Mac Trojan horse OSX/Koobface.A spreads via Facebook, Twitter – Intego Security Memo
Posted on
by
Peter James
Malware: OSX/Koobface.A
Risk: Low
Description: Intego has discovered a Mac version of the Koobface worm, which spreads via social networks such as Facebook, MySpace and Twitter. Intego’s Virus Monitoring Center has been examining this malware for some time, and given the low level of risk, has not publicly issued information about it. Since other reports have been made public about this malware, Intego has decided to publish this security memo.
Reports have circulated discussing a Trojan horse, but without understanding either the scope or the functioning of this malware. This threat is a Mac OS X version of the Koobface worm, which is served as part of a multi-platform attack via a malicious Java applet. The malware itself is made up of a number of elements, though in order to simplify, we will use the term “Trojan horse” to describe it. (Technically, it propagates as a worm, is installed via a Trojan Horse, and installs a rootkit, backdoor, command and control, and other elements.)
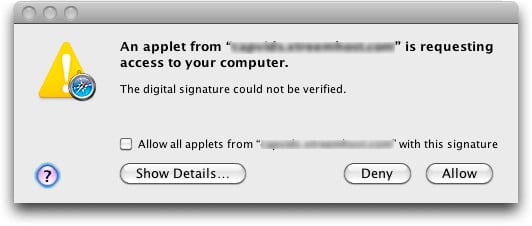
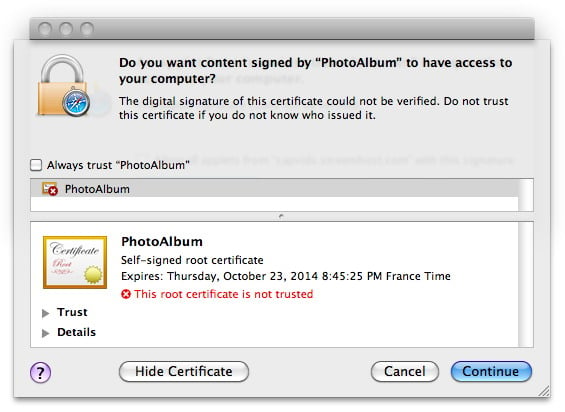
Users first encounter this malware via links on Facebook, MySpace and Twitter, but links can and do exist from other web sites as well. They are taken to malicious web sites in order to view videos, and these sites attempt to load a Java applet. Users are alerted to this via the standard Mac OS X Java security alert.
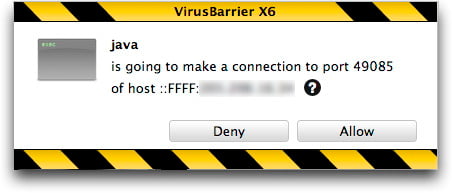
Potentially, if it installs correctly, it functions the same as the Koobface worm running on Windows. It runs a local web server and an IRC server, acts as part of a botnet, acts as a DNS changer, and can activate a number of other functions, either through files initially installed or other files downloaded subsequently. It spreads by posting messages on Facebook, MySpace and Twitter, usually trying to get people to click a link to view some sort of video.
While this is an especially malicious piece of malware, the current Mac OS X implementation is flawed, and the threat is therefore low. However, Mac users should be aware that this threat exists, and that it is likely to be operative in the future, so this Koobface Trojan horse may become an issue for Macs.
Means of protection: The first step is for users who see the Java alert dialog shown above to click Deny; the Java applet will not run, and the malware will not be installed. Second, if a user sees an Installer window display spontaneously, without the user having double-clicked an installation package, they should quit the installer. Intego VirusBarrier X6 and X5 detect and eradicate this malware, which they identify as OSX/Koobface.A, with their current threat filters.

