Safari 6.0.3 Security Update Fixes WebKit Flaws
Posted on
by
Derek Erwin
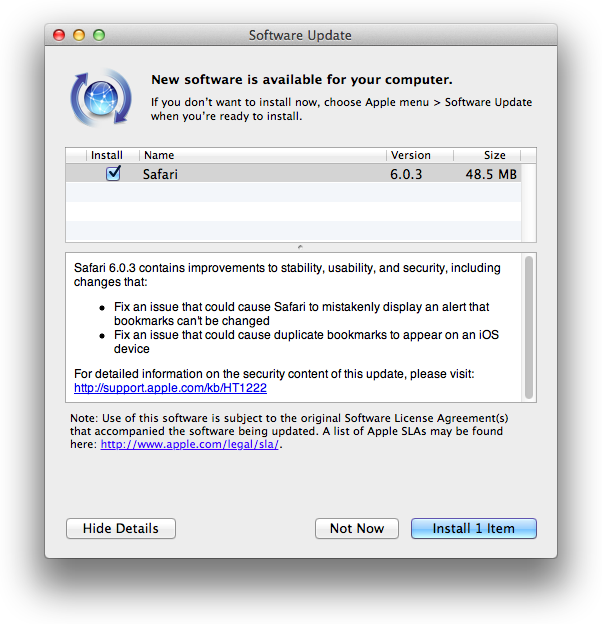
Apple has issued security updates to Safari, updating its web browser to version 6.0.3. The 48.5 MB update to Safari 6.0.3 is available for OS X Lion v10.7.5 and OS X Mountain Lion v.10.8.2, and fixes a number of WebKit flaws and some cross-site scripting issues. The software update coincides with Apple’s released of OS X Mountain Lion v10.8.3 and Security Update 2013-001, which addressed multiple security problems and includes a malware removal tool.
Fixed in the Safari 6.0.3 update are a couple of use-after-free vulnerabilities, multiple memory corruption issues that existed in WebKit, a cross-site scripting issue that existed in the handling of frame elements, and a cross-site scripting issue that existed in the handling of content pasted from a different origin.
Following are details of the two use-after-free vulnerabilities resolved in this software update:
- CVE-2012-2824 : Use-after-free vulnerability in Google Chrome before 20.0.1132.43 allows remote attackers to cause a denial of service or possibly have unspecified other impact via vectors related to SVG painting.
- CVE-2012-2857 : Use-after-free vulnerability in the Cascading Style Sheets (CSS) DOM implementation in Google Chrome before 21.0.1180.57 on Mac OS X and Linux, and before 21.0.1180.60 on Windows and Chrome Frame, allows remote attackers to cause a denial of service or possibly have unspecified other impact via a crafted document.
Also resolved in this update are 13 memory corruption flaws that existed in WebKit, which may lead to an unexpected application termination or arbitrary code execution if visiting a maliciously crafted website. Apple addressed these issues “through improved memory handling.”
Following are details of the WebKit flaws fixed in this update:
- CVE-2013-0948 : CVE-2013-0949 : CVE-2013-0950 : CVE-2013-0951 : CVE-2013-0952 : CVE-2013-0953 : CVE-2013-0954 : CVE-2013-0955 : CVE-2013-0956 : CVE-2013-0958 : CVE-2013-0959 : WebKit, as used in Apple iOS before 6.1, allows remote attackers to execute arbitrary code or cause a denial of service (memory corruption and application crash) via a crafted web site, different vulnerabilities than other WebKit CVEs listed in APPLE-SA-2013-01-28-1.
- CVE-2013-0960 : CVE-2013-0961 : Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution.
Additionally, a cross-site scripting issue was resolved in this update, which existed in the handling of frame elements and may impact users visiting a maliciously crafted website with a cross-site scripting attack. Apple addressed this problem “through improved origin tracking.”
Following are details of CVE-2012-2889:
- CVE-2012-2889 : Cross-site scripting (XSS) vulnerability in Google Chrome before 22.0.1229.79 allows remote attackers to inject arbitrary web script or HTML via vectors involving frames, aka “Universal XSS (UXSS).”
Lastly, another cross-site scripting issue existed in the handling of content pasted from a different origin. “Copying and pasting content on a malicious website may lead to a cross-site scripting attack,” described Apple on the impact of this flaw. Apple addressed this problem “through additional validation of pasted content.”
Following are details of CVE-2013-0962:
- CVE-2013-0962 : Cross-site scripting (XSS) vulnerability in WebKit in Apple iOS before 6.1 allows user-assisted remote attackers to inject arbitrary web script or HTML via crafted content that is not properly handled during a copy-and-paste operation.
Here at Intego, we always recommend updating your software regularly as it is an essential layer of security that helps protect your digital life. Mac users can install the latest updates by choosing Apple menu > Software Update (if prompted, enter an admin password).