Apple Issues Emergency Update to Fix Disk Utility Bug in macOS High Sierra
Posted on
by
Jay Vrijenhoek
Two days after macOS High Sierra was released, a vulnerability was disclosed by Brazilian software developer, Matheus Mariano. The vulnerability shows Disk Utility displaying the actual passwords of encrypted volumes when the “Show Hint” button is clicked, rather than the expected password hint. Fortunately, to address this security flaw, Apple has just released macOS High Sierra 10.13 Supplemental Update.
Disk Utility Bug in macOS High Sierra
Apple’s first Supplemental Update for macOS High Sierra addresses a significant Disk Utility bug that exposes the passwords of encrypted Apple File System (APFS) volumes in plain text. The problem occurs when creating encrypted APFS volumes; however, partitioning a drive and encrypting a partition does not show the same vulnerability.
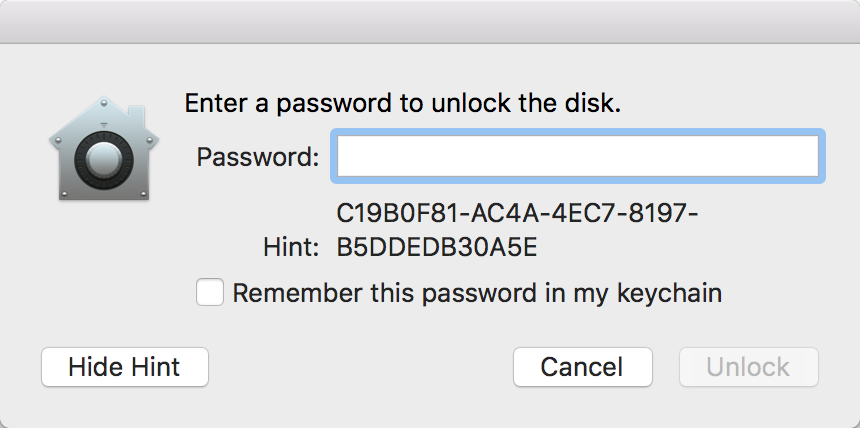
The best way to ensure this vulnerability cannot be exploited on your Mac is to ensure unauthorized users cannot gain access to your system. But what if you have encrypted APFS volumes on an external drive? If someone were to acquire your external drive and connect it to another Mac with macOS High Sierra installed, the Finder will pop-up the “enter password” dialog where the same vulnerability becomes visible. Clicking the “Show Hint” button will reveal the password.
macOS High Sierra 10.13 Supplemental Update
Apple’s macOS High Sierra 10.13 Supplemental Update corrects this behavior on internal drives where the “Show Hint” button now works as it should. However, both the Finder and Disk Utility now no longer have a “Show Hint” button present when it comes to the external drive. That’s one way to ensure the hint doesn’t accidentally display the actual password, but what if someone actually forgot their password and needs the hint?
When we attempt to pull up the hint using Terminal, just a string of garble shows instead.
MacBook-Pro:~ jay$ diskutil apfs listCryptoUsers disk4s2
Cryptographic user (1 found)
|
+-- 0759134B-33BA-4150-8F6C-AC6824846B4A
Type: Disk
Hint: C19B0F81-AC4A-4EC7-8197-B5DDEDB30A5E
The same happens when we connect the external drive back to a pre-supplemental update Mac, the “Show Hint” button is back but the hint shows alphanumeric garble.
The affected volume needs to come into contact with a Mac that has the supplemental update installed, so that it can patch the vulnerability in case that volume is connected to a Mac that does not have the supplemental update installed yet.
Encrypted APFS volumes that were created on a patched Mac will result in the “Show Hint” button appearing when it should, and it shows the actual hint. It looks like Apple was unable to actually repair existing external encrypted APFS volumes, so instead it garbled the output of “Show Hint” in Terminal and simply hid the button in the Finder and Disk Utility. Not an elegant fix, but nonetheless it is a fix.
If you want your hint back, there is only one way to do it: Delete the volume and recreate it using a Mac that has the latest updates installed.
The supplemental update also addresses an issue that allows an application or script to simulate a click on a keychain prompt, thus allowing it access to the stored passwords. This security flaw was discovered by Patrick Wardle — he wrote a proof-of-concept application to demonstrate the vulnerability.
These were two serious vulnerabilities, and makes for a rocky start for the new macOS High Sierra. But with these vulnerabilities fixed by the supplemental update, High Sierra is certainly an OS upgrade I still recommend.
How to Protect Your Mac
If macOS High Sierra shows your password instead of the password hint for an encrypted APFS volume, Apple has created a guide for Mac users to follow and protect your data.
The macOS High Sierra 10.13 Supplemental Update may be obtained from the Mac App Store or Apple’s Software Downloads web site.

