Safari 6.1.4 and Safari 7.0.4 Released with Security Bug Fixes
Posted on
by
Derek Erwin
This week, Apple released Safari 6.1.4 and Safari 7.0.4 with security updates that address multiple vulnerabilities. These updates patch 22 security bugs altogether, 21 of which are related to arbitrary code execution.
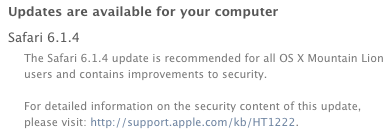
Apple’s Safari web browser updates are available for OS X Lion 10.7.5, OS X Lion Server 10.7.5, OS X Mountain Lion 10.8.5, and OS X Mavericks 10.9.3.
The following vulnerabilities were fixed in the Safari updates:
- CVE-2013-2875, CVE-2013-2927, CVE-2014-1323, CVE-2014-1324, CVE-2014-1326, CVE-2014-1327, CVE-2014-1329, CVE-2014-1330, CVE-2014-1331, CVE-2014-1333, CVE-2014-1334, CVE-2014-1335, CVE-2014-1336, CVE-2014-1337, CVE-2014-1338, CVE-2014-1339, CVE-2014-1341, CVE-2014-1342, CVE-2014-1343, CVE-2014-1344, CVE-2014-1731 : Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution. Multiple memory corruption issues existed in WebKit. These issues were addressed through improved memory handling.
- CVE-2014-1346 : A malicious site can send messages to a connected frame or window in a way that might circumvent the receiver’s origin check. An encoding issue existed in the handling of unicode characters in URLs. A maliciously crafted URL could have led to sending an incorrect postMessage origin. This issue was addressed through improved encoding/decoding.
Mac users running OS X Lion systems can install the Safari 6.1.4 update by choosing Apple menu > Software Update (if prompted, enter an admin password). For users running OS X Mavericks and OS X Mountain Lion systems, Safari 7.0.4 and Safari 6.1.4 may be obtained from the Mac App Store.