Fake “Geek Squad” emails: Call center scam leverages Intuit QuickBooks servers
Posted on
by
Joshua Long and Kirk McElhearn

A series of scam e-mails is circulating, purporting to be from Best Buy or one of its brands, Totaltech or Geek Squad. The e-mails include a fake invoice indicating that you’re being charged hundreds of dollars. Here’s everything you need to know to stay protected from this scam.
In this article:
- What does the “Invoice from Totaltech” scam claim to be?
- How can I recognize similar scam e-mails?
- Why has this scam suddenly gained new attention?
- What happens if I call the “customer service” number?
- How can I report these scammers?
- How can I learn more?
What does the “Invoice from Totaltech” scam claim to be?
Best Buy is an electronics store chain that is mostly based in the U.S. The chain’s Totaltech and Geek Squad technical support services are among its most well-known offerings.
The scam revolves around tricking recipients of the e-mails into believing that they’re receiving erroneous invoices from the company. The goal is to get people to call a “helpline” number found in the e-mail body and the attached “invoice.”
In reality, the “helpline” is a scam support center staffed by fraudsters.
How can I recognize similar scam e-mails?
Recently, this particular e-mail campaign has been using subject lines similar to the following:
- “Invoice 676318 from Best Buy Totaltech™”
- “Invoice 706223 from Totaltech™GeekSquad”
The body of the e-mail might look something like this:
Dear Customer,
Your invoice-706223 for 199.99 is attached towards renewal of 3 years Subscription.
Customer Service for the USA & Canada /1’888’/’397’/’****’/
Thank you for your business – we appreciate it very much.
Sincerely,
Totaltech™GeekSquad
/1’888’/’397’/’****’/
All of the e-mails we received were sent by “Intuit E-Commerce Service” from the address [email protected] — more on that later.
The call center phone numbers we’ve observed used in this scam are 888 toll-free numbers followed by 397, and ending in either 5636 or 5641. It’s very likely that they’re using other numbers as well.
Although it’s less relevant, in case people search for these things we’ll note that the “To:” address was similar to paid*@inq4*[.]cfd. The “Reply-To:” field address varied, but sometimes included domains that looked vaguely like Best Buy, such as noreply@basebytech[.]com or noreply@bestbuytec[.]com. Of course, all of this can vary with each new e-mail the scammers send out.
A quick Web search reveals that similar scam messages have been circulating for several months. It was so prevalent back in October that the U.S. Federal Trade Commission (FTC) warned about it.
Why has this scam suddenly gained new attention?
Evidently, the fraudsters behind this spam-and-scam campaign have figured out that by leveraging a legitimate invoicing service, they can send out massive amounts of fake invoices and avoid getting caught in spam filters.
Intuit, the company behind popular services like TurboTax and QuickBooks, also operates an invoicing service under the latter brand. Most online business accounting software allows users to generate and send invoices.
The e-mails pushing this scam are actually — in reality — sent via Intuit’s e-mail servers.
The scammers have probably imported thousands of email addresses, and have instructed the software to generate invoices for each of these accounts. There could be a legitimate use for this: a company may have 10,000 users of online software that they need to bill every month, so it would be normal for them to generate monthly invoices. Intuit describes the process in this support document.
The software creates invoices and then sends them to the email addresses the scammers are targeting. The e-mails and invoices don’t contain customer names, which would be more common for real business invoices, so the scammers don’t need to add any additional information.
It would, of course, be possible for scammers to generate a single PDF of an invoice and email it to thousands of addresses on their own. In fact, that’s probably what earlier versions of this scam did, like the FTC described back in October.
But if scammers generate and mail out their own PDF invoices manually, they miss one key advantage that they get by sending via a legitimate invoicing service: spam-filter exemption. Since Intuit’s globally whitelisted servers are sending these emails, they get through spam filters — both in email relays and at email providers, such as Gmail.
What happens if I call the “customer service” number?
Out of curiosity, I called one of the supposed customer service numbers and role-played an unaware victim, to see what else I could learn about the scam.
The scammer’s recently registered domain
The person who answered the call told me to open Google Chrome and go to os911[.]org — which surprisingly doesn’t yet seem to be on any major blacklists. The domain was registered just a month ago, on March 15, 2023.
The site asks visitors to enter a “secure code,” which the scammer gave to me. Entering a random code does not allow you to proceed, making it more difficult for others to see what the site is really up to.
The scammer’s so-called “secure support app”
The site then prompted me to download software that claimed to be a “Secure Support App.”
