Switch default apps on iPhone or iPad for better security and privacy
Posted on
by
Kirk McElhearn
Modern operating systems, both on the desktop and on mobile devices, include plenty of “stock apps”—apps provided by default so you can use your device without needing a lot of third-party software. You get an email app, a calendar, a web browser, a messaging app, and more. This wasn’t always the case; I remember when I needed to buy an email app for my Mac, and when I had to pay for a basic calendar app.
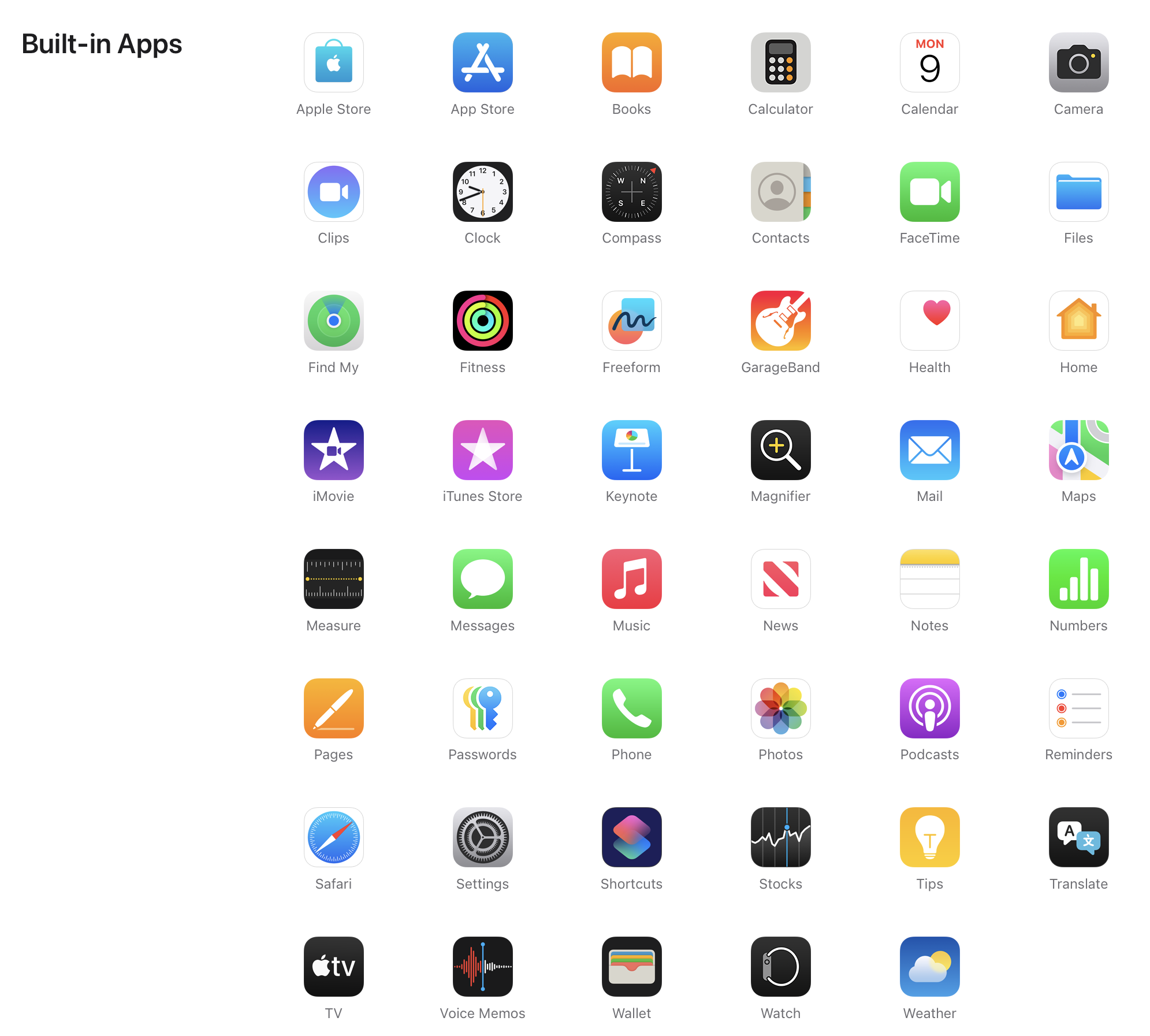
Apple includes more than 40 default apps on iOS and iPadOS (though the exact number may vary from one major operating system version or device to the next). You can download another dozen Apple apps, such as the iWork apps (Pages, Numbers, and Keynote), GarageBand, and more. Visit the Apps by Apple web page to learn about all these default apps.
