Syrian Electronic Army Attacks Military Recruitment Site
For the last several months, the Syrian Electronic Army (SEA) has been causing quite a bit of a ruckus,...
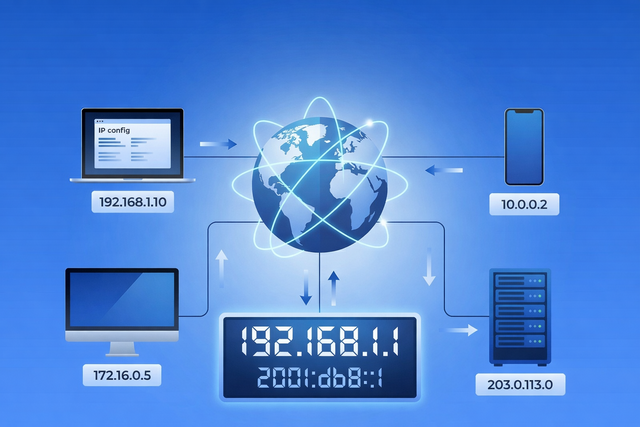
Every time you open a website, stream a video, send an email, or connect to Wi-Fi, your device relies on an IP address. You rarely see it, and most of the time you probably do not think about it. But it plays a quiet, important role in how the internet works. Your IP address helps...

Apple has just released critically urgent security updates—including macOS Sequoia 15.4.1 and iOS 18.4.1—to address two zero-day vulnerabilities that have been actively exploited in...

Macs have a strong security foundation. That’s true — and it’s worth appreciating. But “safer than” doesn’t mean “safe from.” Modern Mac threats don’t...
Is your Mac running slow? Here's how to diagnose and fix performance issues and get your Mac to run faster.
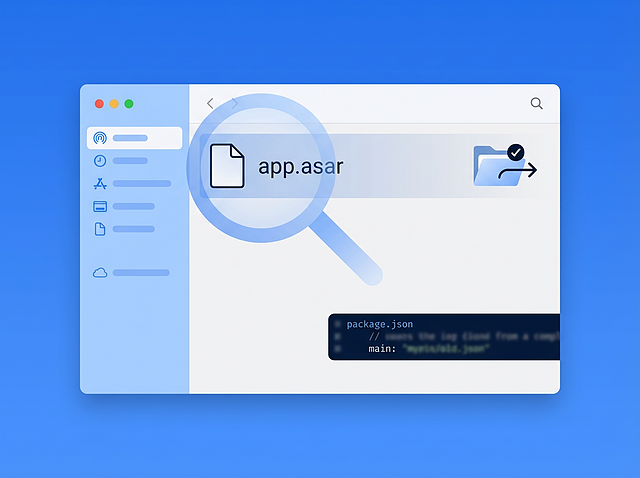
Executive Summary In March 2026, Intego Antivirus Labs investigated a macOS malware campaign delivering the OSX/Amos stealer. During analysis, the infection chain led from stripped Mach-O binaries and heavily obfuscated shell scripts to an unusual final payload that appeared...

For the last several months, the Syrian Electronic Army (SEA) has been causing quite a bit of a ruckus,...
Apple has released an update to its XProtect component of Mac OS X to block certain outdated versions of...
This is apparently the week for people to add interesting things to exploit kits! In case you’ve not already...
For those of you who are fans of the webcomic xkcd, you may recall the suggestion to use passphrases...
In a day filled with news of absolutely baffling decisions (Ben Affleck as Batman, really?!), it should perhaps come...
There is a document floating around with tips written by the NSA for making Macs more secure, which is...
Yesterday, Google’s Chrome team updated its web browser to Chrome version 29. The new Chrome 29.0.1547.57 for Mac (and other...
Once again, fraudulent developers are attempting to fool people into installing their adware by signing their file—which pretends to...
When we last heard from the researchers at Georgia Institute of Technology, they were demonstrating a proof of concept...
This has been an interesting month, with news about hacking a variety of unusual things. People have hacked cars,...