Caution: Mac-specific Hack Tool Mettle Discovered
Posted on
by
Jay Vrijenhoek
Security researchers have discovered a Mac specific implementation of the hacking tool Meterpreter, called Mettle. As described by its creator, “[Mettle] can run on the smallest embedded Linux targets to big iron, and targets Android, iOS, macOS, Linux, and Windows, but can be ported to almost any POSIX-compliant environment.”
Meterpreter is a tool packaged together with the popular Metasploit Framework, a versatile penetration testing software suite that can be used to test a network’s security defenses, expose vulnerabilities and exploit them, if desired.
Metasploit is very useful software for those who wish to harden and defend a network; unfortunately, it is an equally useful tool for those who wish to break into a network and cause havoc. Meterpreter is one of the payloads that Metasploit uses, which allows a user to execute a number of commands on a target system.
What is the infection vector?
This can really be anything from a fake Adobe Flash Player that drops this backdoor, an “evil maid” attack in which someone with physical access installs it, or a hack.
If Mettle ends up on your Mac and is used in conjunction with MetaSploit, chances are the prime suspect is phishing or spear phishing. There is a possibility that your IT staff used this as part of a test for system and network security, so if your Mac falls under the care of such staff, check with them right away. If this came from them, they’ll probably be happy to see you discovered it. If it did not come from them, they’ll want to investigate immediately to see if there has been a data breach.
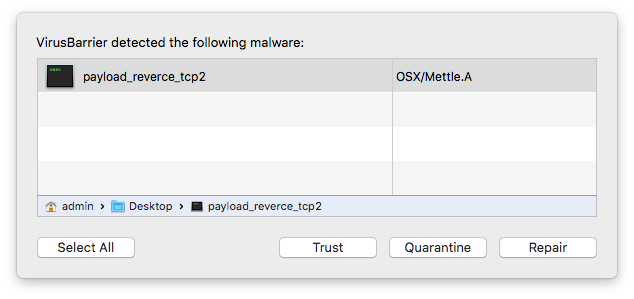
About OSX/Mettle.A
Mettle is a Mach-O (short for Mach object file format), meaning it was developed specifically for the Mac. This can be a port from another platform, similar to what we saw with Snake malware. This Mach-O is the exploit layer used to gain access to a target system. Intego VirusBarrier identifies and eradicates this threat as OSX/Mettle.A.
Once access is provided by Mettle, the attacker can perform a wide range of tasks, including the ability to upload and download files, log keystrokes, search for files, execute scripts, take screenshots, access the camera, and much more. Because users can write their own scripts for Mettle, its functionality is only limited by the skills of the user who controls it.
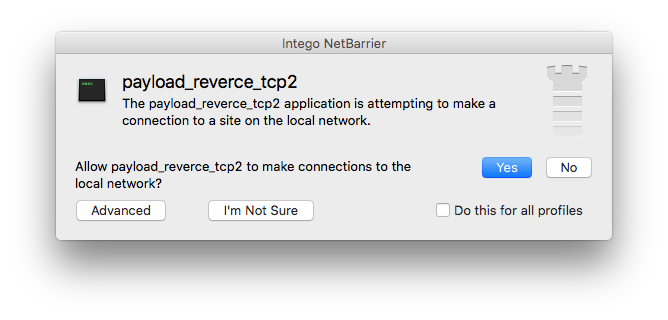
Meterpreter and Mettle are difficult to detect on a system as it creates no files on the hard disk. It runs completely from memory (RAM) and attaches itself to a process. Unless you are looking for it, you probably won’t know it’s there. Your Mac’s memory is not scanned by antivirus software, so you may wonder, how can Intego detect it?
If Mettle finds its way onto your system as part of other malware—if it touches your hard drive in any way—it will be picked up immediately by VirusBarrier’s Real-Time scanner.
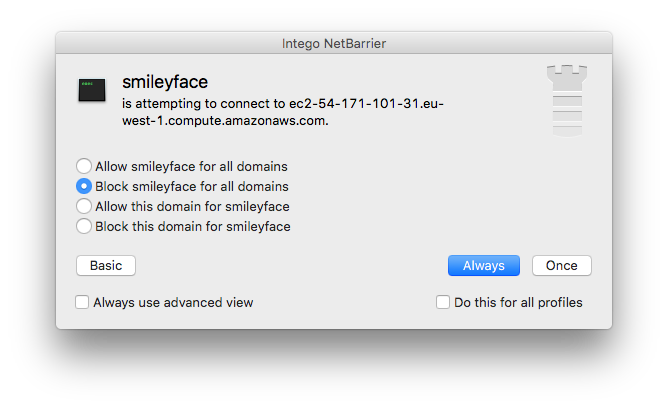
If Mettle is executed from memory, while antivirus software would not detect it, Intego NetBarrier (two way firewall) will detect the network activity when Mettle opens the backdoor and waits for commands to come in from a remote server. (This highlights the importance of having a layered approach to security.)
Upon inspecting Mettle’s behavior, we found that it was attempting to receive commands from an Amazon hosted server.
While there are legitimate purposes for tools like Metasploit, the potential for this security suite to be turned against you, rather than being used to help you, is unfortunately far greater. Mettle was not created with a malicious purpose in mind, in fact, Rapid7 is a big player in the security industry that has a range of services to help improve security for organizations. However, just because Mettle was created with good intentions does not mean it won’t be used with bad intentions.
Samples used for analysis:
08ae98aab06477f1d2622ec7f2c590ec17b8582308c657db51782d6d5963ec27
58a80594603607ed330049187085b84f15513b96b2335f588ca1b28dc2c15576