Microsoft Office for Mac 14.5.8 Patches Mac Spoofing Vulnerability
Posted on
by
Derek Erwin
Microsoft has released Office for Mac 14.5.8 with security patches for two memory corruption flaws and a Mac spoofing vulnerability. The most severe of the vulnerabilities “could allow remote code execution if a user opens a specially crafted Office file,” said Microsoft in its security bulletin (MS15-116).
This update applies to the following Microsoft software: Office 2011, Office 2011 Home and Business Edition, Word 2011, Excel 2011, PowerPoint 2011, Outlook 2011, Office for Mac Standard 2011 Edition, Microsoft Office for Mac Home & Student 2011, and Microsoft Office for Mac Academic 2011.
The Office for Mac update addresses three security bugs altogether — two of which are related to remote code execution (memory corruption vulnerabilities) and the other related to spoofing. Microsoft summarized the Mac spoofing bug in its security bulletin:
For [the Mac spoofing vulnerability] to be exploited, a user must preview a maliciously crafted email from an attacker where they would unknowingly be redirected to a malicious URL. [In turn], the malicious website could spoof content or be used as a pivot to chain an attack with other vulnerabilities in web services. […] At the time this security bulletin was originally issued, Microsoft is unaware of any attack attempting to exploit this vulnerability.
Details of the vulnerabilities patched in this update are as follows:
- CVE-2015-6038, CVE-2015-6094 : Multiple remote code execution vulnerabilities exist in Microsoft Office software when the Office software fails to properly handle objects in memory. An attacker who successfully exploited the vulnerabilities could run arbitrary code in the context of the current user. If the current user is logged on with administrative user rights, an attacker could take control of the affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. Exploitation of the vulnerabilities requires that a user open a specially crafted file with an affected version of Microsoft Office software. In an email attack scenario an attacker could exploit the vulnerabilities by sending the specially crafted file to the user and convincing the user to open the file. In a web-based attack scenario an attacker could host a website (or leverage a compromised website that accepts or hosts user-provided content) that contains a specially crafted file that is designed to exploit the vulnerabilities. An attacker would have no way to force users to visit the website. Instead, an attacker would have to convince users to click a link, typically by way of an enticement in an email or Instant Messenger message, and then convince them to open the specially crafted file.
- CVE-2015-6123 : A spoofing vulnerability exists when Microsoft Outlook for Mac does not sanitize HTML or treat it in a safe manner. An attacker who successfully exploited this vulnerability could trick a user by redirecting them to a malicious website. The malicious website could spoof content or be used as a pivot to chain an attack with other vulnerabilities in web services.
Microsoft addressed the memory corruption vulnerabilities by correcting how Office handles objects in memory. Additionally, Microsoft addressed the Mac spoofing vulnerability by correcting how Microsoft Outlook validates and sanitizes HTML input.
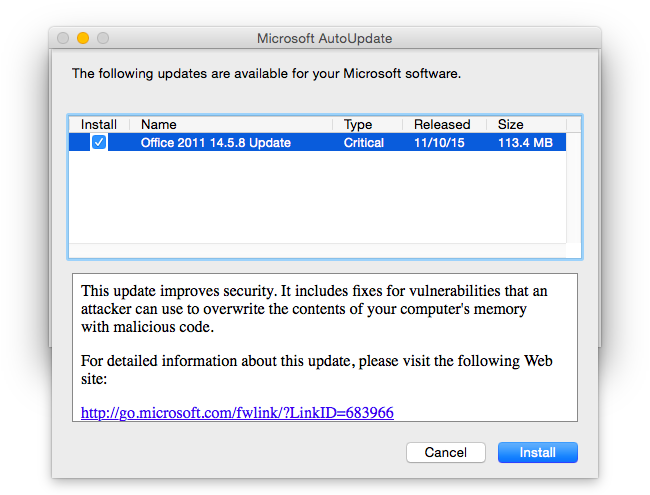
Office for Mac 2011 14.5.8 can be downloaded and installed using the Microsoft AutoUpdate application for Mac, or you can visit the Microsoft Download Center to get the Office for Mac 14.5.8 update (113.4 MB).