While many of these apps are excellent, you may want to change some of them to use apps you prefer—and, in some cases, to enhance your security and privacy.
Switching default apps
There are lots of apps on your phone, each of which has a specific usage. You have an app to browse the web, another to send and receive email, one to take photos, and another one to make phone calls.
Some of these apps work in certain ways that links them to the operating system. For example, if you tap a link that begins with https:, a web browser will open that link. If you tap a link that begins with mailto: to send someone an email, then your mail app opens. While you can manually launch any web browser and type or paste an address, or manually start composing an email in any email app, it’s this connection to specific types of apps via the Uniform Resource Identifier (URI) scheme that opens your selected app.
Other features that aren’t global, but that are part of iOS, also trigger specific apps. For example, if you tap a phone number or a message link on a contact card, your iPhone or iPad will open the default phone or messaging app. All the apps in the Default Apps settings (more on that in a moment) function like this, either via a URI or through internal links in iOS. If you use apps other than these defaults, you may want to change the default apps.
Why can’t you change more default apps?
You may wonder why you can’t set more default apps, such as for the Music, Camera, or Photos apps. These apps don’t respond to any URI or system-level integration. You can install any third party apps like this that you want, but you can’t link them to work with other apps.
It would be nice to be able to set a default camera app, so it would launch when you swipe left on your lock screen. Or you might even want to have Apple’s Camera app store your photos in Google Photos or Flickr, rather than iCloud. Perhaps Apple will offer this sort of integration in the future.
How to change the default apps on iPhone or iPad
Go to Settings, scroll down to the bottom of the screen, then tap Apps. At the top of the next screen, tap Default Apps, and you’ll see this screen:
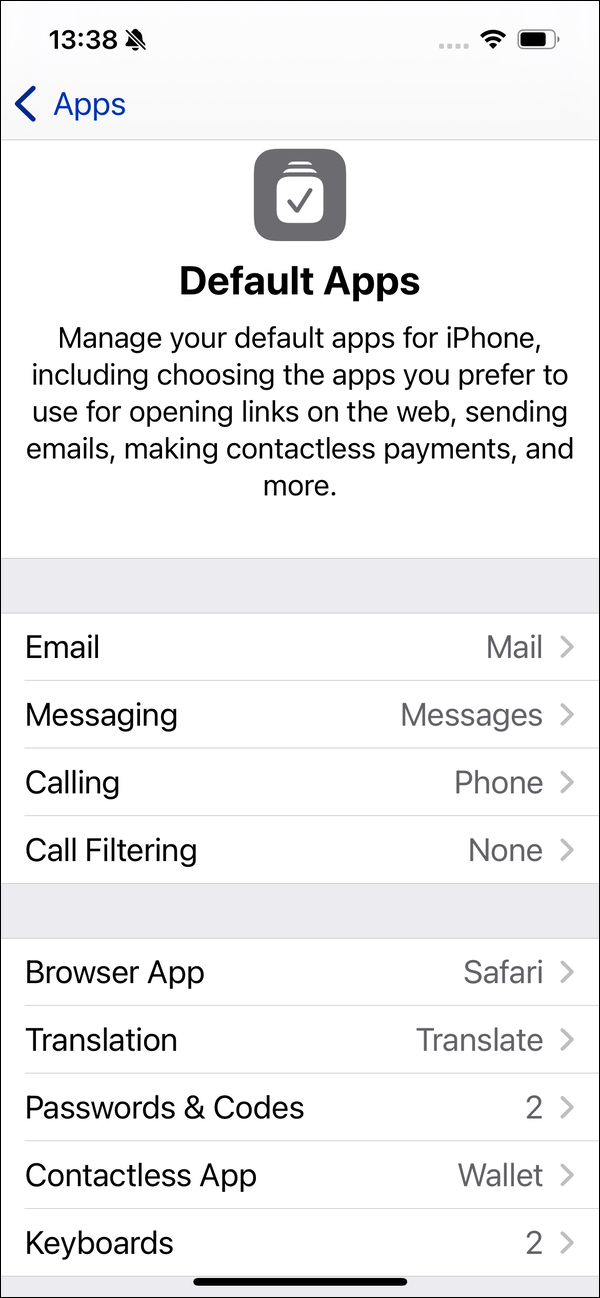
As you can see, there are about nine different app classifications, grouped into two sections. The first group of apps is for communicating with other people, and the second group is all the rest.
