New Sabpab Backdoor Variant Found
Posted on
by
Lysa Myers
Every now and again, we’ll see new variants of popular malware families, especially when those malware families are commonly used in targeted attacks. Today’s new variant is from the Sabpab family that has previously been used to target Tibetan activists. This time it was found on VirusTotal as a Java archive, which acts as a dropper. Once run, it creates a backdoor on the machine that connects to a remote site (www.coremail.info) to await commands.
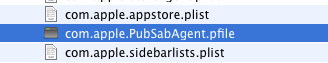
The trojan creates a LaunchAgent in an affected user’s Library folder to persist after reboot. It uses the same file name as previous variants:
- com.apple.PubSabAgent.plist.
It also copies itself inside the user’s Preferences folder using the following file name:
- com.apple.PubSabAgent.pfile
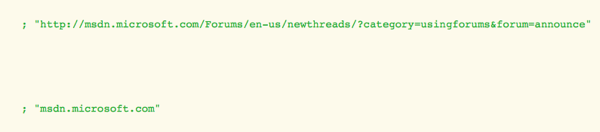
One notable piece of behavior is that this backdoor trojan will take screenshots and post them, encrypted, on Microsoft’s public developer network forums.
This new variant is detected with existing virus definitions. Intego VirusBarrier users with up-to-date virus definitions will detect and remove the SabPab backdoor.