Malware + Recommended + Security News
Malware Spreads through Modified Transmission Application (Again)
Posted on
by
Jay Vrijenhoek
Merely 5 months ago the BitTorrent client Transmission made headlines as being the delivery vehicle for the first Mac ransomware. Now the spotlight is back on Transmission, but this time it was found to be infected with OSX/Keydnap malware. OSX/Keydnap, designed to steal the content of your OS X keychain and keep a backdoor to your Mac open, is detected by Intego VirusBarrier.
Researchers described at WeLiveSecurity that it appears the Transmission application was modified by adding a block of malicious code to the main function—similar to how the ransomware KeRanger was added. The application was then recompiled and made available for download through the legitimate download page on the transmission website.
A closer look at the infected applications show it was digitally signed with a legitimate code signing key, which causes it to bypass Gatekeeper completely and thus opens without problems on your Mac.
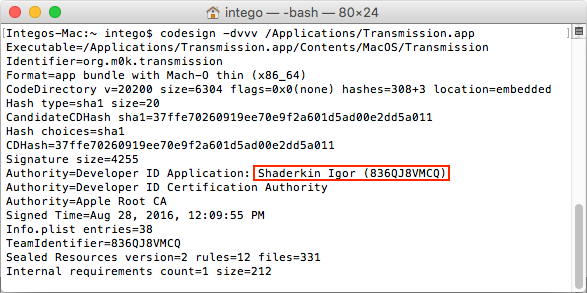
As can be seen in the screenshot, the application was signed on August 28, 2016 and believed to be distributed the following day. The researchers notified the transmission team and within minutes the malicious file was removed from their web server. This means anyone who has downloaded Transmission from their website on August 28 or 29 potentially grabbed the infected version.
If you have downloaded the application from their website in the last few days, we recommend checking for the following files:
- /Applications/Transmission.app/Contents/Resources/License.rtf
- /Volumes/Transmission/Transmission.app/Contents/Resources/License.rtf
- $HOME/Library/Application Support/com.apple.iCloud.sync.daemon/icloudsyncd
- $HOME/Library/Application Support/com.apple.iCloud.sync.daemon/process.id
- $HOME/Library/LaunchAgents/com.apple.iCloud.sync.daemon.plist
- /Library/Application Support/com.apple.iCloud.sync.daemon/
- $HOME/Library/LaunchAgents/com.geticloud.icloud.photo.plist
- $HOME/Library/Application Support/com.geticloud/icloudproc
- $HOME/intego/Library/Application Support/com.geticloud/
The “/Volumes/Transmission….License.rtf” file can be ignored as that indicates the application inside the downloaded .dmg file (which you should delete right away if it’s still in your Downloads folder) once it is mounted.
These files are an indication that your Mac has been infected with the Keydnap malware and should be removed. Intego VirusBarrier detects the malicious files as OSX/Keydnap.
For the observant Mac user, there were two indicators something may have been wrong with the download, though one is easily overlooked and the other rarely tested.
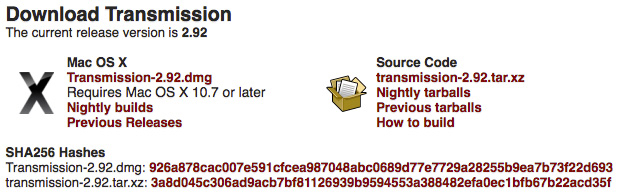
- The downloaded file had the name “Transmission2.92.dmg” while the download page mentions “Transmission-2.92.dmg” (including the hyphen) as being the correct file name.
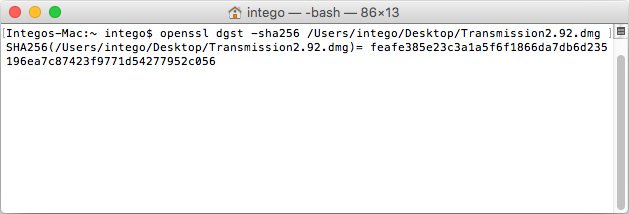
- The download page lists a SHA256 hash for the file, this is a means for the end user to confirm the downloaded file is in fact the file they should be getting. The SHA256 hash for the .dmg file as per the site is “926a878cac007e591cfcea987048abc0689d77e7729a28255b9ea7b73f22d693” but when the .dmg with the infected application is checked, the SHA256 comes out as “feafe385e23c3a1a5f6f1866da7db6d235196ea7c87423f9771d54277952c056”. The user doesn’t even have to compare all 64 characters, if only 1 is off, it means the file is not as intended.
Apart from these two indicators, there was nothing else to show something may be amiss to the end user. The application works as expected.
The devil is often in the details and while a simple hyphen is easily overlooked, the SHA digest (security checksum for a data file) should always be checked. Different sites use different SHA digests, so the ways to check them vary slightly. For example, Apple lists SHA-1 digests on their website with some downloads while Transmission lists SHA-256 instead.
Using the infected Transmission .dmg file as an example, to verify the checksum open the Terminal application and type the appropriate command:
- For SHA-1: openssl sha1 [full path to file]
- For SHA-256: openssl dgst -sha256 [full path to file]
- For MD5: md5 [full path to file]
Rather than typing the full path name, you can drag the file onto the terminal window after typing one of the above commands. Hit return when done and Terminal will show you the digest. MD5 is not used that often anymore but as you may still see it in the wild it’s good to know how to verify those checksums.
Editor’s Update, August 31:
At the original time of writing this article, the Transmission website was offline. This turns out to have been intentional. In a statement from the Transmission team:
It appears that on or about August 28, 2016, unauthorized access was gained to our website server. The official Mac version of Transmission 2.92 was replaced with an unauthorized version that contained the OSX/Keydnap malware. The infected file was available for download somewhere between a few hours and less than a day.
To help prevent future incidents, we have migrated the website and all binary files from our current servers to GitHub. Other services, which are currently unavailable, will be migrated to new servers in the coming days. As an added precaution, we will be hosting the binaries and the website (including checksums) in two separate repositories.
Intego will update this story as new information becomes available.