Let’s go through each of these app categories and discuss what options are available.
If you want to use a different email app, tap this entry and choose your app. For example, if you have the Gmail app installed, you’ll see it here as an option. If, however, you only use Gmail in a web browser, you won’t see it here. There are a number of third-party email apps that you can use, though not all of them display in these settings. For example, I installed email apps for the two services discussed below on my iPhone, and only Tuta Mail showed up in these options; Proton Mail did not.
Why you might want to use a secure email service
Email is inherently insecure. Messages are sent unencrypted, in plain text, and reside on remote servers. They can be intercepted at many points between the sender and recipient, and are no more secure than postcards. So if you need to send and receive confidential information, you should consider using an alternative email app (or, perhaps, some method of communication other than email).
How exactly is email like a postcard? Although most email servers support encryption between the device sending the email and the email server itself (similar to how HTTPS securely connects your browser to a web server), messages may be stored on mail servers in plaintext (i.e. without encryption), or transmitted further down the line on the way to their destinations in plaintext. This makes email servers a potentially interesting target for spy agencies and hackers alike. Furthermore, end users’ devices typically store emails in plaintext, too. If either an email recipient’s device or an email server gets hacked or becomes infected, an attacker could read the contents of unencrypted emails.
Mail on macOS allows you to digitally sign or encrypt emails There are some complex ways to work with encrypted email using Apple’s Mail on iOS, but they require a lot of steps to get them to work.
To send and receive encrypted email, a simpler solution is to create an account with a company that provides such a service. You won’t use Apple’s Mail app for your email, but rather an app provided by such a company, or you’ll access your email by logging into their website.
Privacy-focused email services
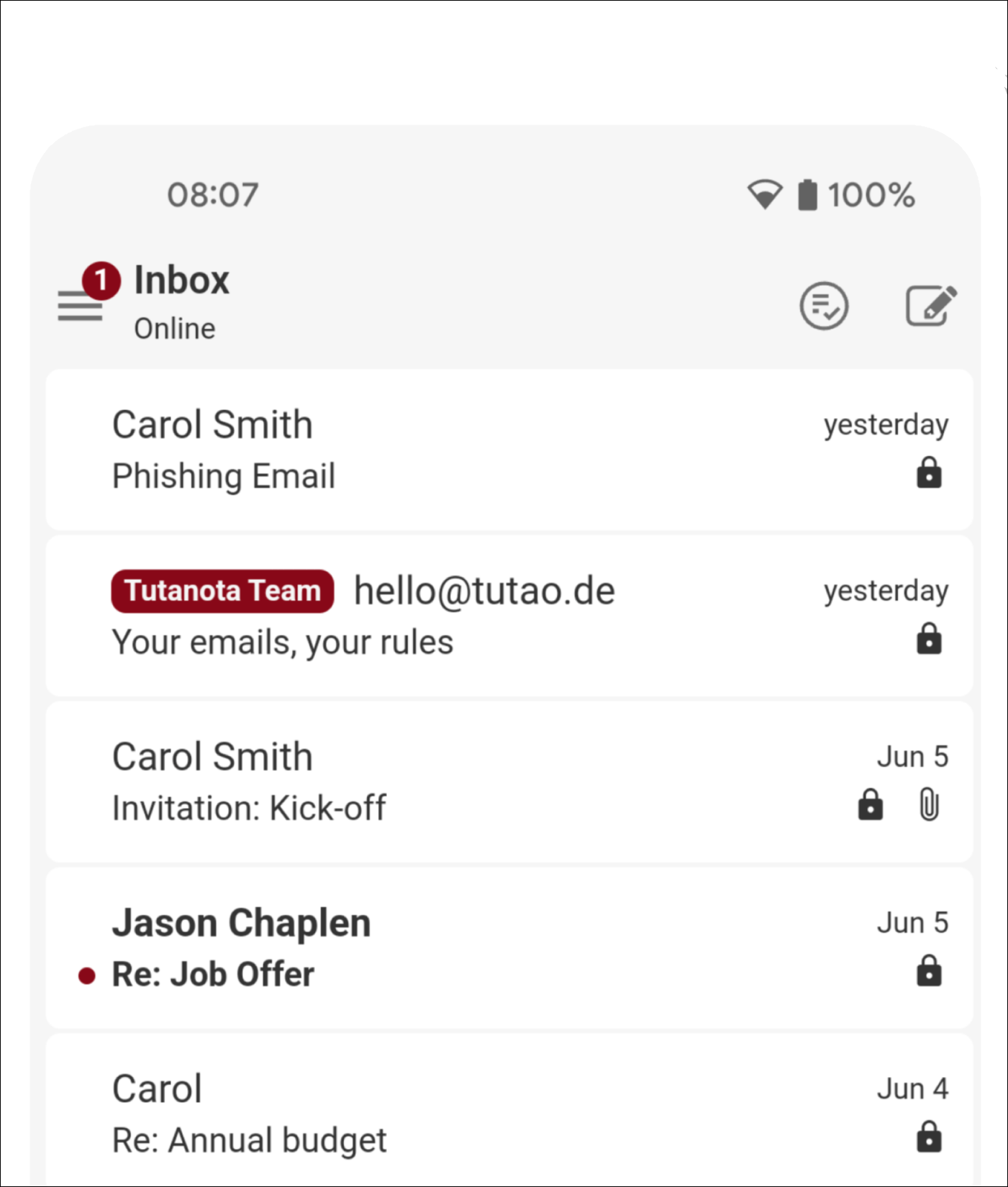
Tuta – previously Tutanota – provides secure email with end-to-end encryption and two-factor authentication. There is a free option, which offers up to 1 GB storage, and there are premium and pro plans that let you use a custom domain, add email aliases, increase storage, etc. The company’s email client is available for iOS and Android, and you can also use webmail.
You can send messages from Tutanota to people not using the service, and they are password protected. So even if you send an email to someone using, say, Gmail, they’ll only be able to read the message if they have the password, and the message’s content remains encrypted on Gmail’s servers.
