Apple Updates Safari Adobe Flash Player Web Plug-in, Disables All Flash Player Versions Prior to 16.0.0.305
Posted on
by
Derek Erwin
 Yesterday’s Adobe software updates address a recently identified Adobe Flash Player web plug-in vulnerability (CVE-2015-0313) affecting all Flash Player versions prior to 16.0.0.305. In response, Apple has updated the OS X web plug-in blocking mechanism in Safari web browsers, disabling all Adobe Flash Player versions prior to Flash Player 16.0.0.305 and 13.0.0.269.
Yesterday’s Adobe software updates address a recently identified Adobe Flash Player web plug-in vulnerability (CVE-2015-0313) affecting all Flash Player versions prior to 16.0.0.305. In response, Apple has updated the OS X web plug-in blocking mechanism in Safari web browsers, disabling all Adobe Flash Player versions prior to Flash Player 16.0.0.305 and 13.0.0.269.
Apple’s plug-in updates follow Adobe Systems’ release of Adobe Flash Player 16.0.0.305 for Mac and Windows, which includes security updates that address another critical 0-day vulnerability reportedly being used in malvertisement attacks.
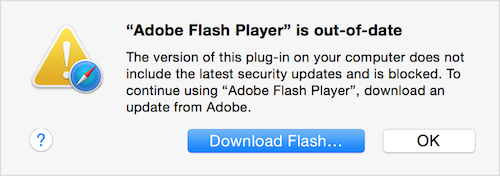
Due to these updates, when attempting to view Flash content in Safari, you may see a “Flash out-of-date” message if your software is outdated and vulnerable to 0-day attacks currently in the wild. The message my look like this:
If you see this message, then you are certainly using an outdated Flash Player version. Click on the indicator, and it will confirm this by displaying the following message:
Unsure if that Adobe Flash popup is safe or a malware threat? Here’s how to verify what Adobe Flash version you have installed and safety get the latest Flash Player version.
To continue using Flash in Safari, you’ll need to update to a later version of Adobe Flash Player. To do so, follow these steps:
First, click the download Flash button. Safari will take you to Adobe’s official Flash Player page where you can obtain the newest software version. Simply follow the instructions Adobe provides you to download and install the latest version of the plug-in.
A second method OS X users can take is to update Flash Player manually, which uses OS X’s internal system to bypass fake websites and makes it far less likely for you to be fooled by phishing sites. Some instructions for how to do this can be found here.
Intego VirusBarrier protects your Mac from these 0-day attacks and detects the threats as Flash/NuclearEK.