iOS 8 Has Arrived! ‘Biggest Update’ Packed with Security Fixes
Posted on
by
Derek Erwin
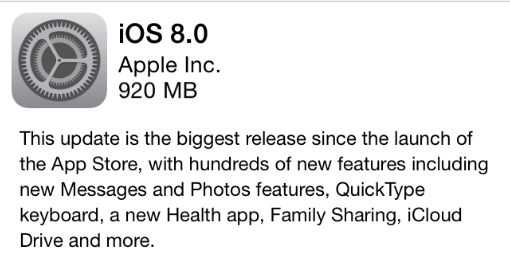
iOS 8 has arrived! Apple has just released iOS 8, the company’s biggest update since the launch of the App Store. This is without question the most comprehensive, detailed upgrade Apple has ever offered to its iPhone, iPad software.
There are so many fantastic new features in iOS 8, it will take more than one article to review them all. On the more exciting features, it comes with “hundreds of new features including new Messages and Photos features, QuickType keyboard, a new Health app, Family Sharing, iCloud Drive and more.” On security, a whopping 56 vulnerabilities have been resolved, and that’s just the tip of the iceberg!
RELATED: iOS 8 Tip: Read This Before You Upgrade to iCloud Drive
This update is available for iPhone 4s and later, iPod touch (5th generation) and later, iPad 2 and later.
In addition to addressing vulnerabilities (CVEs), Apple also applied security updates to the iOS certificate trust policy. (The complete list of certificates can be found here.)
Moreover, an iOS information disclosure issue was discovered in an API used to determine local weather; location information was being sent unencrypted. Apple fixed this issue by changing APIs.
Apple also addressed a privacy issue after finding that an iOS device may be passively tracked by its Wi-Fi MAC address. Apple noted, “An information disclosure existed because a stable MAC address was being used to scan for Wi-Fi networks.” Apple addressed the issue by randomizing the MAC address for passive Wi-Fi scans.
The vulnerabilities resolved in the iOS 8 update are described as follows:
- CVE-2014-4364 : An attacker can obtain WiFi credentials. An attacker could have impersonated a WiFi access point, offered to authenticate with LEAP, broken the MS-CHAPv1 hash, and used the derived credentials to authenticate to the intended access point even if that access point supported stronger authentication methods. This issue was addressed by disabling LEAP by default.
- CVE-2014-4423 : A malicious application may be able to identify the Apple ID of the user. An issue existed in the access control logic for accounts. A sandboxed application could get information about the currently-active iCloud account, including the name of the account. This issue was addressed by restricting access to certain account types from unauthorized applications.
- CVE-2014-4368 : The device may not lock the screen when using AssistiveTouch. A logic issue existed in AssistiveTouch’s handling of events, which resulted in the screen not locking. This issue was addressed through improved handling of the lock timer.
- CVE-2014-4357 : An attacker with access to an iOS device may access sensitive user information from logs. Sensitive user information was logged. This issue was addressed by logging less information.
- CVE-2014-4352 : A person with physical access to an iOS device may read the address book. The address book was encrypted with a key protected only by the hardware UID. This issue was addressed by encrypting the address book with a key protected by the hardware UID and the user’s passcode.
- CVE-2014-4386 : A local attacker may be able to escalate privileges and install unverified applications. A race condition existed in App Installation. An attacker with the capability of writing to /tmp may have been able to install an unverified app. This issue was addressed by staging files for installation in another directory.
- CVE-2014-4384 : A local attacker may be able to escalate privileges and install unverified applications. A path traversal issue existed in App Installation. A local attacker could have retargeted code signature validation to a bundle different from the one being installed and cause installation of an unverified app. This issue was addressed by detecting and preventing path traversal when determining which code signature to verify.
- CVE-2014-4383 : An attacker with a privileged network position may be able to cause an iOS device to think that it is up to date even when it is not. A validation issue existed in the handling of update check responses. Spoofed dates from Last-Modified response headers set to future dates were used for If-Modified-Since checks in subsequent update requests. This issue was addressed by validation of the Last-Modified header.
