Emergency iOS 9.3.5 Update Thwarts Pegasus Spyware—Patch Now!
Posted on
by
Jay Vrijenhoek
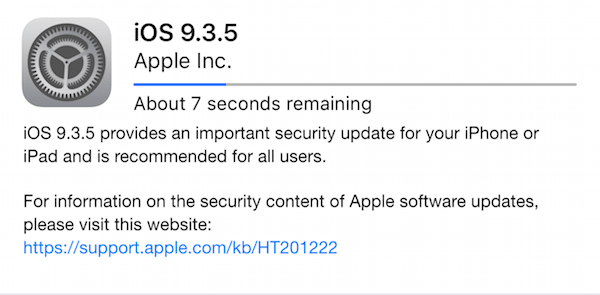
Apple today released iOS update 9.3.5, available for iPhone 4s and later, iPad 2 and later and iPod touch (5th generation) and later. The update addresses three vulnerabilities and received the same generic listing as most other updates do. Yet there is much more to this update than what Apple mentions in their documentation.
Discovered by Citizen Lab and Lookout, these three vulnerabilities have been named “Trident.” Exploiting Trident will give an attacker access to your messages, calls, emails, and logs from apps like Gmail, Facebook, Skype, WhatsApp, FaceTime, Calendar, and Viber, among others.
As it turns out, a company called NSO Group (an Israeli-based organization that is said to specialize in cyber warfare and sells their services to governments) has been exploiting Trident as part of one of their spyware products, called Pegasus.
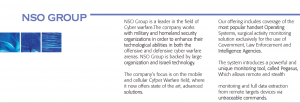
Image from an NSO Group brochure posted on SIBAT (The International Defense Cooperation Directorate of the Israel Ministry of Defense).
Pegasus is the most sophisticated attack we’ve seen on any endpoint because it takes advantage of how integrated mobile devices are in our lives and the combination of features only available on mobile — always connected (WiFi, 3G/4G), voice communications, camera, email, messaging, GPS, passwords, and contact lists. It is modular to allow for customization and uses strong encryption to evade detection. (source)
By sending a victim a phishing text message with a malicious URL, if opened, a web browser will load a page and the page contents will exploit those vulnerabilities. As these vulnerabilities were not known until now, there was no defense and a victim would not even know the device had been compromised. Citizen Lab and Lookout believe that this spyware has been around for years, as far back as iOS 7.
Other orgs spoofed by NSO via lookalike domains include YouTube, Facebook, Google, Univision, BBC, CNN and AlJazeera pic.twitter.com/nIwKNVDnNC
— Christopher Soghoian (@csoghoian) August 25, 2016
Citizenlab also wrote a report that describes how Trident was exploited to target human rights defender Ahmed Mansoor. Other sources state this was the exploit used to target New York Times journalists recently. Needless to say this is a significant exploit. Citizen Lab and Lookout worked directly with Apple’s security team and the 9.3.5 update was created to address the Trident vulnerabilities.
I strongly recommended updating all your iOS devices that support iOS 9.3.5 as soon as possible. To do so, on your iPhone or iPad simply go to Settings > General > Software Update, or you can download and install the update in iTunes when your iOS device is connected to a computer with an Internet connection. As with any update, make sure you have a backup to iCloud or iTunes before installing.

