iOS 9.3 Patches iMessages Encryption Vulnerability
Posted on
by
Derek Erwin

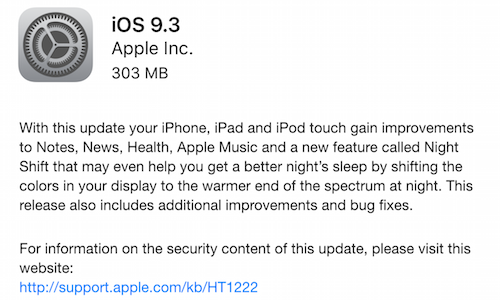
Apple has released iOS 9.3 for iPhones, iPads, and iPod touches, patching a number of security flaws, including a critical iMessages encryption vulnerability (CVE-2016-1788).
This update patches a combined 39 vulnerabilities, one of which was discovered by a group of Johns Hopkins University researchers who found a bug in the Apple’s iMessage encryption that could allow an attacker to decrypt photos and videos sent as secure instant messages.
Ashley Carman over at The Verge described how the discovery of an iMessages encryption vulnerability came about:
“The researchers, including computer science professor Matthew D. Green, exploited the bug through custom software that acted as an Apple server. They used it to target messages that included a link to a photo stored on Apple’s iCloud server along with a 64-digit key to decrypt the image. The researchers didn’t know those digits, but were able to keep guessing until they hit a combination of digits and letters that would let them download the photo.”
In a statement to The Washington Post, Green said:
“Even Apple, with all their skills — and they have terrific cryptographers — wasn’t able to quite get this right. So it scares me that we’re having this conversation about adding back doors to encryption when we can’t even get basic encryption right.”
Apple told The Verge that security improvements in iOS 9.0 “blocked external attackers from performing the message intercept necessary to perform the attack identified in this report [by Johns Hopkins University researchers],” and that “further targeted protections have been added in [iOS 9.3].”
Due to the iMessages vulnerability and the vast number of other flaws patched in iOS 9.3, we recommend all users update your iPhones and other iOS devices immediately.
Following is the full list of vulnerabilities addressed by the iOS 9.3 update:
- CVE-2016-1734 : An application may be able to execute arbitrary code with kernel privileges. A memory corruption issue existed in the parsing of data from USB devices. This issue was addressed through improved input validation.
- CVE-2016-1740 : Opening a maliciously crafted PDF file may lead to an unexpected application termination or arbitrary code execution. A memory corruption issue was addressed through improved memory handling.
- CVE-2015-8659 : A remote attacker may be able to execute arbitrary code. Multiple vulnerabilities existed in nghttp2 versions prior to 1.6.0, the most serious of which may have led to remote code execution. These were addressed by updating nghttp2 to version 1.6.0.
- CVE-2016-1748 : An application may be able to determine kernel memory layout. A memory corruption issue was addressed through improved memory handling.
- CVE-2016-1752 : An application may be able to cause a denial of service. A denial of service issue was addressed through improved validation.
- CVE-2016-1750 : An application may be able to execute arbitrary code with kernel privileges. A use after free issue was addressed through improved memory management.
- CVE-2016-1753 : An application may be able to execute arbitrary code with kernel privileges. Multiple integer overflows were addressed through improved input validation.
- CVE-2016-1751 : An application may be able to bypass code signing. A permissions issue existed in which execute permission was incorrectly granted. This issue was addressed through improved permission validation.
- CVE-2016-1757 : An application may be able to execute arbitrary code with kernel privileges. A race condition existed during the creation of new processes. This was addressed through improved state handling.
- CVE-2016-1756 : An application may be able to execute arbitrary code with kernel privileges. A null pointer dereference was addressed through improved input validation.
- CVE-2016-1754, CVE-2016-1755 : An application may be able to execute arbitrary code with kernel privileges. Multiple memory corruption issues were addressed through improved memory handling.
- CVE-2016-1758 : An application may be able to determine kernel memory layout. An out-of-bounds read issue existed that led to the disclosure of kernel memory. This was addressed through improved input validation.
- CVE-2016-1760 : An application may be able to modify events from other applications. An event handler validation issue existed in the XPC Services API. This issue was addressed through improved message validation.
- CVE-2015-1819, CVE-2015-5312, CVE-2015-7499, CVE-2015-7500, CVE-2015-7942, CVE-2015-8035, CVE-2015-8242, CVE-2016-1761, CVE-2016-1762 : Processing maliciously crafted XML may lead to unexpected application termination or arbitrary code execution. Multiple memory corruption issues were addressed through improved memory handling.
- CVE-2016-1763 : Visiting a maliciously crafted website may auto-fill text into other Message threads. An issue existed in the parsing of SMS URLs. This issue was addressed through improved URL validation.
- CVE-2016-1788 : An attacker who is able to bypass Apple’s certificate pinning, intercept TLS connections, inject messages, and record encrypted attachment-type messages may be able to read attachments. A cryptographic issue was addressed by rejecting duplicate messages on the client.
- CVE-2016-1766 : An untrusted MDM profile may be incorrectly displayed as verified. A certificate validation issue existed in MDM profiles. This was addressed through additional checks.
- CVE-2016-1950 : Processing a maliciously crafted certificate may lead to arbitrary code execution. A memory corruption issue existed in the ASN.1 decoder. This issue was addressed through improved input validation.
- CVE-2016-1775 : Processing a maliciously crafted font file may lead to arbitrary code execution. A memory corruption issue existed in the processing of font files. This issue was addressed through improved input validation.
- CVE-2016-1778, CVE-2016-1783 : Processing maliciously crafted web content may lead to arbitrary code execution. Multiple memory corruption issues were addressed through improved memory handling.
- CVE-2016-1781 : A website may be able to track sensitive user information. An issue existed in the handling of attachment URLs. This issue was addressed through improved URL handling.
- CVE-2016-1780 : A website may be able to track sensitive user information. A hidden web page may be able to access device-orientation and device-motion data. This issue was addressed by suspending the availability of this data when the web view is hidden.
- CVE-2016-1779 : Visiting a maliciously crafted website may reveal a user’s current location. An issue existed in the parsing of geolocation requests. This was addressed through improved validation of the security origin for geolocation requests.
- CVE-2016-1782 : A malicious website may be able to access restricted ports on arbitrary servers. A port redirection issue was addressed through additional port validation.
- CVE-2016-1784 : Processing maliciously crafted web content may lead to an unexpected Safari crash. A resource exhaustion issue was addressed through improved input validation.
- CVE-2016-1786 : Visiting a malicious website may lead to user interface spoofing. Redirect responses may have allowed a malicious website to display an arbitrary URL and read cached contents of the destination origin. This issue was addressed through improved URL display logic.
- CVE-2016-1785 : A malicious website may exfiltrate data cross-origin. A caching issue existed with character encoding. This was addressed through additional request checking.
- CVE-2016-0801, CVE-2016-0802 : An attacker with a privileged network position may be able to execute arbitrary code. A frame validation and memory corruption issue existed for a given ethertype. This issue was addressed through additional ethertype validation and improved memory handling.
iOS 9.3 is available for the iPhone 4s and later, iPod touch (5th generation) and later, and the iPad 2 and later.
Apple iOS users can download and install the iOS 9.3 update through iTunes or through your device settings (select General > Software Update).