- CVE-2014-4354 : Bluetooth is unexpectedly enabled by default after upgrading iOS. Bluetooth was enabled automatically after upgrading iOS. This was addressed by only turning on Bluetooth for major or minor version updates.
- CVE-2014-4377 : Opening a maliciously crafted PDF file may lead to an unexpected application termination or arbitrary code execution. An integer overflow existed in the handling of PDF files. This issue was addressed through improved bounds checking.
- CVE-2014-4378 : Opening a maliciously crafted PDF file may lead to an unexpected application termination or an information disclosure. An out of bounds memory read existed in the handling of PDF files. This issue was addressed through improved bounds checking.
- CVE-2013-6835 : Tapping on a FaceTime link in Mail would trigger a FaceTime audio call without prompting. Mail did not consult the user before launching facetime-audio:// URLs. This issue was addressed with the addition of a confirmation prompt.
- CVE-2014-4374 : An application using NSXMLParser may be misused to disclose information. An XML External Entity issue existed in NSXMLParser’s handling of XML. This issue was addressed by not loading external entities across origins.
- CVE-2014-4361 : A background app can determine which app is frontmost. The private API for determining the frontmost app did not have sufficient access control. This issue was addressed through additional access control.
- CVE-2014-4353 : Attachments may persist after the parent iMessage or MMS is deleted. A race condition existed in how attachments were deleted. This issue was addressed by conducting additional checks on whether an attachment has been deleted.
- CVE-2014-4369 : An application may cause an unexpected system termination. A null pointer dereference existed in the handling of IOAcceleratorFamily API arguments. This issue was addressed through improved validation of IOAcceleratorFamily API arguments.
- CVE-2014-4373 : The device may unexpectedly restart. A NULL pointer dereference was present in the IntelAccelerator driver. The issue was addressed by improved error handling.
- CVE-2014-4379 : A malicious application may be able to read kernel pointers, which can be used to bypass kernel address space layout randomization. An out-of-bounds read issue existed in the handling of an IOHIDFamily function. This issue was addressed through improved bounds checking.
- CVE-2014-4404 : A malicious application may be able to execute arbitrary code with system privileges. A heap buffer overflow existed in IOHIDFamily’s handling of key-mapping properties. This issue was addressed through improved bounds checking.
- CVE-2014-4405 : A malicious application may be able to execute arbitrary code with system privileges. A null pointer dereference existed in IOHIDFamily’s handling of key-mapping properties. This issue was addressed through improved validation of IOHIDFamily key-mapping properties.
- CVE-2014-4380 : A malicious application may be able to execute arbitrary code with kernel privileges. An out-of-bounds write issue existed in the IOHIDFamily kernel extension. This issue was addressed through improved bounds checking.
- CVE-2014-4407 : A malicious application may be able to read uninitialized data from kernel memory. An uninitialized memory access issue existed in the handling of IOKit functions. This issue was addressed through improved memory initialization.
- CVE-2014-4418 : A malicious application may be able to execute arbitrary code with system privileges. A validation issue existed in the handling of certain metadata fields of IODataQueue objects. This issue was addressed through improved validation of metadata.
- CVE-2014-4388 : A malicious application may be able to execute arbitrary code with system privileges. A validation issue existed in the handling of certain metadata fields of IODataQueue objects. This issue was addressed through improved validation of metadata.
- CVE-2014-4389 : A malicious application may be able to execute arbitrary code with system privileges. An integer overflow existed in the handling of IOKit functions. This issue was addressed through improved validation of IOKit API arguments.
- CVE-2014-4371, CVE-2014-4419, CVE-2014-4420, CVE-2014-4421 : A local user may be able to determine kernel memory layout. Multiple uninitialized memory issues existed in the network statistics interface, which led to the disclosure of kernel memory content. This issue was addressed through additional memory initialization.
