New Multi-Platform Backdoor Discovered
Posted on
by
Lysa Myers
Recently a compromised Columbian website was found that is being used to deliver a multi-platform backdoor. The infection is a multi-stage process, which is what allows it to deliver different files depending on what operating system a machine is running.
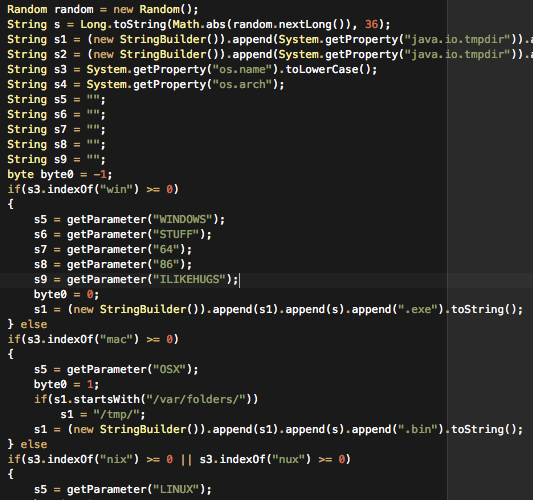
The initial piece of the puzzle is a signed Java applet on the compromised website, which does an operating system check. It then downloads additional components depending on whether the machine is running Windows, Linux or OS X. Once those components are downloaded, it will attempt to install a backdoor Trojan. The functionality of the backdoor Trojan is the same, regardless of which OS it’s running on.
There is one part of the OS X version that is particularly notable: It is a PPC binary only, so it will require Rosetta in order to run on an Intel machine. This is likely to severely limit prevalence of the OS X version.
It’s also interesting to note that the components of this threat are created with readily available hack-tools, namely TrustedSec Social Engineering Toolkit and MetaSploit. This is not something that was cleverly handcrafted, but something that was generated with tools made by other people. And given that the OS X component is not intended for current hardware, it’s likely that the person who planted this threat was not especially technically savvy.
Intego VirusBarrier X6 detects the initial Java applet in this infection chain since July 5th as OSX/SET.gen.