New OS X Malware: Another Tibet Variant Found
Posted on
by
Lysa Myers
Things have been relatively quiet lately from the authors of the Tibet family of malware, but another variant was found last night on the Virus Total website, which is a site used by security researchers to share malware samples. Before last night, the last variant was found just over a year ago, and was already detected by Intego VirusBarrier’s existing virus definitions as OSX/Tibet.C.
This time, the attack arrives via a Java applet on a web site. This drops a Java archive with the backdoor and launches it without user interaction, by way of a Java vulnerability. When installed, it creates a backdoor to the affected computer, which allows an attacker to view and access files on the computer as well as running commands. The malware uses recently patched Java vulnerabilities CVE-2013-2465 and CVE-2013-2471. If you’ve not yet updated, now would be a great time to do so.
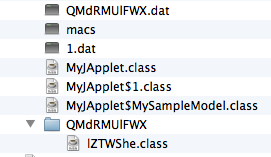
The archive file has the following contents:
The new Tibet malware variant creates the following files when installed:
- /Library/Audio/Plug-Ins/Components/AudioService
- /Library/LaunchAgents/com.apple.AudioService.plist
The LaunchAgent enables the malware to start after reboot. The backdoor itself is what’s copied as “AudioService.” It contacts a C&C server in China (mail.tbnewspaper.com) to receive commands.
Intego VirusBarrier with current malware definitions protects Mac users against this malware as OSX/Tibet.D. This is considered to be a low-risk threat at this time as it’s not known to be affecting users.