Key Moments in the History of Mac Malware – 1982 to the Present
Posted on
by
Kirk McElhearn
You’ve certainly heard people say that "Macs don’t get viruses." And, while that’s generally true – most malware these days isn’t viruses but other types of malicious software – the Mac has a long history of malware attacks. Viruses, worms, Trojan horses; the Mac has seen them all. Here is an overview of the history of malware that has affected the Mac.
1982 – Elk Cloner
Even before the arrival of the Macintosh, Apple computers were affected by viruses. In fact, the Elk Cloner virus is considered to be the first computer virus that spread in the wild. Infecting Apple’s DOS 3.3 operating system, it was hidden in a game, and the 50th time someone played the game, the computer would display a poem. It infected the entire operating system, and spread via floppy disks to other computers.
1987 – nVIR
The nVIR virus was first discovered in 1987, and it affected Macintosh computers running System 4.1 to 8.0. There were many strains of nVIR, and, while it was not malicious, it reproduced by infecting the System file and applications. It would either beep, or, if MacinTalk was installed, have the computer say "Don’t panic".
1988 – HyperCard viruses
HyperCard was a development environment, released in 1987, that allowed users to create applications in "stacks" and distribute them to other Mac users. Shortly after that, viruses began appearing that infected HyperCard, spreading via stacks that users shared, notably on bulletin boards. One early HyperCard virus displayed a message supporting the US presidential campaign of Michael Dukakis.
Another, called MacMag, was an example of good intentions gone wrong. It was written for the MacMag magazine, and was designed to display a message of peace when an infected computer was started up on March 2, 1988, and then delete itself. Unfortunately, because of a bug in the virus’s code, it caused computers to crash when they were started up before this date. It was also present on copies of the FreeHand app, sold by Aldus, which led to the company having to recall thousands of copies of their software.
Interlude – Disinfectant
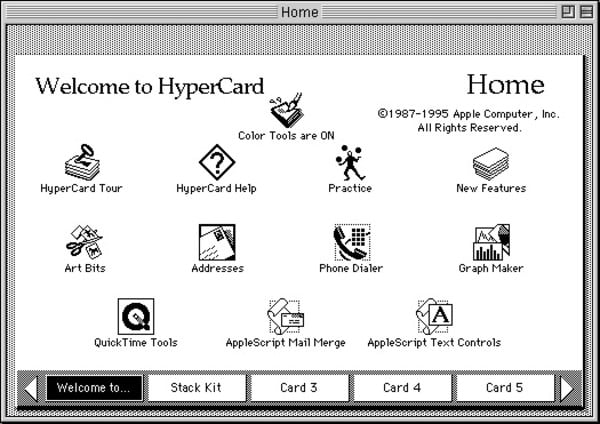
With the rise in viruses affecting the Mac, John Norstad, of Northwestern University, created the free antivirus Disinfectant in in 1989. The software was available online, on a number of bulletin boards and freeware repositories, or you could send Norstad a floppy disk and a self-addressed stamped envelope to get a copy.
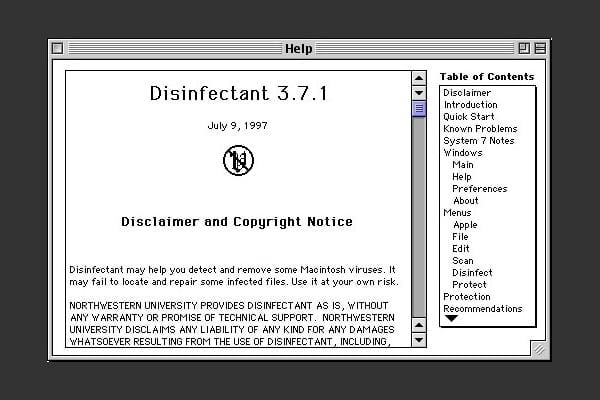
With no commercial antivirus software available yet, Disinfectant was a must-have for people who downloaded software from bulletin boards or who installed freeware and shareware from floppy discs provided with magazines. Norstad retired Disinfectant in 1998, because the software was unable to act on the growing threat of Microsoft Word and Excel macro viruses. At the same time, there were powerful commercial solutions available, and he could no longer maintain it sufficiently to ensure that it was reliable.
1990 – MDEF and CDEF
Four strains of the MDEF virus were discovered in 1990 and 1991 in Ithaca, New York, and two strains of the CDEF virus were discovered in 1990, then in 1993. The author of these viruses was arrested shortly after the viruses were discovered.
These viruses attacked applications and the System file, and could also infect documents and the Desktop file, which was an invisible file used on Mac OS prior to Mac OS X. Neither virus was particularly malicious, but they could, in some cases, damage applications, requiring that they be reinstalled.
1995 – Word macro viruses
Microsoft Office has a feature allowing users to write macros, or sets of commands to automate procedures. These macros can be stored in Word and Excel files, and they are read whenever files containing them are opened. So if you send a friend or colleague a file containing a macro, their apps will read the macro. It won’t necessarily execute when you open a file, but some can.
In 1995, we started seeing malicious macros that could not only damage your documents, or your Word and Excel applications, but they could also cross the Mac-Windows barrier: they were the first truly cross-platform malware.
The first real macro virus that was found in the wild was the Concept virus, which attacked Microsoft Word files. This was quickly followed by other variants, as virus writers saw the potential to do great damage through the ubiquity of this program. Later, macro viruses were written to exploit Microsoft Excel as well, though the Mac version of Excel only got macro support in 1998. In just a few years, thousands macro viruses circulated in the wild, and were a serious threat; while less common now, thanks to Microsoft having added settings to prevent macros from running automatically, new macro viruses are still discovered.
1998 – AutoStart worms

