MAC Defender Fake Antivirus Program Targets Mac Users – Intego Security Memo
Posted on
by
Peter James
Malware: OSX/MacDefender.A
Risk: Low; in the wild, but not very widespread for now
Description: Intego has discovered a fake antivirus program called MAC Defender, which targets Mac users via SEO poisoning attacks (web sites set up to take advantage of search engine optimization tricks to get malicious sites to appear at the top of search results). When a user clicks on certain links after performing a search on a search engine such as Google, they are sent to a web site that displays a fake Windows screen with an animated image showing a malware scan; a window then tells the user that their computer is infected. After this, JavaScript on the page automatically downloads a file. The file downloaded is a compressed ZIP archive, which, if a specific option in a web browser is checked (“Open ‘safe’ files after downloading” in Safari, for example), will open. The file is decompressed, and the installer it contains launches presenting a user with the following screen:
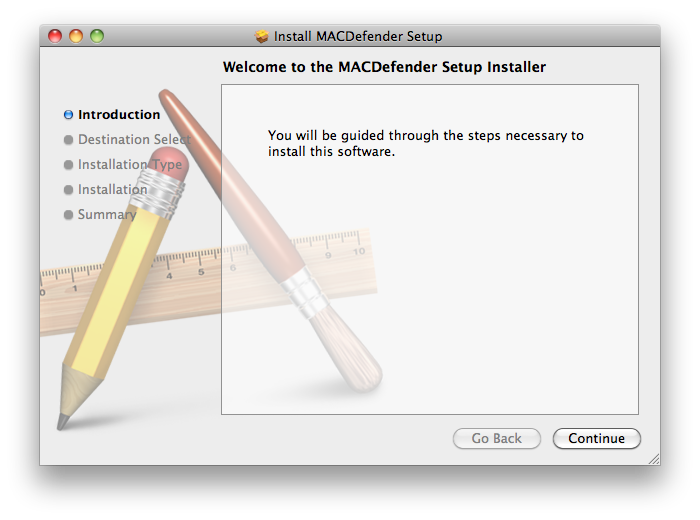
If the user continues through the installation process, and enters an administrator’s password, the software will be installed.
VirusBarrier X6’s real-time scanner detects this installer when it is downloaded:
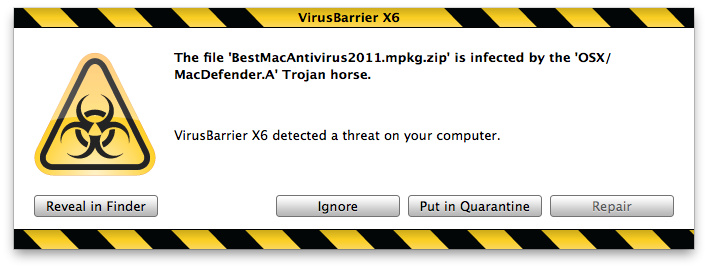
And VirusBarrier X6’s Web Threats protection detects pages that serve this installer:

