Apple Patches Major Data Security Flaw with iOS Update
Posted on
by
Derek Erwin
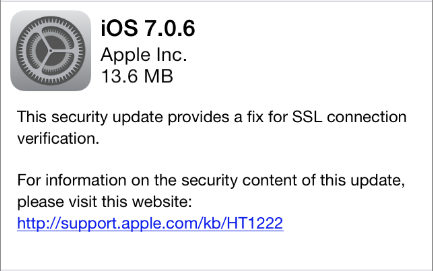
Apple has patched a major data security flaw with its latest iOS update. The tech company pushed two software updates for iOS users with the release of iOS 6.1.6 for iPhone 3GS and iOS 7.0.6 for iPhone 4 and later. These updates provide “a fix for SSL connection verification,” according to the update notices.
The iOS 6.1.6 update is available for: iPhone 3GS, iPod touch (4th generation).
The iOS 7.0.6 update is available for: iPhone 4 and later, iPod touch (5th generation).
Both iOS 6.1.6 and iOS 7.0.6 updates patch the same vulnerability (CVE-2014-1266), from which an attacker with a privileged network position may capture or modify data in sessions protected by SSL/TLS. Apple also released Apple TV 6.0.2 with fixes for the same SSL flaw.
Apple described the vulnerability as follows:
CVE-2014-1266 : Secure Transport failed to validate the authenticity of the connection. This issue was addressed by restoring missing validation steps.
Apple released the patch for iOS and Apple TV on Friday. News of the update quickly spread over the weekend after several researchers reported that the flaw also affected OS X 10.9 Mavericks and possibly other OS X versions. InfoWorld mentioned, “On OS X, the flaw is likely limited to SSL connections over unsecured Wi-Fi networks, though only in Safari.” An Apple spokesperson said that a fix for OS X is due “very soon.”
InfoWorld further explained the impact of this vulnerability:
[C]ommunications sent over unsecured Wi-Fi hot spots could be intercepted and read while unencrypted, potentially exposing user password, bank data, and other sensitive data to hackers via man-in-the-middle attacks. Secured Wi-Fi networks, such as home and business networks with encryption enabled, are not affected.
With Macs likely still affected by this vulnerability, Dan Goodin over at Ars Technica offered some recommendations for OS X users:
For the time being, people using Macs should avoid using public networks, a step that can thwart many criminal eavesdroppers but will do little to prevent surveillance by the National Security Agency and other state-sponsored spies. Because the Google Chrome and Mozilla Firefox browsers appear to be unaffected by the flaw, people should also consider using those browsers when possible, although they shouldn’t be considered a panacea.
From the WSJ, this video does a great job summarizing what Mac users need to know about Apple’s security flaw:
All iOS users should immediately update their iOS devices to versions 7.0.6 or 6.1.6, which we recommend doing so over a secure-private network. Apple TV users should also update their software immediately.
Mac users, in the meantime, can check to see if your computer is affected. As pointed out by David Morgenstern at ZDNet:
You can test whether your device is affected at gotofail.com or imperialviolet.org:1266. At this writing, Mac OS X 10.9, including current seeds, is still vulnerable. iOS 5 and Mac OS X 10.8 never had the bug. It’s fixed in iOS 6.1.6 and iOS 7.0.6.
Apple iOS users can download and install the iOS 6.1.6 and iOS 7.0.6 updates through iTunes or through your device Settings (select General > Software Update).