ProtonMail is another secure email provider. It also offers end-to-end encryption, and boasts that its email servers, housed in Switzerland, reside in “Europe’s most secure datacenter, underneath 1000 meters of solid rock.” Available for iOS, Android, and via the web, and you can use it with your standard Mac email client if you install ProtonMail Bridge. You can send emails to people not using ProtonMail, and they can read your messages after entering a password. ProtonMail offers free and paid versions, the latter with more storage, custom domains, etc.
It’s clear that most people won’t need to encrypt all their emails, so you can use Tutanota or ProtonMail for sensitive messages, and use Mail or another client for the rest of your email. Secure email systems are most efficient if both senders and recipients are using the same service, such as in a company or other organization, for example.
Messaging and phone calls
As of now, there aren’t any options to change the default messaging app on iPhone or iPad; only Apple’s iMessage is available.. Apple says this setting allows you to choose an app “to use when opening links to send instant messages,” but, in spite of having Signal and WhatsApp on my iPhone, I don’t see them here. This should change it some point in the future, and it may depend on the third-party apps supporting specific APIs (application-programming interfaces) in iOS and iPadOS.
For calling, there are two options: Phone and FaceTime. As with messaging, there are no other choices yet, but that may change.
Secure messaging and calling services
Apple’s iMessage and FaceTime services offer end-to-end encryption, meaning Apple cannot tap into your live conversations. However, iMessage is only available for messaging between two or more Apple devices, so its end-to-end encryption unfortunately doesn’t apply to messages exchanged with users of Android smartphones or other phones. (You’ll know you’re using iMessage, as opposed to an SMS or MMS text message, if you see a “blue bubble” instead of a “green bubble” when sending messages to the recipient.) If you need to send secure messages to people on other platforms, you have a lot of options.
In spite of offering end-to-end encryption, some other concerns about iMessage have come to light in recent years. Trustjacking can make it possible for an attacker to obtain your iMessages from local backups, unbeknownst to you. Furthermore, iMessages can (optionally) be backed up to iCloud servers, and iCloud backups are accessible to select Apple employees—i.e. they’re not stored encrypted in such a way that you’re the only one who can access them. That could potentially mean your messages might fall into the hands of government entities who request that data, rogue Apple employees, or attackers who either compromise an authorized Apple employee’s account or iCloud servers. For iCloud users in mainland China, messages backed up to iCloud are actually stored on servers operated by the Chinese government.