After installation, a program called MAC Defender launches, displaying its interface, and adding a menu item to the Mac OS X menubar (the small, orange shield icon in the image below, which becomes red when the program “finds” viruses):
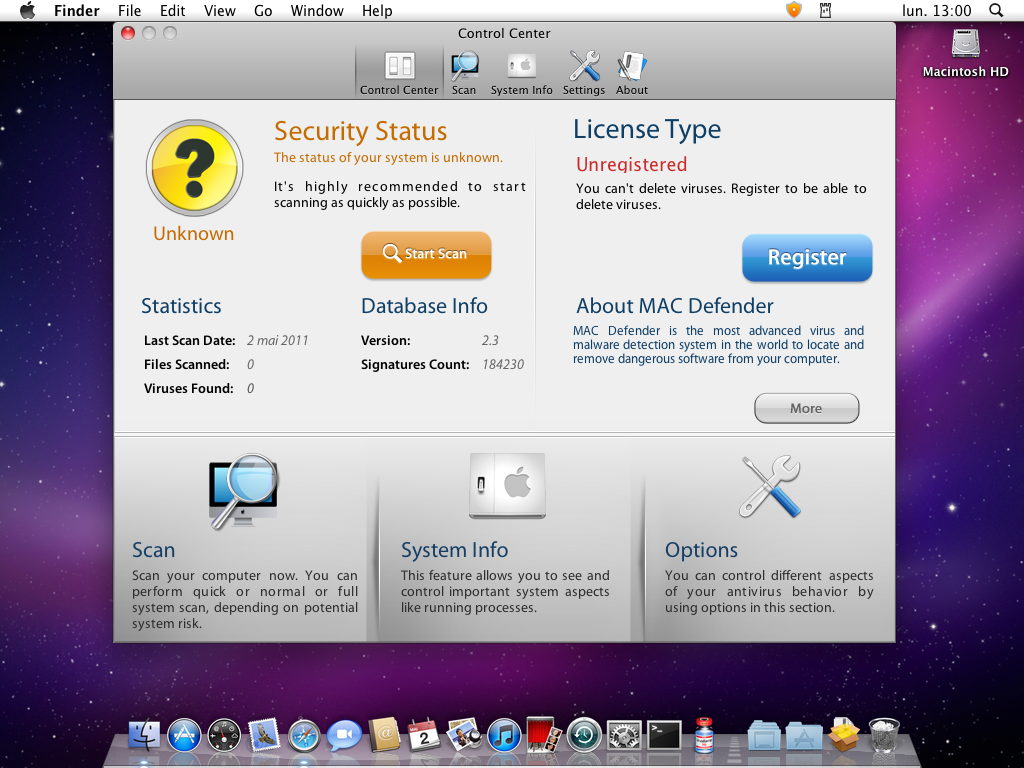
Upon installation, the application adds itself to the user’s Login Items, so it will relaunch each time the user logs in or starts up their computer. The application itself cannot be quit easily, as there is no Dock icon.
(One thing to point out is that, in the past, these types of sites—very common vectors of Windows malware—only delivered Windows .exe applications. The fact that such a site is providing a Mac rogue antivirus is new, and extremely rare. While the site itself still shows a fake Windows screen, the rogue antivirus itself is a well-designed Mac application.)
This application is very well designed, and looks professional. There are a number of different screens, and the grammar and spelling are correct, the buttons are attractive, and the overall look and feel of the program give it a professional look. It will occasionally display alerts, telling users that viruses are found:
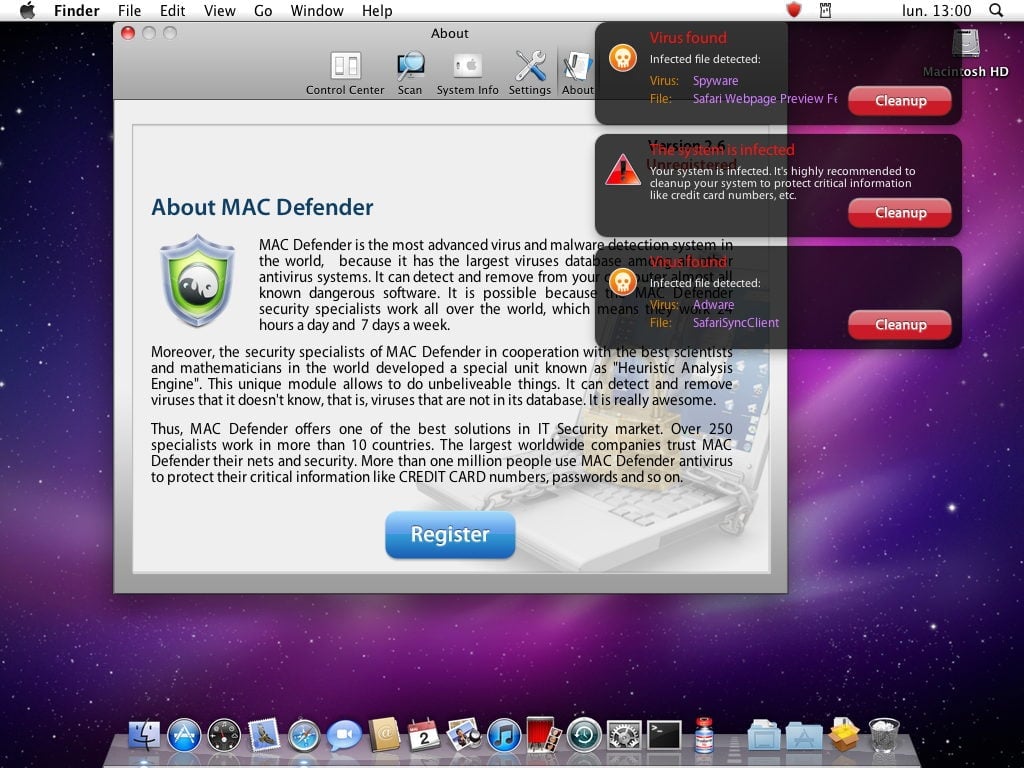
MAC Defender also opens web pages for pornographic web sites in the user’s web browser every few minutes. This is most likely to make users think that they are infected by a virus, and that paying for MAC Defender will relieve them of the problem.
