New Flashback Variant Changes Tack to Infect Macs
Posted on
by
Peter James
Intego has discovered a new variant of the Flashback malware, Flashback.N, which has been changed since our blog post showing how Flashback used Twitter as a command and control center. This new variant changes the files it installs and their location: the files we specified in our blog post of February 23 are no long used. In addition, it uses a different social engineering trick, if it fails to install itself via the Java vulnerabilities that we mentioned in that blog post.
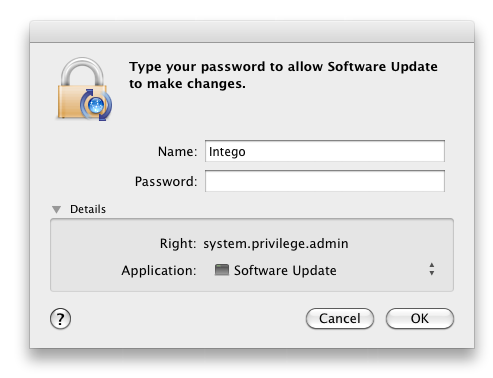
The new version of the Flashback malware installs after Mac users visit infected web sites. In Intego’s tests, the installation procedure was somewhat odd, as web sites display a spinning gear for some time, before finally displaying a password request dialog pretending to be from Software Update, Apple’s tool for downloading and installing software.
Flashback forces Safari to quit, installs a file at /tmp/Software Update, then installs two invisible files in Safari’s resources, taking advantage of the root rights it obtained when the user entered his or her administrator’s password.
Next, Flashback injects code in Safari when the browser is launched. The .COAAShipPlotter.png file is the malware, and the .COAAShipPlotter.xsl is the file that injects code in Safari, in conjunction with Safari’s info.plist file which has been modified.
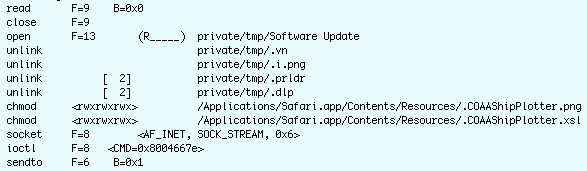
After this, the malware performs the same operations as previously, sniffing network traffic in search of user names and passwords. Note that these file names may change.
In addition, it is now clear that the Flashback malware has been created by the same people who were behind the Mac Defender fake antivirus which infected many Mac users beginning in May, 2011.
Websense Security Labs published a blog post pointing out that tens of thousands of WordPress blogs were infected by code that redirected them to web sites serving fake antiviruses, including Mac Defender. Sucuri Security narrowed this down to a plugin called ToolsPack, which installs a backdoor on servers where it is installed. But David Dede of Sucuri Security said, “Many of the blogs compromised in these recent attacks were running outdated WordPress versions, had vulnerable plug-ins installed or had weak administrative passwords susceptible to brute force attacks.”
Intego has examined some of the WordPress blogs infected with this code and found that they redirect Mac users to sites that serve the Flashback malware. It is important that people running WordPress sites ensure that their installation is up to date, that they have secure passwords, and that they especially don’t use this ToolsPack plugin.
Regarding this new variant of the Flashback malware, it is important to make sure to only enter passwords when you have performed an action that would require one. Using Software Update is a bit sneaky, because if you have Software Update set to check for updates automatically, it may unexpectedly display a dialog when it has found new updates, but the dialog it presents is different, and looks like this:
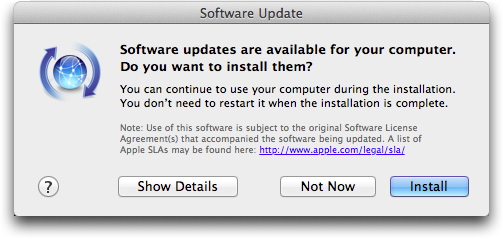
After you click on Install, you may see a password request, depending on the type of update being installed.
Intego VirusBarrier X6 with current malware definitions protects against this new version of the Flashback malware; Intego did not need to update its malware definitions to detect this new variant.