Adobe Patches Second 0-Day Flaw with Flash Player 16.0.0.296
Posted on
by
Derek Erwin
 Over the weekend, on January 24, Adobe Systems released another Flash Player update that includes a fix for a second 0-day vulnerability (CVE-2015-0311) affecting Adobe Flash Player 16.0.0.287 and earlier versions for Mac and Windows.
Over the weekend, on January 24, Adobe Systems released another Flash Player update that includes a fix for a second 0-day vulnerability (CVE-2015-0311) affecting Adobe Flash Player 16.0.0.287 and earlier versions for Mac and Windows.
Adobe previously patched one of the critical 0-Day vulnerabilities with an update to Flash Player 16.0.0.287, but was still investigating reports that a separate exploit exists in the wild. Adobe estimated that they would have a new Flash Player update available during the week of January 26.
Ahead of schedule, Adobe updated its security bulletin (APSA15-01), and said:
UPDATE (January 24): Users who have enabled auto-update for the Flash Player desktop runtime will be receiving version 16.0.0.296 beginning on January 24. This version includes a fix for CVE-2015-0311. Adobe expects to have an update available for manual download during the week of January 26, and we are working with our distribution partners to make the update available in Google Chrome and Internet Explorer 10 and 11.
That’s great news! But how can you check if this manual update is available to you, and securely download and install it? Follow the steps outlined below.
How to Manually Update Flash Player
If you’re unsure what version of Adobe Flash you have running, or how to safely install new updates, you can head over here for some answers to the most common Flash Player installation and update questions.
For the easiest way to check what Flash Player version you have installed on Mac OS X, and update to the latest version, follow these steps:
- Choose the Apple menu icon (upper left corner on OS X desktop)
- Select System Preferences
- Then click on Flash Player at the bottom under Other
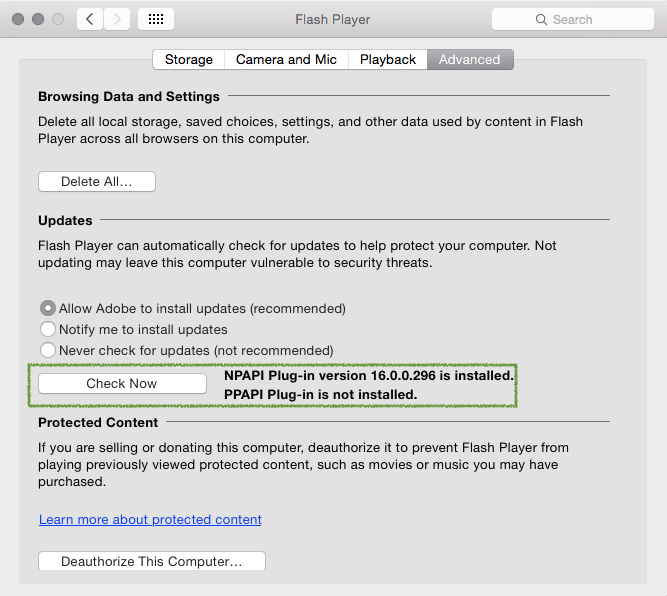
- In the Advanced tab, under Updates, press the Check Now button
If you do not have the latest Flash Player version, you will see a notification that an update is available, and it will ask if you want to download and install it.
- Click Yes, and then follow all of the prompts from Adobe for updating to the latest version of Flash Player
Now you should see that NPAPI plug-in version 16.0.0.296 is installed. This is the latest version of Flash Player and includes patches for both 0-day vulnerabilities (CVE-2015-0310, CVE-2015-0311) affecting earlier Flash Player versions.
By using this method to check for Adobe Flash Player updates, your computer’s internal system will properly check and connect you to Adobe’s website. Because OS X’s internal system bypasses fake websites entirely and makes it far less likely for users to be fooled by phishing websites, this is perhaps the most secure way to update Flash Player.
January 27 Update: Adobe’s security updates for Adobe Flash Player for Windows, Macintosh and Linux are now available for download from Adobe.com. These updates address critical vulnerabilities that could potentially allow an attacker to take control of the affected system, according to Adobe’s security bulletin (APSB15-03).
Affected (out of date) software versions include: Adobe Flash Player 16.0.0.287 and earlier versions, Adobe Flash Player 13.0.0.262 and earlier 13.x versions, and Adobe Flash Player 11.2.202.438 and earlier versions for Linux.
Flash Player 16.0.0.296 for Mac and Windows, and Flash Player 11.2.202.440 for Linux, include patches for the following vulnerabilities:
- These updates resolve a use-after-free vulnerability that could lead to code execution (CVE-2015-0311).
- These updates resolve a double-free vulnerability that could lead to code execution (CVE-2015-0312).
Users of Adobe Flash Player desktop runtime for Windows and Macintosh should update to Adobe Flash Player 16.0.0.296. Users of Adobe Flash Player for Linux should update to Adobe Flash Player 11.2.202.440. Adobe Flash Player installed with Google Chrome, as well as Internet Explorer on Windows 8.x, will automatically be updated to version 16.0.0.296.
Intego VirusBarrier with up-to-date malware definitions detects these Flash Player vulnerabilities as Flash/CVE-2015-0311 and Flash/NuclearEK.