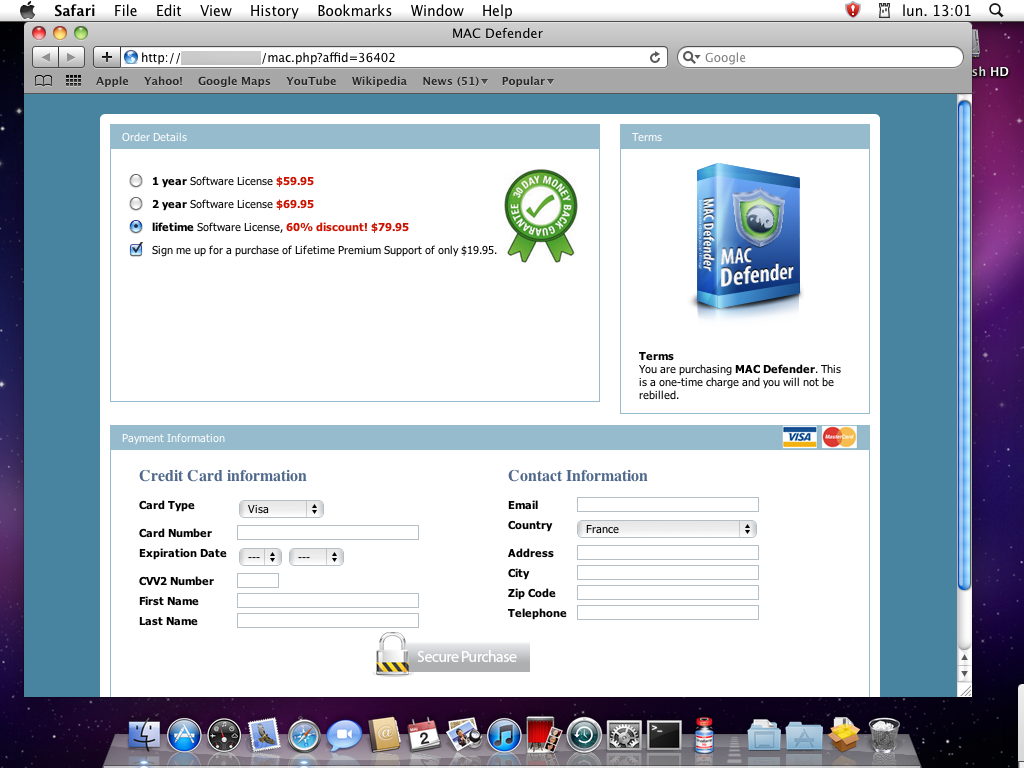
Clicking the Register button on the About screen takes users to a web page where they can purchase a license for the program: either a 1-year, 2-year, or lifetime license. Users are asked to provide a credit card number, and the web page used is not secure. The scam here is to charge users for a program that doesn’t do anything; the virus warnings presented are bogus, and after paying, they no longer display, so users think the program has done something useful. It is also possible that these credit card numbers, given via an unsecure web page, could be used for other purposes.
Means of protection: It is essential that users who unexpectedly see an installation screen, as shown at the beginning of this security memo, do not go further and install the application. This installation screen is the normal Mac OS X Installer screen, but this should only display when you expect to install software.
Second, it is important to uncheck the “Open ‘Safe’ files after downloading” option in Safari, or similar options in other browsers. If a browser asks you if you want to run an installer when you did not expect to download an installer, always click the No or Cancel button.
VirusBarrier X5 and VirusBarrier X6 (www.intego.com/virusbarrier/) protect users from this malware with malware definitions dated May 2, 2011 or later. VirusBarrier X5’s and VirusBarrier X6’s real-time scanner will detect the file when it is downloaded, and its Web Threats protection blocks web pages containing this malicious code. VirusBarrier Express and VirusBarrier Plus, available exclusively from the Mac App Store, detect this malware with malware definitions dated May 2, 2011 or later, but these programs do not have a real-time scanner, due to limitations imposed by the Mac App Store; users should scan their Macs after they have updated to the latest malware definitions.
UPDATE: May 5, 2011 – Intego has discovered several new variants of this fake antivirus. See this post for more information, and for a video showing how the fake antivirus is installed and how it functions.

