Apple’s New iMac Pro Delivers Enhanced Security with the T2 Chip
Posted on
by
Jay Vrijenhoek

Have you seen the new iMac Pro? What a beast! With a gorgeous 5K display, up to 18 cores of CPU goodness and slick AMD Radeon Vega graphics options, the iMac Pro is a serious contender in the pro market. For those interested in Mac security, what’s particularly noteworthy in Apple’s new iMac Pro is a dedicated chip called the T2.
In Apple’s own words, the T2 does the following:
Introducing the Apple T2 chip, our second-generation custom Mac silicon. By redesigning and integrating several controllers found in other Mac systems — like the system management controller, image signal processor, audio controller, and SSD controller — T2 delivers new capabilities to the Mac. For instance, the T2 image signal processor works with the FaceTime HD camera to enable enhanced tone mapping, improved exposure control, and face detection–based auto exposure and auto white balance. T2 also makes iMac Pro even more secure, thanks to a Secure Enclave coprocessor that provides the foundation for new encrypted storage and secure boot capabilities. The data on your SSD is encrypted using dedicated AES hardware with no effect on the SSD’s performance, while keeping the Intel Xeon processor free for your compute tasks. And secure boot ensures that the lowest levels of software aren’t tampered with and that only operating system software trusted by Apple loads at startup.
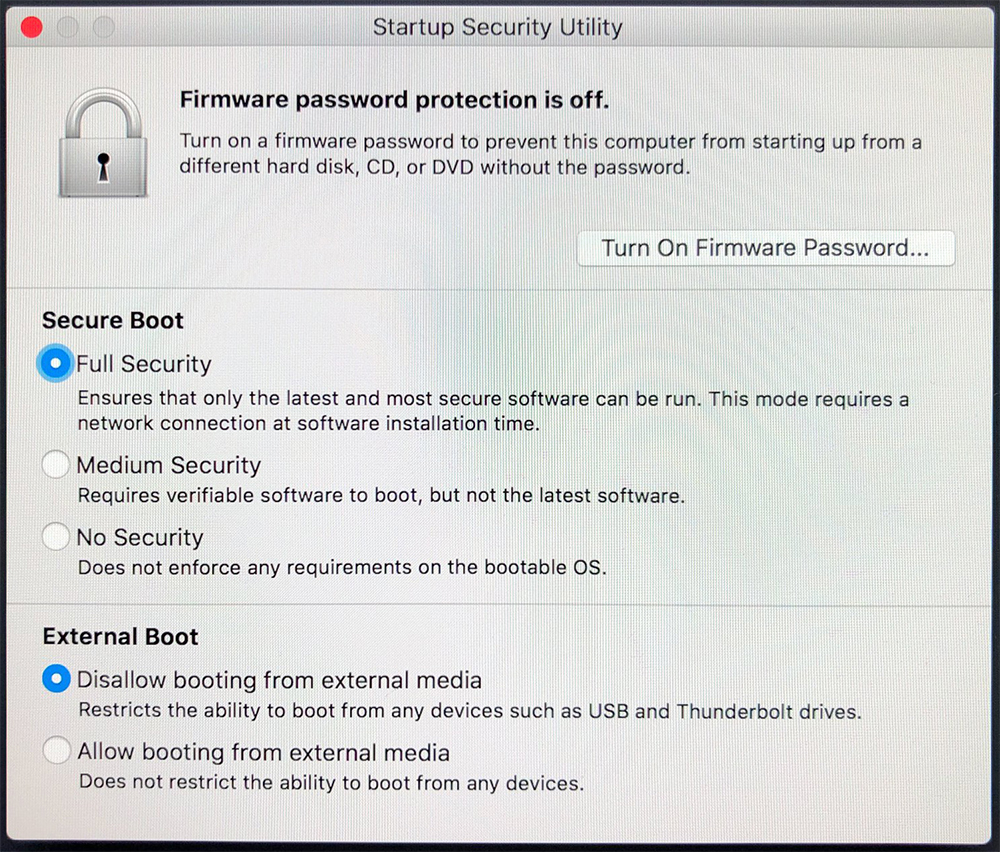
That all sounds pretty good! Encryption is handled by the T2, meaning there is no impact on the CPU. For the end user, the presence of the T2 chip may go unnoticed, but for those who want to tweak the security settings, you can do so through the new Startup Security Utility, found in Recovery.
