Blackhat Brings News of Malicious iOS Charger
Posted on
by
Lysa Myers
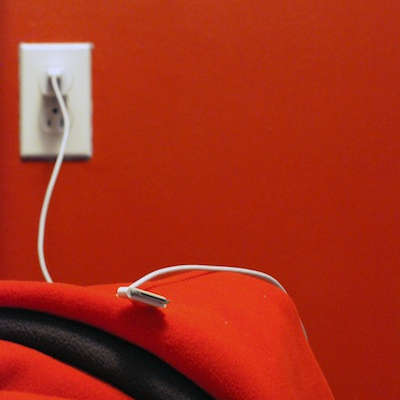
Each year, with the start of the BlackHat security conference, thousands of hackers and researchers descend upon the Las Vegas desert. And their arrival is always preceded by spectacular tales of hacking they’ve done during the previous year. In past years, there has been such spectacular headline fodder as “ATM Jackpotting” and “Lethal Pacemaker Attacks.” This year is no different, as it brings us “Evil iOS Chargers.”
Usually I read these things with an appreciation for the theatrics of it all and just roll my eyes as I move on to the next news story. But since this one pertains to an Apple product, I thought I would take a moment to discuss this tale.
The short of it is, this is nothing to worry about. While the coverage is terribly inflammatory and dramatic, it isn’t something that is now being used (or likely ever will be) in the real world.
The simple fact is, malware authors have plenty of attack surface to cover with Windows, OS X, Linux and Android. They don’t need to get into manufacturing devices and working out how to slip them unnoticed into people’s luggage, to get into these platforms. The information is interesting from an academic perspective, and it’s possible future versions of iOS will address this, but it really isn’t a pressing concern by any stretch of the imagination.