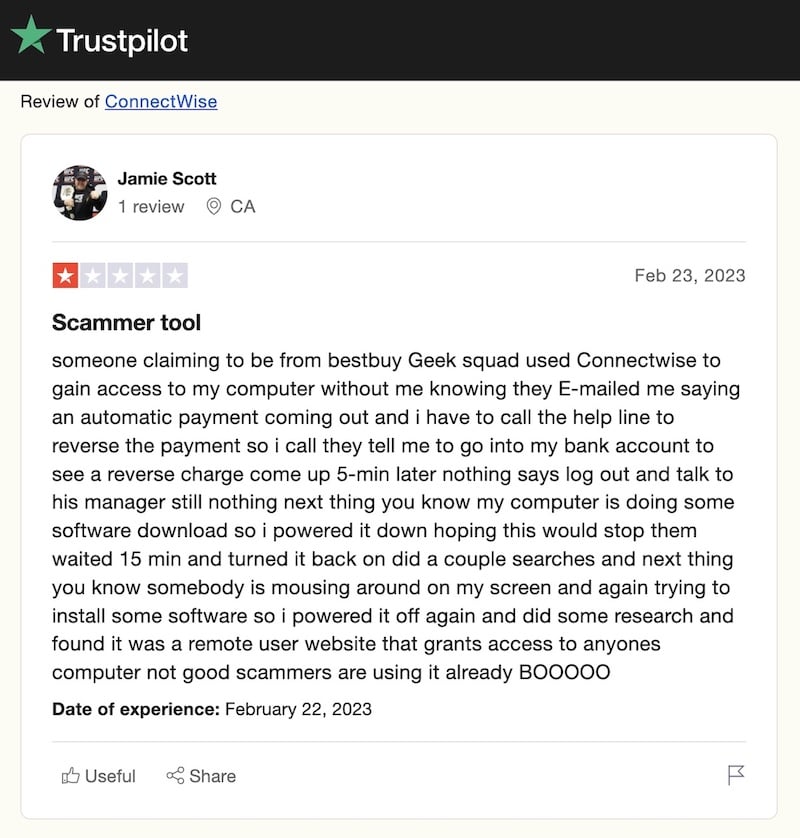
Once the app eventually finished downloading, I could see that it was a Java app signed by ConnectWise, Inc (K8M3XDZV9Y), a technology service provider. Apparently, scammers use this tool often, according to reviews like this one on the company’s Trustpilot page.
In any case, apparently the scammer didn’t expected me to get a prompt to download an app. They asked if I had a Mac or Windows, and I said a Mac. The scammer seemed frustrated.
Calling back the scammer on another number
Next, the scammer asked for my callback number. When I asked why they needed to call me back, they said I was calling from a Netherlands number. This was news to me; in reality, I was using a Web site to make the call, to avoid disclosing my real phone number.
They asked if I had a U.S. number where they could reach me. I said no, so they told me to call them back at a different (non-toll-free) number in ten minutes. The number began with (606) 303-xxxx, which the Whitepages Reverse Phone Lookup app claimed was a landline, but according to Whitepages’ site is a Verizon Wireless number in Lexington, Kentucky. How fun; could this be the scammer’s personal cell phone number?
But when I called back, the scammer didn’t answer my call; it went to voicemail. The generic recording indicated it was actually a TextNow number. According to TextNow’s App Store description, it appears that anyone, anywhere in the world, could have been using the number.
Others have reported on their experiences with scams like these, as did the Trustpilot reviewer I mentioned earlier. This victim claimed that the scammer maintained an active connection to the computer even after having shut it down, and that the scammer kept trying to download additional software.
How can I report these scammers?
Intuit’s site suggests forwarding phishing or technical support scam e-mails that appear to come from their service to [email protected] — although it’s unclear how quickly the company will take action.
We discovered evidence that similar scams have been abusing Intuit’s invoicing service since at least December 2021, if not earlier. Given how long these scams have been ongoing, Intuit’s response to the abuse of its services seems to be largely reactionary, rather than proactive.
If Intuit doesn’t get its act together, it’s possible that major spam filters, like that of Gmail, could start flagging legitimate Intuit E-Commerce Service invoices as spam. Of course, that assumes Intuit isn’t completely exempt from Google’s spam-categorizing algorithm, which it might be. But if that’s the case, Google and others may want to rethink that policy.
In addition to forwarding such e-mails to Intuit’s security department, it’s also a good idea to forward the e-mails to the FTC at [email protected], as well as to the Anti-Phishing Working Group at [email protected]. The latter organization, APWG, is a coalition of international law enforcement agencies and tech companies that work together to take down identity thieves and fraudsters.
If you happen to get a fraudster’s TextNow number, you can contact [email protected] to inform them the account is being used for fraud.
And if you believe you’ve fallen victim to one of these scams, inform the FTC; go to ReportFraud.ftc.gov and fill out the form. You may also find it helpful to review Intego’s video about how to report scams before submitting your report.
How can I learn more?
For more details about this scam, listen to (or read the transcript of) episode 287 of the Intego Mac Podcast; we discuss this scam from 15:26 to 20:27.
Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, including security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
You can also subscribe to our e-mail newsletter and keep an eye here on The Mac Security Blog for the latest Apple security and privacy news. And don’t forget to follow Intego on your favorite social media channels: ![]()
![]()
![]()
![]()
![]()
![]()
![]()