The new T2 chip is a really cool feature that adds to the security of your Mac, but what about theft and safety protection for your Mac? Someone can still take your iMac Pro, or any Mac for that matter, and walk off with it. How do you secure the Mac itself?
Theft and safety protection for Mac
Over the years, Apple has removed from Macs the one anti-theft security feature it had as everything now is thinner, smaller and lighter. Known as the Kensington cable slot, it allowed you to secure your Mac to a desk or anything that would help make stealing the Mac a lot harder. Here’s a MacBook Pro with that slot:
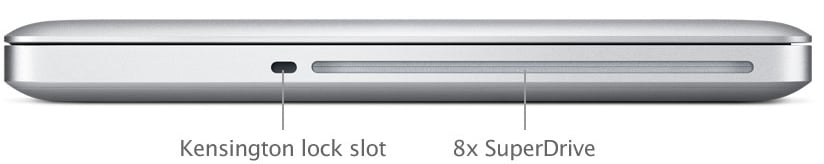
Today the only Mac with that slot still available is the iMac. The Mac Pro, iMac Pro, MacBook, MacBook Air, MacBook Pro and Mac mini no longer have the slot, so what can you do to secure these Macs in place? Let’s explore some options.
iMac Pro
With the Kensington slot gone, there are just two ways of securing a Mac to a desk. You can run a Kensington cable through the hole in the back of the foot or you can secure it at the bottom of the foot. A cable through the hole in the foot is the easiest way, but over time it might scratch the foot — and depending on how the Mac is set up — look less than stellar. Securing the foot in place might look better, but you lose the ability to move the Mac around on your desk.
Using something like the Security Swivel plate will make it a lot harder to steal the Mac, because it is physically screwed into your desk.
Mac Pro
There are brackets available that attach to your Mac Pro, ranging from a simple Kensington slot clip to full base mount with cable management and the Kensington slot. Apple sells one, which you can see here, but you may find it more preferable to get some cable management out of such a solution, too.
If your Mac Pro is in use as a server and/or in an environment where a server rack is available, you may also want to consider mounting it in a rack.
Mac mini
As one of the more easy to steal Macs, locking this down is typically a good idea. Simple solutions are available that consist of enclosing your Mac mini in a bracket, which in turn is screwed to your desk or wall, or secured with a Kensington slot.
The Mac mini is also a popular server; and, as such, it is often used in environments where a rack is available. If you are one of these users, securing your Mac mini in a rack is a good option.
This leaves us with the Macs most likely to be stolen — the MacBook series. Whether they sit on your desk or go with you everywhere, securing these laptops is not easy. You can’t bolt them to a desk, because that defeats the purpose of having a laptop.You can’t mount them in a rack, because it would be super uncomfortable to work on them. You can’t put a bracket on them, because the lid needs to open and close constantly… or can you?
Luckily, when the Retina MacBook Pros came about, some clever people started looking for hardware lock solutions and now several are available.
With the Apple laptops these days being so thin, there is nothing to physically connect an adapter or lock to, and so some manufacturers thought, “Hey! Why not screw the adapters into the Mac using the existing screw holes!” This is in fact a great solution that will anchor the lock adapter firmly to your Mac, making it difficult to steal once secured to a desk or table.
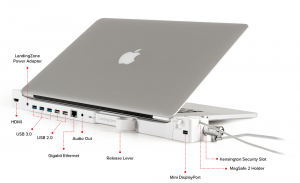
If you want some additional ports on your now almost port-less laptop, a dock might also be an attractive option.
While Apple continues to increase security on an internal hardware and software level, don’t forget to protect the Mac itself. FileVault encryption and the cool, new Apple T2 chip may keep your data secure if your Mac is stolen, but it is preferable to keep your data and your Mac safe and (obviously) in your possession. The above mentioned products are just a small sample of options available out there, so have a look around online and you’ll find one that’s just right for you.
Have something to say about this story? Share your comments below!