Unlike web and email links, iOS doesn’t open a messaging app by default, at least not yet. You can use as many messaging apps as you want, as many people do. The list is long: WeChat, WhatsApp, Facebook Messenger, Viber, Line, Slack, Google Hangouts, and many more. Most of these apps offer end-to-end encryption, but some provide more security than others.
Signal offers text, voice, video, group chats, and document sharing, with full end-to-end encryption, and you can even set your messages to self-destruct. It is free and open source. Journalism and privacy organizations recommend Signal because of its security and the fact that the service does not store metadata, information about who you communicate with. You can send standard SMS messages to non-Signal users, and they are not encrypted, so you can (in a sense) use Signal as your default messaging app.

WhatsApp offers secure messaging and calling, and it uses Signal’s protocol, but the fact that it is owned by Facebook makes some people uncomfortable (Facebook, like Google, has a poor reputation when it comes to respecting end-user privacy). There are particularly issues with WhatsApp and the way messages can be forwarded, leading to the distribution of fake news. And reportedly most WhatsApp messages are stored unencrypted.
Call Filtering
This setting allows you to choose an “app to use for presenting caller ID and blocking unwanted callers.”
Web Browser
You can choose a web browser here, and it seems that all third-party browsers are supported. But why would you want to use a different web browser?
While Safari is an excellent web browser, and Apple is doing good things with its Intelligent Tracking Prevention technology (see Apple’s white paper PDF about this), there are other browsers that can enhance your security and privacy in other ways.  Some browsers, such as Brave, include built-in ad and tracker blocking, can optionally enforce HTTPS for any site that supports it, and allow users to disable JavaScript by default whenever it isn’t needed.
Some browsers, such as Brave, include built-in ad and tracker blocking, can optionally enforce HTTPS for any site that supports it, and allow users to disable JavaScript by default whenever it isn’t needed.
We have an extensive article about which is the most private browser for iPhone and iPad, discussing alternative browsers and their advantages and disadvantages.
Translation
New in iOS 18.3 and iPadOS 18.4, this option lets you choose an app to translate for you. As of now, only Apple’s Translate shows up here.
Passwords & Codes
Here, you can change the default app to use “instead of the Passwords app to use for Password AutoFill in Safari and other apps.” In addition to this, many password managers have browser extensions allowing you to use both. And when you encounter a password field, the small key icon above your keyboard lets you access any password manager you have on your device.
Choosing a password manager
One essential element of security is ensuring that you have strong passwords to protect your accounts. iOS and iPadOS include Apple’s Passwords app, which allows you to store, sync, and generate passwords on iPhones, iPads, and Macs, as well as managing two-factor authentication codes. While this app is great, it is limited. You can install iCloud for Windows to access your passwords on a PC, but you cannot access these passwords on an Android device, even if you sign into iCloud on the web.
So if all your devices are Apple devices, the Passwords app is fine. If not, consider using 1Password, Bitwarden, Dashlane, or another trusted password manager so you have more flexibility when you need to enter passwords.
Related article:
4 Best Password Managers in 2025: How to choose the right one for you
Contactless App
In some countries and regions, notably the European Union, this setting lets you “choose another app to make contactless transactions using your device’s built-in technology.” However, this is visible in countries outside the EU, so perhaps Apple is planning to extend this capability.
Keyboards
This allows you to change the system-wide keyboard used on your device. This has been possible for many years, and you can also make this change in Settings > Keyboard > Keyboards.
While you can only change the defaults for a handful of apps, it’s easy to switch these default apps for ones you prefer to use. If you do use a different browser, email client, or other app this list, make the change so the app is easier to work with, and to use an app more focused on security and privacy.
How can I learn more?
 Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
Each week on the Intego Mac Podcast, Intego’s Mac security experts discuss the latest Apple news, security and privacy stories, and offer practical advice on getting the most out of your Apple devices. Be sure to follow the podcast to make sure you don’t miss any episodes.
You can also subscribe to our e-mail newsletter and keep an eye here on The Mac Security Blog for the latest Apple security and privacy news. And don’t forget to follow Intego on your favorite social media channels: ![]()
![]()
![]()
![]()
![]()
![]()
![]()