- CVE-2011-2391 : A person with a privileged network position may cause a denial of service. A race condition issue existed in the handling of IPv6 packets. This issue was addressed through improved lock state checking.
- CVE-2014-4375 : A local user may be able to cause an unexpected system termination or arbitrary code execution in the kernel. A double free issue existed in the handling of Mach ports. This issue was addressed through improved validation of Mach ports.
- CVE-2014-4408 : A local user may be able to cause an unexpected system termination or arbitrary code execution in the kernel. An out-of-bounds read issue existed in rt_setgate. This may lead to memory disclosure or memory corruption. This issue was addressed through improved bounds checking.
- CVE-2014-4422 : Some kernel hardening measures may be bypassed. The random number generator used for kernel hardening measures early in the boot process was not cryptographically secure. Some of its output was inferable from user space, allowing bypass of the hardening measures. This issue was addressed by using a cryptographically secure algorithm.
- CVE-2014-4381 : A malicious application may be able to execute arbitrary code with root privileges. An out-of-bounds write issue existed in Libnotify. This issue was addressed through improved bounds checking.
- CVE-2014-1360 : A device can be manipulated into incorrectly presenting the home screen when the device is activation locked. An issue existed with unlocking behavior that caused a device to proceed to the home screen even if it should still be in an activation locked state. This was addressed by changing the information a device verifies during an unlock request.
- CVE-2014-4366 : Login credentials can be sent in plaintext even if the server has advertised the LOGINDISABLED IMAP capability. Mail sent the LOGIN command to servers even if they had advertised the LOGINDISABLED IMAP capability. This issue is mostly a concern when connecting to servers that are configured to accept non- encrypted connections and that advertise LOGINDISABLED. This issue was addressed by respecting the LOGINDISABLED IMAP capability.
- CVE-2014-1348 : A person with physical access to an iOS device may potentially read email attachments. A logic issue existed in Mail’s use of Data Protection on email attachments. This issue was addressed by properly setting the Data Protection class for email attachments.
- CVE-2014-4367 : Voice Dial is unexpectedly enabled after upgrading iOS. Voice Dial was enabled automatically after upgrading iOS. This issue was addressed through improved state management.
- CVE-2013-5227 : User credentials may be disclosed to an unintended site via autofill. Safari may have autofilled user names and passwords into a subframe from a different domain than the main frame. This issue was addressed through improved origin tracking.
- CVE-2014-4363 : An attacker with a privileged network position may intercept user credentials. Saved passwords were autofilled on http sites, on https sites with broken trust, and in iframes. This issue was addressed by restricting password autofill to the main frame of https sites with valid certificate chains.
- CVE-2014-4362 : Apple ID information is accessible by third-party apps. An information disclosure issue existed in the third-party app sandbox. This issue was addressed by improving the third-party sandbox profile.
- CVE-2014-4356 : Text message previews may appear at the lock screen even when this feature is disabled. An issue existed in the previewing of text message notifications at the lock screen. As a result, the contents of received messages would be shown at the lock screen even when previews were disabled in Settings. The issue was addressed through improved observance of this setting.
- CVE-2014-4372 : A local user may be able to change permissions on arbitrary files. syslogd followed symbolic links while changing permissions on files. This issue was addressed through improved handling of symbolic links.
- CVE-2014-4409 : A malicious website may be able to track users even when private browsing is enabled. A web application could store HTML 5 application cache data during normal browsing and then read the data during private browsing. This was addressed by disabling access to the application cache when in private browsing mode.
- CVE-2013-6663, CVE-2014-1384, CVE-2014-1385, CVE-2014-1387, CVE-2014-1388, CVE-2014-1389, CVE-2014-4410, CVE-2014-4411, CVE-2014-4412, CVE-2014-4413, CVE-2014-4414, CVE-2014-4415 : Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution. Multiple memory corruption issues existed in WebKit. These issues were addressed through improved memory handling.
This update is available directly on iOS devices (Settings > General > Software Update), or it can be downloaded and installed in iTunes when a device is connected to a computer with an Internet connection.