In May 1998, the first worm infecting Macintosh computers was found. AutoStart spread quickly throughout the world, and there were several variants of this worm.
This worm spread easily among Macintosh computers that had QuickTime’s "CD-ROM AutoPlay" function enabled. If an infected CD-ROM was read by the computer, the worm copied itself to the host computer, creating invisible files in various locations. These worms could cause serious damage, deleting files and destroying data.
2004 – Renepo/Opener

The 2004 discovery of the Trojan horse Renepo/Opener was a watershed moment for Mac malware. With Mac OS X, many changes had made the Mac more resistant to malware. But Apple had to add more serious security features to Mac OS X to meet this challenge. Mac OS X 10.4 Tiger, released in April 2005, saw a number of new security features added to protect Macs.
This Trojan horse made the news around the world, and even got written up in the New Scientist, showing how Macs had become much more important than in the previous decade.
2006 – Leap-A, or Oompa-Loompa
It was just a matter of time before a real Mac OS X virus was discovered. In 2005, Intego discovered Leap-A, or Oompa-Loompa, which spread via iChat over local networks via Bonjour. It required very specific conditions to spread, and its effect was limited, but it showed that Mac OS X wasn’t immune to sophisticated threats. Because its code had a number of bugs, it wasn’t very effective, but if it had been written more carefully, it could have been a lot more dangerous.
Interlude – 10 Years of Mac Malware, 2006 – 2016
Take a look at this infographic made by Intego in 2016, summing up the malware threats that affected the Mac in the ten-year period following the discovery of Leap-A, or Oompa-Loompa.
There was a wide range of threats in this period, with Trojan horses, worms, fake security software (such as MacDefender), and more. Check out the infographic for more details.
2011 – Flashback
In 2011, Intego discovered Flashback, which was by far the most widespread Mac malware of the decade. Masquerading as a Flash Player installer, it installed software on Macs that could turn them into "zombies" as part of a botnet, which affected as many as 700,000 Macs over time. Hackers could access files and install software on infected Macs, and there are still Macs infected with this malware.

2018 – Shlayer
Intego discovered Shlayer in early 2018. This Trojan horse masquerades as yet another Flash Player installer. Distributed on BitTorrent sites, this malware hasn’t spread a lot, but it has an interesting way of downloading additional software using shell scripts. You can learn more about Shlayer in Episode 28 of the Intego Mac Podcast.
Interlude – Flash Player
Flash Player was a target for Mac malware or many years. Not that the Flash Player app itself was targeted, but as users often saw alerts when visiting sites using Flash, saying that they needed to update their Flash Player, malware creators took advantage of this to create fake Flash Player installers.
Flash Player is being phased out, and will be considered obsolete at the end of 2020. Don’t install Flash Player, and use the Google Chrome browser if you need to access Flash content, since the browser has its own, built-it version of the software. Update Chrome regularly, and you won’t need to worry about Flash Player updates.
2019 – Linker and CrescentCore
Linker seems to have been a proof of concept or a test that attempted to exploit a vulnerability in macOS’s Gatekeeper technology, which checks software for specific types of malware that Apple flags, or which checks for the presence of a valid developer certificate. Intego found a number of samples, and speculates that the malware, while not in the wild, was a test to see if it would be detected.
Another Flash Player Trojan horse, CrescentCore, attempts to evade antivirus detection using some sophisticated code. CrescentCore is widely distributed on file sharing websites, but was also found on other websites that featured near the top of some Google search results.
Learn more about Linker and CrescentCore on Episode 88 and Episode 89 of the Intego Mac Podcast.
30+ Years of Apple Malware
This article only contains highlights of more than thirty years of malware affecting Apple computers; there have been plenty of other types of malware discovered, most of which had little distribution in the wild. Malware creators won’t stop targeting Macs any time soon, and Intego remains vigilant, discovering new malware, and ensuring that Intego VirusBarrier protects your Macs.

