two zero-day vulnerabilities that have been actively exploited in...

Mac gaming is in a better place than it used to be — but it’s not “anything a PC can do, a Mac can...
Is your Mac running slow? Here's how to diagnose and fix performance issues and get your Mac to run faster.
Malware + Security & Privacy + Security News
Executive Summary Intego Antivirus Labs is tracking an evolution of the “ClickFix” social engineering campaign targeting macOS users. Dubbed Matryoshka due to its nested obfuscation layers, this variant uses a fake installation/fix flow to trick victims into executing a...

Bad news iOS 9 users. Someone has developed a way of jailbreaking your iPhone or iPad and spying...
It’s important to create secure passwords that are hard to hack. Here are 5 tips to stay safe online...
Apple + How To + Recommended
Customize OS X El Capitan and make it easier to work with your Mac. Here’s how to tweak the...
Mobile devices can be used almost anywhere and everywhere. And with the Internet more accessible than ever, kids are now bombarded...
Want to use an ad blocker on your iPhone? Here we explain how to install, set up, and use...
Last Friday, Adobe Systems released an ahead-of-schedule update to resolve a widely known vulnerability in Flash Player being actively...
Microsoft has released Office for Mac 14.5.7 as an update that patches two remote code execution flaws affecting Microsoft...
Apple + Malware + Recommended
A group of Chinese hackers famous for their jailbreaking activities, announced that they had released to the public the...
Security & Privacy + Security News
If no words are spoken, how could hackers send Siri a command? French researchers have uncovered an ingenious - albeit...
It’s 2015, and in today’s interconnected world we live robust, online lives. From banking and shopping to health care, social...