Apple Updates Safari for Mac, Closes Multiple Security Holes in WebKit
Posted on
by
Derek Erwin

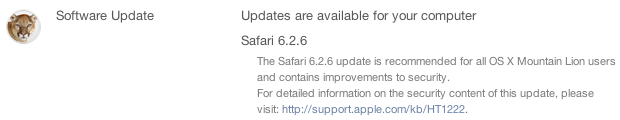
Just yesterday, Apple released fixes for multiple security flaws that affect its web browser engine WebKit in Safari 8.0.5, Safari 7.1.5, and Safari 6.2.5 and earlier versions. The new Safari for Mac versions include Safari 8.0.6 for OS X Yosemite, Safari 7.1.6 for OS X Mavericks, and Safari 6.2.6 for OS X Mountain Lion.
Apple’s Safari 8.0.6, Safari 7.1.6, and Safari 6.2.6 updates mitigate the following vulnerabilities:
- CVE-2015-1152, CVE-2015-1153, CVE-2015-1154 : Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution. Multiple memory corruption issues existed in WebKit. These issues were addressed through improved memory handling.
- CVE-2015-1155 : Visiting a maliciously crafted website may compromise user information on the filesystem. A state management issue existed in Safari that allowed unprivileged origins to access contents on the filesystem. This issue was addressed through improved state management.
- CVE-2015-1156 : Visiting a malicious website by clicking a link may lead to user interface spoofing. An issue existed in the handling of the rel attribute in anchor elements. Target objects could get unauthorized access to link objects. This issue was addressed through improved link type adherence.
All too often people delay or forget to update browsers. Such updates are an important layer of security as spyware can take advantage of vulnerabilities in third-party software, including web browsers. Make sure your browsers and browser plugins are all up-to-date and protected against all known flaws to keep your system safe.
Mac users can install the latest Safari versions by choosing Apple menu > Software Update (if prompted, enter an admin password), or the updates may be obtained from the Mac App Store.

